State, local, tribal, and territorial (SLTT) governments have been warned they are being targeted by Business Email Compromise (BEC) scammers. In a March 17, 2021 Private Industry Notification, the Federal Bureau of Investigation (FBI) explained it has observed an increase in BEC attacks on SLTT government entities between 2018 and 2020. Losses to these attacks range from $10,000 to $4 million.
BEC attacks involve gaining access to an email account and sending messages impersonating the account holder with a view to convincing the target to make a fraudulent transaction. The email account is often used to send messages to the payroll department to change employee direct deposit information or to individuals authorized to make wire transfers, to request changes to bank account details or payment methods.
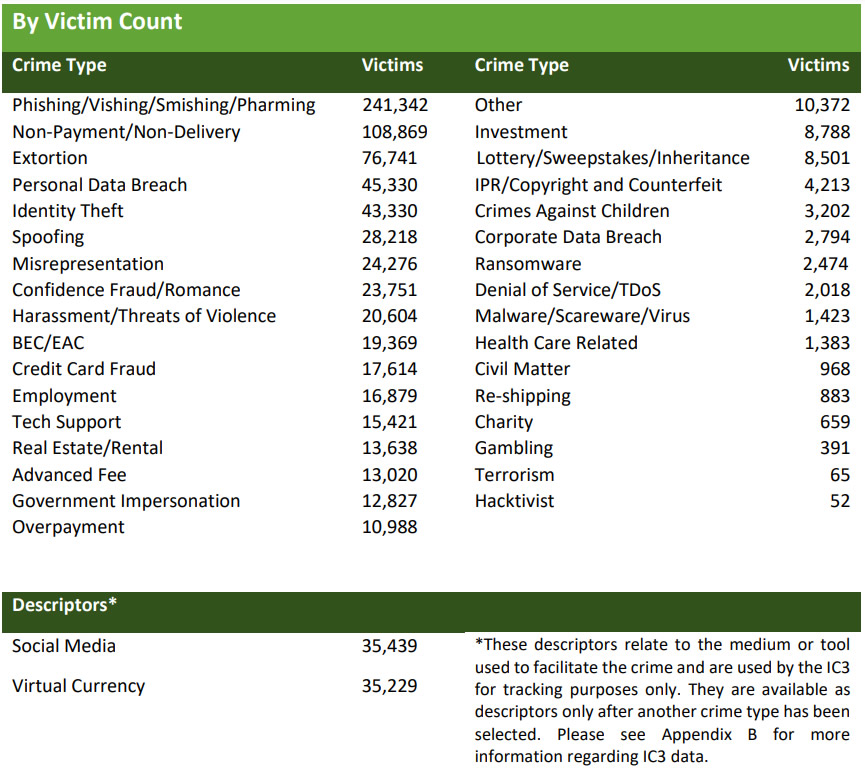
In 2020, the FBI’s Internet Crime Complaint Center (IC3) was notified about 19,369 BEC attacks and losses of almost $1.9 billion were reported. In July 2019, a small city government was scammed out of $3 million after receiving a spoofed email that appeared to be from a contractor requesting a change to their payment method. In December 2019, the email account of a financial coordinator of a government agency of a US territory was compromised and used to send 146 messages to government entities with financial transaction instructions. Many of these requests were queried via email, and the attacker was able to intercept and respond to those messages. In total, $4 million was transferred to the attacker’s account.
In addition to the financial losses, the attacks impair operational capabilities of SLTT government entities, cause reputational damage, and can also result in the loss of sensitive information such as PII, banking information, and employment data.
BEC scammers can easily research targets and can discover SLTT operating information and information about vendors, suppliers, and contractors from public sources. Gaining access to the email accounts is straightforward as the target’s email address is easy to locate, and phishing kits can be purchased cheaply on the darknet for harvesting credentials.
Once an email account is compromised, the writing style of the account holder is copied, and message threads are often hijacked. The scam could involve multiple messages where the target believes they are communicating with the genuine account holder, when they are communicating with the scammer.
The FBI warns that BEC scammers often go for low hanging fruit, and most likely target SLTT government entities with inadequate cybersecurity protocols and take advantage of SLTT government entities that fail to provide sufficient training to the workforce. The move to remote working due to the pandemic has also made it easier for the scammers.
In 2020, CISA conducted phishing simulations of SLTT government entities. Across 152 campaigns consisting of around 40,000 messages, there were around 5,500 unique clicks of fake malicious links, which is a click rate of 13.6%. Such a high click rate suggests security awareness training is failing to teach employees about the risk of email-based attacks and highlights the need for “defense in depth mitigations.”
The FBI suggests ensuring all members of the workforce receive security awareness training, are told about BEC attacks and how to identify phishing emails and fraudulent emails. Employees must be instructed to carefully check email requests for advance payments, changes to bank account information, or requests for sensitive information. Policies and procedures should be implemented that require any bank account change or transaction request to be verified by telephone using a verified number, not information supplied in emails.
Additional measures that should be considered include phishing simulations, multi-factor authentication on email accounts, blocking of automatic email forwarding, monitoring email Exchange servers for configuration changes, adding banners to emails arriving from external sources, and using email filtering services.
Further measures that can be implemented to prevent and detect BEC attacks are detailed in the FBI Alert.
The post FBI Warns of Increase in Business Email Compromise Attacks on Local and State Governments appeared first on HIPAA Journal.