Senator Mark Warner (D-Va) has written letters to leaders of the Department of Health and Human Services (HHS), the Food and Drug Administration (FDA), the Centers for Medicare and Medicaid Services (CMS), the National Institute of Standards and Technology (NIST), and 12 healthcare associations requesting answers to a list of healthcare cybersecurity questions.
Warner, a member of the Senate Finance Committee and co-chair of the Senate Cybersecurity Caucus, is deeply concerned about the state of cybersecurity in healthcare and is calling for a collaborative effort “to develop a short- and long-term strategy reducing cybersecurity vulnerabilities in the health care sector” and “develop a national strategy that improves the safety, resilience, and security of our healthcare industry.”
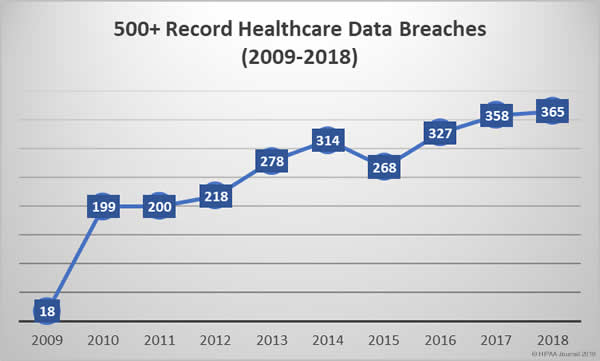
The healthcare industry is being targeted by cybercriminals and those attacks are succeeding far too frequently. 2014 was the sixth successive year to see an annual increase in healthcare data breaches. In 2015, another record was broken. The most healthcare records ever breached. 113 million healthcare records were exposed that year.
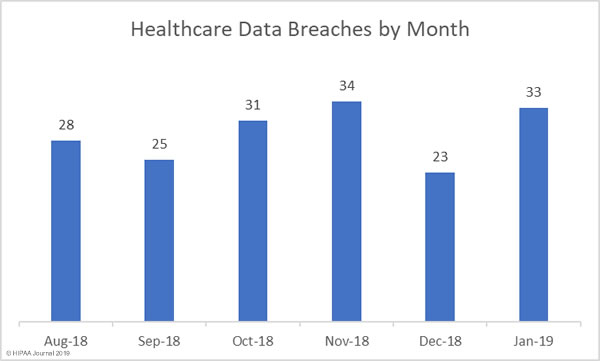
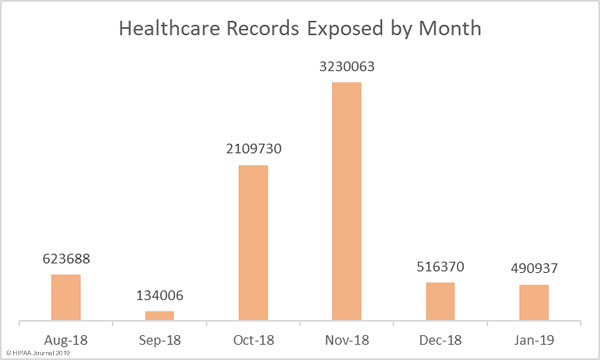
Even though investment in cybersecurity is increasing, records continue to be broken each year and data breaches have now reached unprecedented levels. 2016 saw the record for the most healthcare data breaches in a single year broken again, and again in 2017, and yet again in 2018. Last year, healthcare data breaches were reported at a rate of one a day. That trend is likely to continue unless action is taken.
In the letters, Warner cited a 2015 GAO report that estimated cyberattacks on the healthcare industry would result in $305 million in losses over a five-year period and a Trend Micro report in the same year which suggests 100,000 healthcare devices and systems have been exposed over the internet.
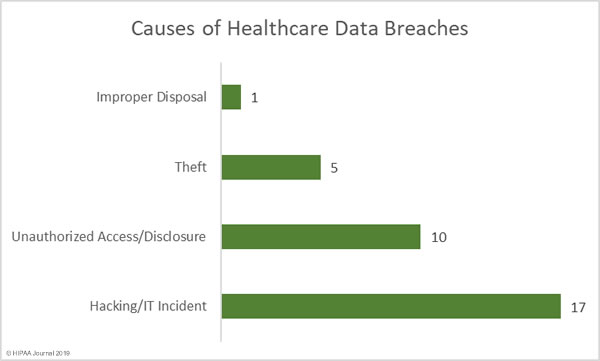
Healthcare data is of high value to cybercriminals and hospitals store vast quantities of patient data. Successful attacks can be extremely profitable, either through theft and resale of healthcare data or by preventing healthcare providers from accessing patient data through ransomware attacks. Cyberattacks cannot be prevented, but it is possible to improve resilience and stop most of those attacks from succeeding.
As a first step, Warner has asked each agency to supply details of the actions each has taken to identify and reduce vulnerabilities in the healthcare industry, and what each agency has done to develop a national strategy to reduce vulnerabilities. Warner wants to know whether each department and agency has been seeking input from private sector healthcare stakeholders to address vulnerabilities and any potential changes to current laws and regulations that would help to combat cyberattacks on healthcare entities.
Similar questions have been sent to healthcare associations and organizations including the Healthcare Information Management and Systems Society (HIMSS), the American Hospital Association (AHA), the American Medical Association (AMA), and the Health Information Sharing and Analysis Center (H-ISAC). They have been asked to explain the steps that they have taken to improve security awareness and their technical capabilities.
The sheer volume of successful cyberattacks has prompted state regulators to introduce new requirements for entities doing business in their respective states to improve security and privacy protections, but what is also required is a nationwide effort to improve privacy and security. Federal regulators and Congress are taking steps to develop a national cybersecurity strategy. Warner hopes that his efforts will help to speed up that process.
The post Senator Demands Answers from Government Agencies and Healthcare Associations on Healthcare Cybersecurity appeared first on HIPAA Journal.