The 2018 Insider Threat Intelligence Report from Dtex Systems shows how a lack of visibility into employee activities is preventing security teams from acting on serious data security threats.
The report is based on data gathered from risk assessments performed on the firm’s customers and prospective customers. Those risk assessments highlighted just how common it is for employees to attempt to bypass security controls, download shadow IT, and violate company policies.
If your risk assessment has identified employees attempting to bypass security controls, you are not alone. According to the Dtex Systems report, 60% of risk assessments uncovered attempts by employees to bypass an organization’s security controls, use of private and anonymous browsers, or cases where employees had researched how to bypass security controls.
In most cases, employees are attempting to bypass security controls to gain access to websites that breach acceptable internet usage policies – such as adult content, gaming, and gambling sites, and to access P2P file sharing websites. 67% of companies discovered inappropriate Internet use. It is also common for employees to try to download shadow IT to make their jobs easier – use of tools such as Dontsleep, Caffeine, WireShark, or SnippingTool is common, even though those programs are prohibited.
While there may not be any malicious intent, these actions jeopardize security and could easily result in the accidental disclosure of sensitive information or malware infections. Programs such as open VPN tools and CCleaner are also commonly downloaded – both of which are an indicator of employees attempting to cover their tracks, potentially to hide malicious activities.
72% of risk assessments determined at least some employees were using high-risk applications or hacking tools and 90% of risk assessments showed employees were transferring data to unencrypted USB devices. 78% of companies also discovered company data that were publicly accessible online due to mistakes made by employees.
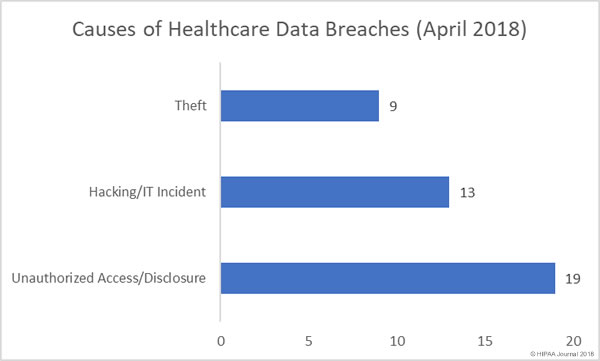
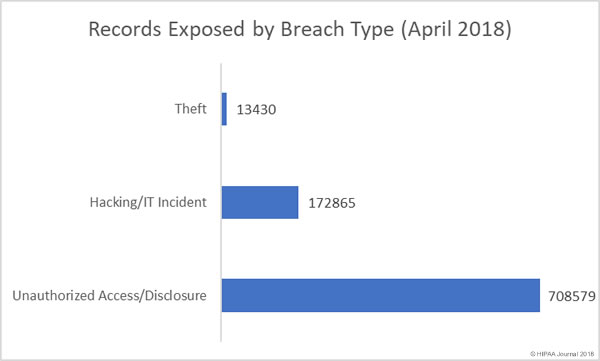
The 2018 Verizon Data Breach Investigations Report showed almost a third of the 2,216 confirmed breaches were caused by insiders and insider data breaches are far more common in the healthcare industry. Typically, in any given month, more healthcare industry data breaches are caused by insiders than breaches caused by external threat actors.
While technological controls can be implemented to improve security, it is important not to neglect the human element. Security awareness training shows employees how certain behaviors can easily result in a data breach; however, employees are often aware that certain actions increase risk, yet they still engage in risky activities. Many employees do not think that their actions will result in a data breach and carry on taking risks. They rely on IT teams to address cybersecurity and take no personal responsibility for helping to keep their company’s systems and data secure.
Security teams can take steps to reduce risk, but unless they have visibility into what their employees are doing they will not know the extent of risk taking by employees are could remain blind to these potentially dangerous activities.
Unfortunately, no single solution can be used to protect against insider threats. Only by using a range of solutions will healthcare organizations be able to tackle the problem of insider data breaches.
In addition to performing regular risk analyses to identify potential threats, Dtex Systems suggests the use of Security Information and Event Management (SIEM), user behavior analytics, and data loss prevention technologies. Additionally, employee monitoring solutions and user behavior intelligence are required to highlight abnormal activities and suspicious behavior. Such solutions will help security teams identify insider threats and take action before they lead to a data breach.
The post Lack of Visibility into Employee Activity Leaves Organizations Vulnerable to Data Breaches appeared first on HIPAA Journal.