The Government Accountability Office (GAO) has recommended that the Department of Health and Human Services (HHS) establish a feedback mechanism to improve the effectiveness of its data breach reporting process.
The Health Information Technology for Economic and Clinical Health (HITECH) Act, part of the American Recovery and Reinvestment Act of 2009, called for the Secretary of the HHS to create and maintain a list of data breaches involving the unsecured protected health information of 500 or more individuals on its website.
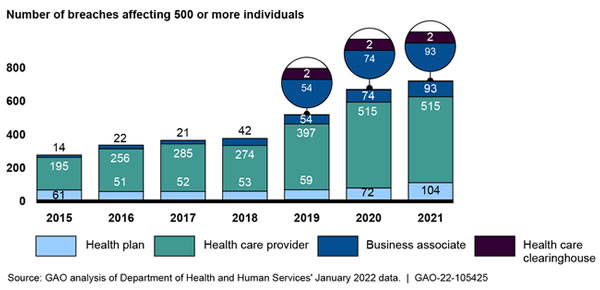
The HHS’ Office for Civil Rights (OCR) Breach Portal includes breaches of the personally identifiable protected health information (PHI), such as unauthorized access and disclosures, exposures, and the loss and theft of PHI. The number of reported data breaches has been increasing each year, with 2021 seeing 714 data breaches of 500 or more records reported to OCR.
GAO explained in its report that between 2015 and 2021, the number of individuals affected by healthcare data breaches at healthcare providers, health plans, healthcare clearinghouses, and business associates of those entities has ranged from 5 million to 113 million each year.
OCR is the main enforcer of compliance with the Health Insurance Portability and Accountability Act (HIPAA). OCR investigates data breaches and complaints about potential HIPAA violations and seeks to establish whether the HIPAA Rules have been violated. To date, OCR has imposed 110 financial penalties on HIPAA-regulated entities that have been determined to have violated the HIPAA Rules.
In January 2021, the HITECH Act was amended to require OCR to consider the ‘recognized security practices’ that were continuously in place for the 12 months previously when making determinations about actions to take against HIPAA-regulated entities that have experienced breaches of PHI. OCR sought feedback from the public on the implementation of recognized security practices and is due to finalize that process this summer.
GAO said it was asked to conduct a review of the breach reporting process, determine the extent to which the HHS had established a review process to assess whether covered entities had implemented recognized security practices, and determine the extent to which improvements can be made related to the breach reporting requirements of the HHS.
As part of that process, GAO reviewed privacy and information security laws; analyzed HHS documentation, policies, and procedures; interviewed cognizant OCR officials; and surveyed HIPAA-regulated entities.
GAO said in its report that OCR has been charged with the development and management of the breach reporting process but has not established a method to allow HIPAA-regulated entities to provide feedback on the breach reporting process. Without such a mechanism, HIPAA-regulated entities could face challenges during the breach reporting process and have no clear way of reporting those issues to OCR. GAO has recommended such a process be established, as this would help OCR to improve aspects of the breach reporting process.
The HHS concurred with the single GAO recommendation and explained that OCR would establish a mechanism for regulated entities to provide feedback on the breach reporting and investigative process. This would be achieved by adding language and contact information to the confirmation emails that HIPAA-regulated entities receive when they report data breaches through the HHS Breach Portal. The HHS said it will also be issuing procedures to OCR’s regional offices that require them to regularly review and address emails received about the breach reporting process.
The post GAO: HHS Should Establish Mechanism for Obtaining Feedback on HIPAA Data Breach Reporting Process appeared first on HIPAA Journal.

