A final rule updating the HIPAA Security Rule is due for release as early as May 2026. According to HHS/OCR, the modifications to the Security Rule will improve cybersecurity in the health care sector by strengthening requirements to safeguard electronic protected health information to prevent, detect, contain, mitigate, and recover from cybersecurity threats. In Spring 2025, OCR released a timetable suggesting a May 2026 release, although the final rule will likely be delayed. If OCR opts to release a final rule implementing all changes proposed in its January 2026 Notice of Proposed Rulemaking (NPRM), it will have a major impact on business associates of HIPAA-covered entities.
For more than two decades, the HIPAA Security Rule has set a baseline for cybersecurity to safeguard electronic protected health information (ePHI). Prior to its release in 2003, there were no standards for cybersecurity, although at the time, adoption of electronic health records was far from widespread. The standards of the HIPAA Security Rule have helped to ensure that ePHI, and the systems used to store, process, and transmit that information, have appropriate safeguards to protect against unauthorized access; however, standards that were reasonable and appropriate in the early 2000s are no longer sufficient to protect against the barrage of attacks from nation-state actors and cybercriminals, the increasing sophistication of intrusion and lateral movement techniques, and the emerging threat of AI-assisted attacks.
New Mandatory Cybersecurity Rules for HIPAA Business Associates
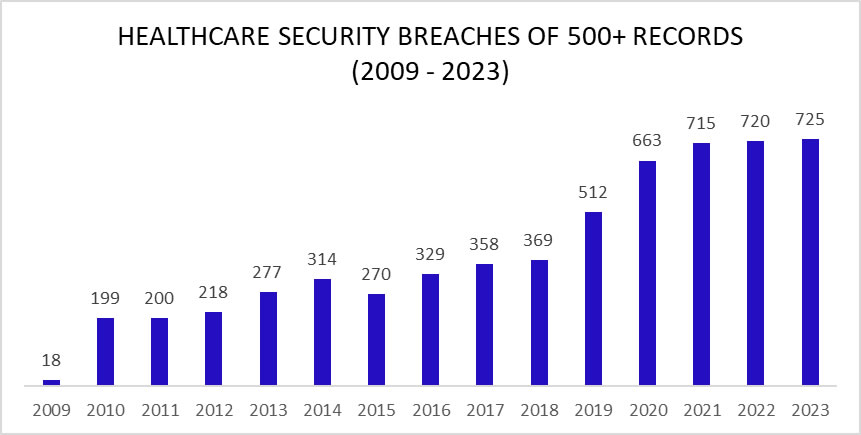
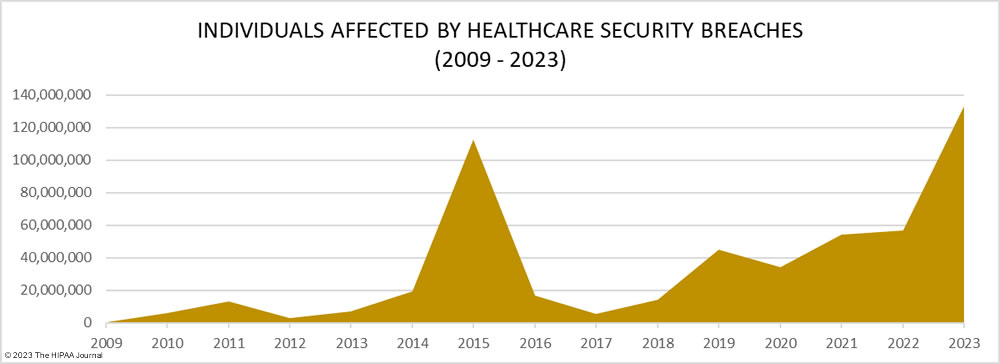
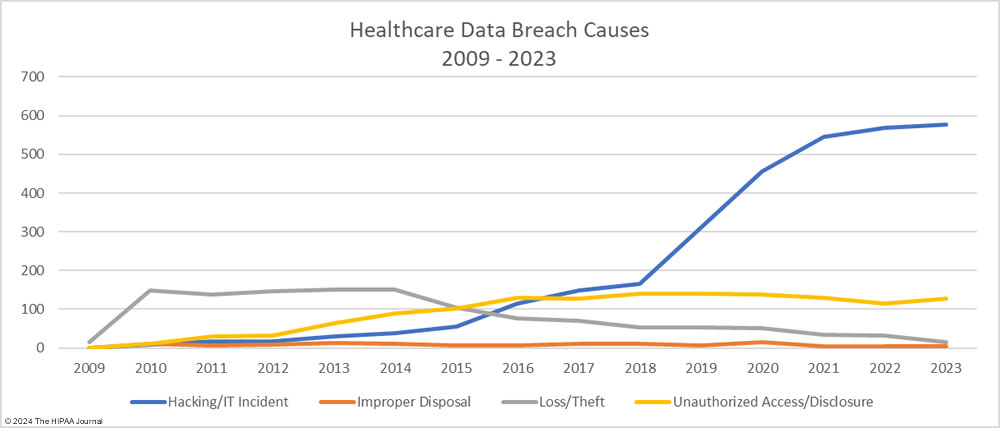
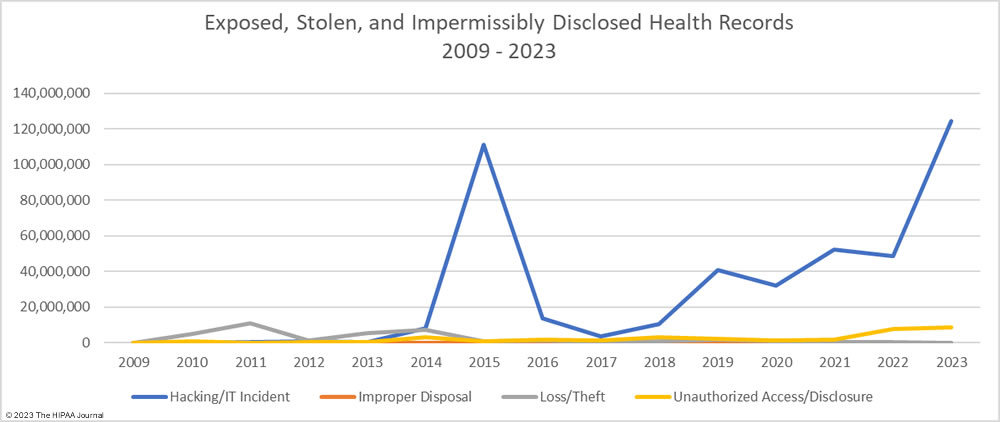
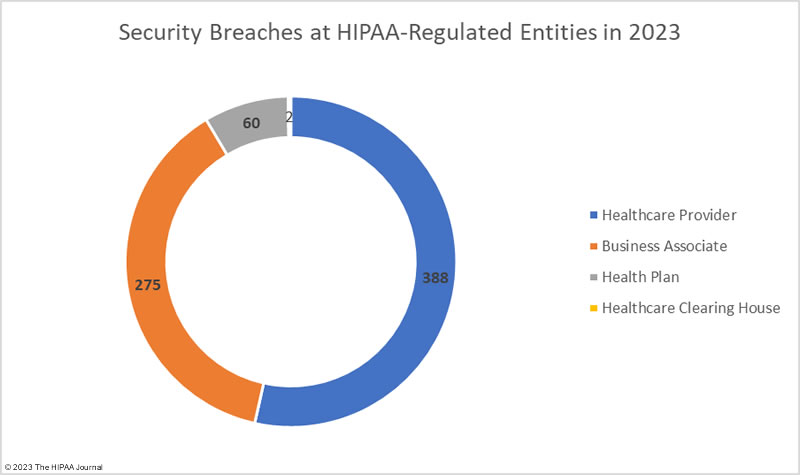
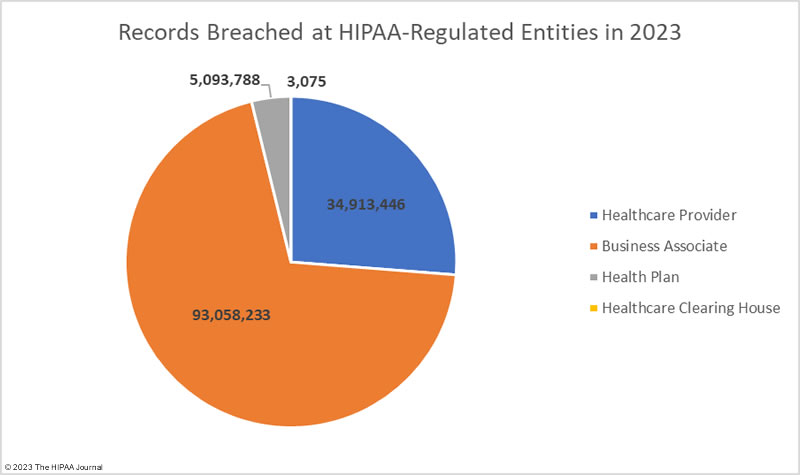
For the past few years, more than 700 large healthcare data breaches have been reported each year, a large proportion of which occurred at business associates of HIPAA-covered entities. To address the cybersecurity weaknesses routinely being exploited by threat actors, OCR proposed two sets of voluntary healthcare-specific cybersecurity performance goals (CPGs): essential and enhanced. The CPGs consist of high-impact measures to strengthen cybersecurity, and healthcare organizations were encouraged to adopt the essential CPGs and then mature their cybersecurity programs by adopting the enhanced cybersecurity goals.
When OCR released the CPGs, it was made clear that they were a precursor to mandatory new cybersecurity measures. The NPRM- HIPAA Security Rule To Strengthen the Cybersecurity of Electronic Protected Health Information was published by OCR in the Federal Register on January 6, 2025. Since then, OCR has been reviewing the extensive feedback it received.
The Security Rule update was proposed in response to increased cyberattacks, evolving healthcare delivery environments, and the common deficiencies identified by OCR during its compliance investigations. If a final rule is issued, it will be the first major update to the HIPAA Security Rule in more than two decades. In its proposed form, business associates will be required to make substantial changes to their cybersecurity and compliance programs. Proposed rules typically have a compliance deadline of approximately 240 days (8 months). If released per OCR’s proposed timetable, compliance will likely be required as early as Q1, 2027.
There are extensive new Security Rule requirements for business associates, which will be time-consuming and potentially costly to implement. These are not changes that can be implemented overnight or in a few weeks. The changes will require extensive planning, implementation, validation, and detailed documentation. Business associates should be proactive and assess where their current security program falls short, rather than wait until the final rule is issued.
Regulated Entities Must Implement All Security Rule Implementation Specifications
Changes have been made to the language of the HIPAA Security Rule, introducing the term HIPAA-regulated entities for covered entities and business associates to improve consistency. OCR has eliminated the distinction between “addressable” and “required” implementation specifications. The removal of “addressable” implementation specifications means covered entities and business associates will be required to comply with all implementation specifications. Together with the more prescriptive cybersecurity requirements, substantial changes will need to be made to security and compliance programs.
The current HIPAA Security Rule is scalable, flexible, and technology-neutral, whereas the proposed rule is more prescriptive and testable, with operationalized cybersecurity requirements. The proposed Security Rule introduces a host of new cybersecurity requirements, and while there are limited exceptions, some requirements are risk-based and only apply to systems containing ePHI, regulated entities will have to make significant changes to their cybersecurity programs. New requirements include encryption of all ePHI at rest and in transit, multifactor authentication across all systems, continuous monitoring of systems for anomalous activity, vulnerability scanning, penetration testing, more prescriptive patch management requirements, configuration management, anti-malware protections, network segmentation, and annual testing of technical controls.
The HIPAA Security Rule requires business associates to provide security awareness training under 45 CFR § 164.308(a)(5), Standard: Security Awareness and Training. This requirement applies to all workforce members with access to IT systems, not only staff who use or disclose PHI. Security awareness training is focussed on cybersecurity training and is separate from, and in addition to, HIPAA training for Business Associates on Privacy Rule, Breach Notification Rule, and organizational policy requirements. The proposed HIPAA Security Rule changes are not expected to change the existing security awareness training requirements.
More Detailed and Prescriptive Business Associate Risk Analysis Requirements
Certain requirements, such as the risk analysis, have more detailed and prescriptive requirements. Under the current regulations, business associates are required to periodically conduct a risk analysis to identify risks and vulnerabilities to ePHI, following any significant change to technology, software, hardware, or business practices, and after a security incident.
The proposed rule requires a risk analysis to be conducted at least annually. The risk analysis must identify and assess all risks and vulnerabilities to all systems, devices, applications, environments, and services that collect, receive, maintain, store, transmit, or touch ePHI. The risk analysis must cover risks associated with subcontractors, service providers, cloud environments, and integrated technologies, and must feed into contingency planning, disaster recovery, and downtime operations planning.
The risk analysis must cover all ePHI in the business associate’s possession, not just the ePHI created or received on behalf of a covered entity, including ePHI from multiple clients and ePHI maintained in shared systems. Before a HIPAA-compliant risk analysis can be conducted, the business associate must identify all systems, devices, applications, services, and environments where ePHI is created, received, maintained, or transmitted. That information must be maintained in a comprehensive, accurate, and up-to-date asset inventory.
The risk analysis must be a formal, fully documented, and repeatable process, aligned with recognised cybersecurity practices. It must be regularly updated to reflect changes in the healthcare environment, evolving threats, and new technologies, and be repeated when systems, subcontractors, business practices, technology, and threat conditions change. This update moves the risk analysis from what is often viewed, albeit incorrectly, as a one-time event to a continuous process. Everything must be documented in detail, including the methodology, identified risks, rationale for risk ratings, mitigation decisions, and residual risks, with written verification of the completeness of the risk analysis and implemented safeguards by qualified personnel.
Greater Oversight of Vendors by HIPAA-Covered Entities
Risks must be subjected to a risk management process, and while that has not changed, specific, documented mitigation plans need to be developed and prioritized for all risks, with remediation measures tracked through to completion. There will be greater oversight of business associates by covered entities. Previously, covered entities were required to obtain satisfactory assurances of HIPAA Security Rule compliance, such as by obtaining a signed business associate agreement. The updated Security Rule requires safeguards to be verified by a covered entity through annual written verification from the business associate.
That means business associates must maintain detailed documentation of all compliance efforts, including their risk analysis methodology and results, the mitigations implemented, and the administrative, physical, and technical safeguards implemented to reduce risks to a reasonable and appropriate level, plus any residual risks that have yet to be addressed. Safeguards must be reassessed and reverified every year.
In the event of a security incident involving ePHI, the HIPAA Breach Notification Rule requires business associates to notify each affected covered entity within 60 days; however, the updated HIPAA Security Rule requires covered entities to be notified within 24 hours of an emergency or other occurrence affecting their electronic information systems and the activation of contingency plans. Business associates must also have a plan for restoring access to critical systems. That means business associates are likely to face increased scrutiny of their breach response and will need to provide regular updates to their covered entity clients.
The expansion of requirements for business associates will require updates to current business associate agreements to include the new obligations. HIPAA-covered entities will need to incorporate the new HIPAA Security Rule requirements into their business associate templates, assess whether their current business associates meet the new requirements, and, if not, ensure that they have a viable plan to implement the required changes on time.
Comparison of Requirements of Current vs. Proposed Security Rule
| Compliance Area | Post HITECH Act – HIPAA Security Rule Requirement | Proposed HIPAA Security Rule Requirement |
| Applicability | Business associates were directly subject to the Security Rule, with certain obligations operationalized through business associate agreements. | Introduction of the term “HIPAA Regulated Entities.” Obligations of business associates are identical to those of covered entities, eliminating any interpretative discrepancies. |
| Implementation Specifications | Distinction between required and addressable implementation specifications | Elimination of distinction – All implementation specifications are required for compliance. |
| Asset Inventory | No requirement for an asset inventory. | Business associates must create and maintain a comprehensive and accurate technology asset inventory, on which the risk analysis will be based, complete with network/ePHI movement maps. |
| Risk Analysis | Business Associates required to conduct an accurate and thorough assessment of risks and vulnerabilities to ePHI. Risk assessments required periodically, and in response to material changes to systems, technology, and workflows | Explicit requirements for risk analysis methodology, which must be formal, repeatable, and documented. Must cover the entire ePHI ecosystem, with specific expectations for content. Must cover risks associated with subcontractors, vendors, cloud platforms, shared systems, service providers, and supply chains. Risk analyses must be conducted at least annually, and methodologies must be updated in response to changes to systems, vendors, threat conditions, and changing operational practices. Extensive documentation requirements, including methodology, analysis, mitigations, and residual risks. The risk analysis and safeguards must be documented and performed by qualified personnel, with written verifications required. |
| Administrative Safeguards: Standard: Evaluation | Periodic technical and nontechnical evaluation in response to environmental or operational changes affecting the security of ePHI | Consistent methodology required, with an emphasis on recurring testing, technical reviews, vulnerability scanning, and documented reassessments, including in response to emerging threats and operational/environmental changes. Extensive documentation requirements for analyses and mitigations. |
| Technical Safeguards | Technologies and configurations not specified. Left to the discretion of the business associate, with some addressable requirements. | Specific cybersecurity measures mandated: Encryption of all ePHI at rest and in transit (with limited exceptions) aligned with current best practices; implementation of multi-factor authentication across all systems; continuous monitoring of systems for anomalous activity; vulnerability scanning and penetration testing; prescriptive patch management requirements and timelines; configuration management; backup restoration timing requirements; anti-malware protections, network segmentation; access control specifications; mandatory creation of audit and access logs; and periodic testing of technical controls. |
| Compliance Audits and Testing | Perform a periodic technical and nontechnical evaluation to establish the extent to which policies and procedures meet Security Rule requirements. | Annual risk analyses, verification of safeguards, testing of contingency plans, and vulnerability scanning and penetration testing. |
| Physical Safeguards | Physical measures, policies, and procedures to protect a regulated entity’s electronic information systems and related buildings and equipment. | Minor requirements for physical safeguards, including workstation management and facility access. |
| Workforce Access Management | Ensure that all members of its workforce have appropriate access to ePHI. Flexible and technology neutral, without prescriptive standards or review frequencies. | Expanded requirements for access provisioning, termination procedures, privilege management, minimum necessary access, and periodic reviews of access provisions. |
| Administrative Safeguards: Business associate contracts | Covered entities must obtain satisfactory assurances that the business associate will appropriately safeguard ePHI, typically achieved through business associate agreements. | Covered entities must verify that a business associate has implemented the required technical safeguards. The business associate must provide the necessary documentation to prove compliance. |
| Contingency Planning | Must establish data backup, disaster recovery, and emergency operational plans. No requirement to report activation of contingency plans. | Formalized incident response plans required, with defined roles and responsibilities, incident classification, response timelines, post-incident analysis, and detailed documentation requirements. Required criticality analysis, maintenance of exact backup copies, restoration testing, and restoration of critical systems and data within the specified timeframes. Business associates must report emergencies involving electronic information systems and activation of contingency plans to covered entities within 24 hours. |
| Documentation | Policies, procedures, and analysis documentation must be retained for 6 years, with no specified requirements for format. | Business associate must maintain structured, granular documentation of risk analyses, verify safeguards, risk mitigations, contingency plan reporting, cybersecurity training, third-party risk assessments, logs of system activity, and continuous monitoring. OCR will require documentation to be produced in data breach/complaint investigations and compliance reviews. |
| Security Incident Procedures | Must identify, respond to, and mitigate harm from security incidents. | Formal incident response plan required with testing requirements, and workforce reporting procedures. Adds expectation for timely notifications to appropriate regulated entities when shared systems or data are impacted. |
| Vendor and supply chain risk management | As stipulated in business associate agreements | Formal requirement for downstream vendor oversight and the assessment and management of risks associated with vendors and subcontractors. Analyses and mitigations must be fully documented for audit purposes |
| Business associate agreements | – | Business associate agreements must be updated to reference the new requirements. Covered entities require annual written verifications of technical safeguards, validated by qualified cybersecurity personnel. |
| CyberSecurity Training | CFR § 164.308(a)(5), Standard: Security Awareness and Training. | Business associated agreements can be expected to include cybersecurity training for business associates. |
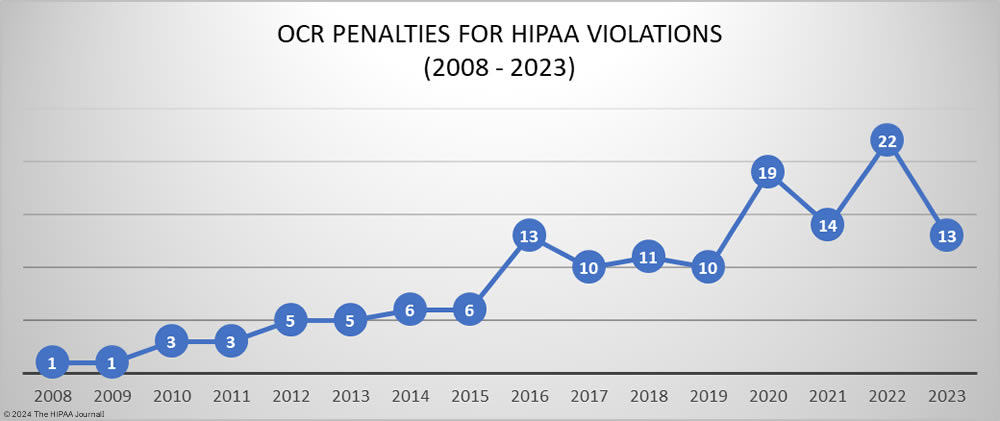
| Enforcement | There has been increased enforcement in 2026. | Business associates may face increased liability for compliance failures. The proposed rule has more prescriptive standards that should aid enforcement by reducing interpretive flexibility. |
When and If a Final Rule Will Be Issued
The proposed HIPAA Security Rule update significantly raises the cybersecurity bar for all HIPAA-regulated entities. Any business associate that can demonstrate that they have implemented a rigorous and well-documented risk analysis, all new safeguards, and have mitigated third-party risks will be in an ideal position to comply with the final rule when it is issued, and will be perfectly positioned to attract new healthcare clients.
When the HHS published its regulatory agenda for the year, the May release date was not set in stone. The proposed rule was delayed by several months, and the same may happen to the final rule, especially if the decision is made to severely cut back on its requirements. How long a delay is impossible to predict, as OCR is keeping its cards close to its chest. There is a possibility that the final rule may not be issued, as the Trump administration is pro-deregulation; however, the current state of healthcare cybersecurity and the volume of cyberattacks and data breaches being reported each month mean something needs to be done.
In my opinion, a final rule will be issued, and many of the core requirements will be retained, especially the new risk analysis requirements. It is therefore in the best interests of all business associates to start preparing for that release by reviewing their current security measures and planning, organizationally and financially, for Security Rule changes. While the final rule could differ substantially from the proposed rule, the core elements of the proposed rule are unlikely to change. The best place for business associates to start is with a gap analysis to determine how current security measures stack up against the proposed new HIPAA Security Rule standards, to ensure they can hit the ground running when the final rule is released and be fully compliant ahead of the enforcement date.
Steve Alder, Editor-in-Chief, HIPAA Journal
The post The Impact of Proposed Changes to the HIPAA Security Rule for Business Associates appeared first on The HIPAA Journal.