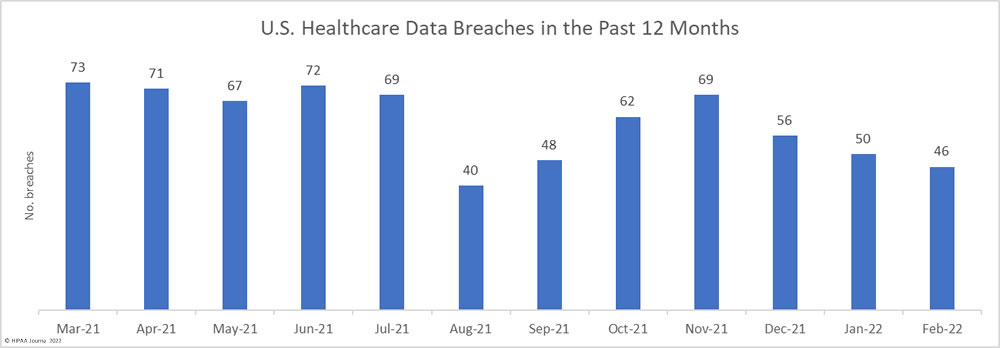
For the third successive month, the number of data breaches reported to the HHS’ Office for Civil Rights (OCR) has fallen. 46 healthcare data breaches of 500 or more records were reported to OCR in February – an 8% fall from January. February saw the lowest number of data breaches in the past 5 months. Even with the reduction in breaches, on average, more than 2 healthcare data breaches have been reported each day over the past 12 months. From March 1, 2021, to February 28, 2022, there have been 723 reported data breaches of 500 or more records.
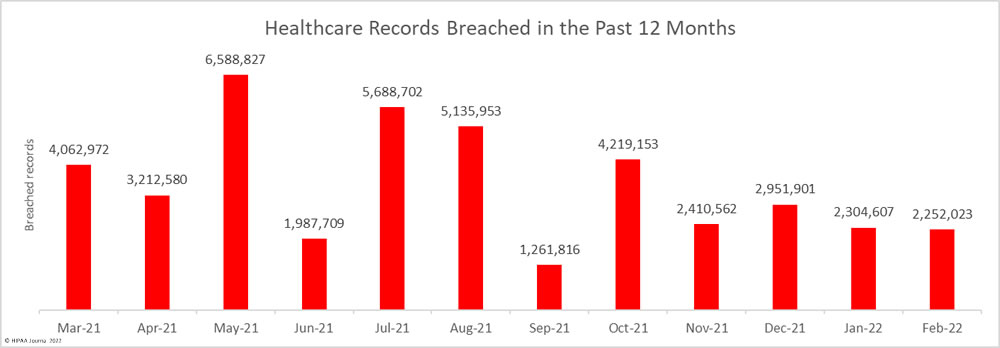
Across February’s 46 incidents, the records of 2,525,023 individuals were exposed or compromised – a 2.28% fall from the previous month – which is considerably lower than the 3,506,400 records that have been breached each month, on average, from March 1, 2021, to February 28, 2022. At least 42,076,805 healthcare records were exposed over that period. In February, the average breach size was 48,957 records and the median breach size was 7,014 records.
Largest Healthcare Data Breaches Reported in February 2022
22 HIPAA-regulated entities reported breaches of 10,000 or more healthcare records in February. The largest breach of the month was reported by Morley Companies, which was a hacking incident that resulted in the exposure and possible theft of the protected health information of 521,046 members of its health plan.
Monongalia Health System reported a major hacking incident that potentially resulted in the theft of the PHI of 492,861 individuals. The breach was discovered a few days after the health system announced a previous data breach – a phishing and business email compromise attack – that affected almost 398,164 individuals.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Type of Breach | Cause of Breach |
| Morley Companies, Inc. | MI | Business Associate | 521,046 | Hacking/IT Incident | Unspecified hacking incident |
| Monongalia Health System, Inc. | WV | Healthcare Provider | 492,861 | Hacking/IT Incident | Unspecified hacking incident |
| Norwood Clinic | AL | Healthcare Provider | 228,000 | Hacking/IT Incident | Unspecified hacking incident |
| Logan Health Medical Center | MT | Healthcare Provider | 213,543 | Hacking/IT Incident | Unspecified hacking incident |
| South Shore Hospital Corporation | IL | Healthcare Provider | 115,670 | Hacking/IT Incident | Unspecified hacking incident |
| Comprehensive Health Services | FL | Healthcare Provider | 106,752 | Hacking/IT Incident | Business email compromise |
| US Radiology Specialists, Inc. | NC | Business Associate | 87,552 | Hacking/IT Incident | Unknown |
| Memorial Village ER | TX | Healthcare Provider | 80,000 | Hacking/IT Incident | Unspecified hacking incident |
| Montrose Regional Health | CO | Healthcare Provider | 52,632 | Hacking/IT Incident | Compromised email accounts |
| Cross Timbers Health Clinics dba AccelHealth | TX | Healthcare Provider | 48,126 | Hacking/IT Incident | Ransomware attack |
| Jacksonville Spine Center, P.A. | FL | Healthcare Provider | 38,000 | Hacking/IT Incident | Ransomware attack |
| The Puerto Rican Organization to Motivate, Enlighten, and Serve Addicts, Inc. | NY | Healthcare Provider | 30,220 | Hacking/IT Incident | Compromised email accounts |
| EPIC Pharmacy Network, Inc. | VA | Healthcare Provider | 28,776 | Hacking/IT Incident | Compromised email accounts |
| Ascension Michigan (single affiliated covered entity) ACE | MI | Healthcare Provider | 27,177 | Unauthorized Access/Disclosure | Unauthorized EHR access by an employee |
| Bako Diagnostics | GA | Healthcare Provider | 25,745 | Hacking/IT Incident | Unspecified hacking incident (data exfiltration confirmed) |
| Ultimate Care, Inc. | NY | Healthcare Provider | 15,788 | Hacking/IT Incident | Compromised email accounts |
| Alliance Physical Therapy Group, LLC | MI | Business Associate | 14,970 | Hacking/IT Incident | Unspecified hacking incident |
| University Medical Center Southern Nevada | NV | Healthcare Provider | 12,230 | Hacking/IT Incident | Unknown |
| Seneca Nation Health System | NY | Healthcare Provider | 12,000 | Hacking/IT Incident | Unknown |
| CareOregon Advantage | OR | Health Plan | 10,467 | Unauthorized Access/Disclosure | Misdirected email |
| Extend Fertility | NY | Healthcare Provider | 10,373 | Hacking/IT Incident | Ransomware attack |
| Houston Health Department | TX | Healthcare Provider | 10,291 | Unauthorized Access/Disclosure | Misconfigured web portal |
Causes of February 2022 Healthcare Data Breaches
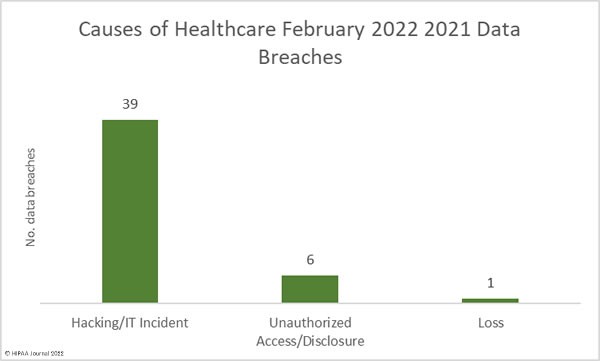
As the table above shows, hacking incidents dominated the breach reports in February. 39 of the month’s data breaches were hacking/IT incidents, the majority of which saw unauthorized individuals hack into networks and view and/or exfiltrate sensitive data. It is common for breached entities to disclose hacking incidents but not publicly disclose details about the exact nature of the attacks, such as if they involved malware or ransomware. Across those 39 breaches, the records of 2,184,973 individuals were exposed or compromised. The average breach size was 56,025 records and the median breach size was 6,221 records.
There were 6 unauthorized access/disclosure incidents reported in February involving the records of 62,550 individuals. The average breach size was 10,425 records and the median breach size was 8,953 records. There was one loss incident involving a desktop computer that contained the PHI of 4,500 individuals. There were no reported theft or improper disposal incidents.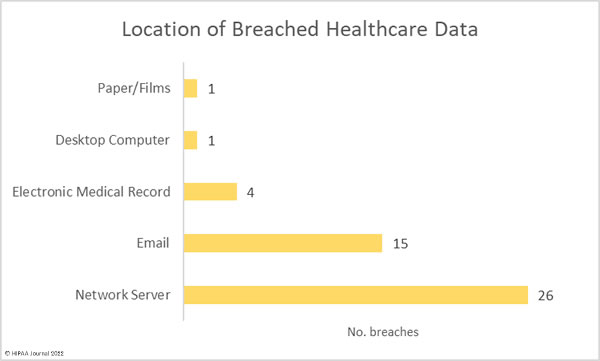
Healthcare Data Breaches by State
HIPAA-regulated entities in 23 states reported data breaches in February. New York the worst affected state with 6 reported breaches, followed by Florida, Michigan, and New Jersey which each had 5.
| State | Number of reported breaches |
| New York | 6 |
| Florida, Michigan, and New Jersey | 5 |
| Texas and Virginia | 3 |
| Pennsylvania and West Virginia | 2 |
| Alabama, Arizona, Colorado, Connecticut, Georgia, Illinois, Massachusetts, Montana, Nevada, North Carolina, Oklahoma, Oregon, Rhode Island, Utah, and Washington | 1 |
Healthcare Data Breaches by HIPAA-Regulated Entity Type
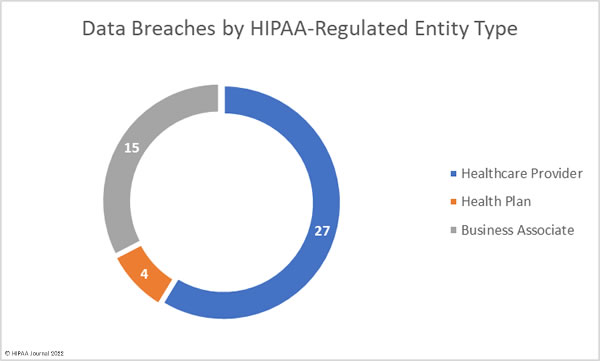
Healthcare providers were the worst affected entity in February 2022 having reported a total of 35 data breaches involving the records of 1,597,155 individuals. There were 6 data breaches reported by health plans involving 21,284 records, and 5 data breaches were self-reported by business associates of HIPAA-covered entities, which involved the records of 633,584 individuals.
10 breaches occurred at business associates but were reported by the affected covered entity, with the adjusted figures shown in the chart below.
HIPAA Enforcement Actions in February 2022
There were no announcements by the HHS’ Office for Civil Rights or state Attorneys General about HIPAA enforcement actions in February. In fact, there have been no financial penalties imposed for HIPAA violations so far in 2022.
OCR Director, Lisa J. Pino, has confirmed that the Department of Health and Human Services has an ambitious regulatory agenda for 2021, which will include strong enforcement of HIPAA compliance, including the continuation of its enforcement initiative targeting healthcare providers that violate the HIPAA Right of Access and fail to provide individuals with timely access to their medical records.
The post February 2022 Healthcare Data Breach Report appeared first on HIPAA Journal.