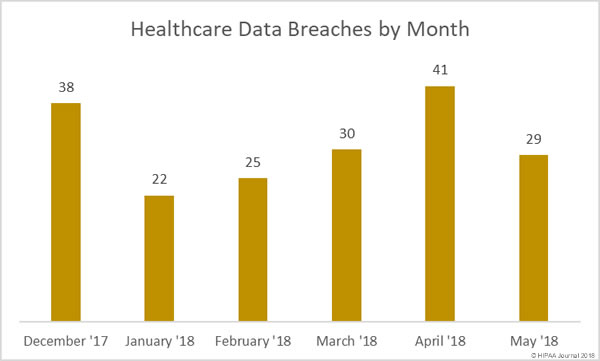
April was a particularly bad month for healthcare data breaches with 41 reported incidents. While it is certainly good news that there has been a month-over-month reduction in healthcare data breaches, the severity of some of the breaches reported last month puts May on a par with April.
There were 29 healthcare data breaches reported by healthcare providers, health plans, and business associates of covered entities in May – a 29.27% month-over month reduction in reported breaches. However, 838,587 healthcare records were exposed or stolen in those incidents – only 56,287 records fewer than the 41 incidents in April.
In May, the mean breach size was 28,917 records and the median was 2,793 records. In April the mean breach size was 21,826 records and the median was 2,553 records.
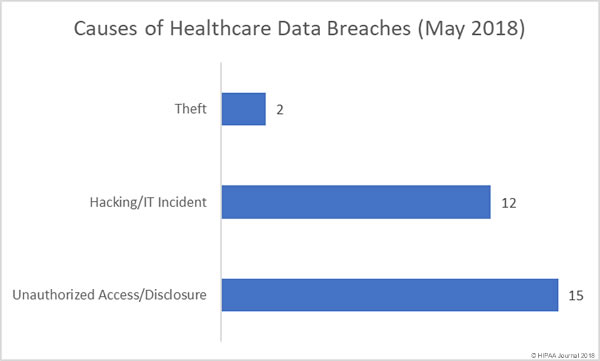
Causes of May 2018 Healthcare Data Breaches
Unauthorized access/disclosure incidents were the most numerous type of breach in May 2018 with 15 reported incidents (51.72%). There were 12 hacking/IT incidents reported (41.38%) and two theft incidents (6.9%). There were no lost unencrypted electronic devices reported in May and no improper disposal incidents.
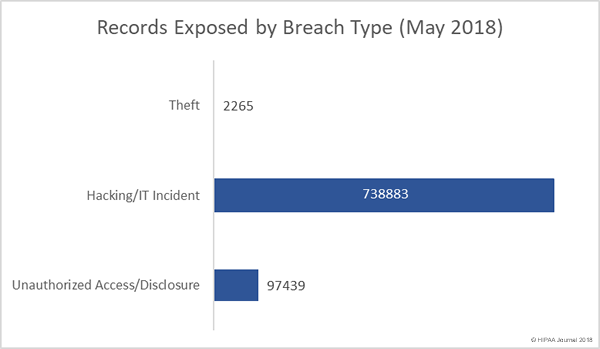
The 12 hacking/IT incidents reported in May resulted in the exposure/theft of 738,883 healthcare records – 88.11% of the total for May. Unauthorized access/disclosure incidents affected 97,439 patients and health plan members – 11.62% of the total. Theft incidents resulted in unauthorized individuals obtaining the PHI of 2,265 individuals – 0.27% of the monthly total.
Largest Healthcare Data Breaches Reported in May 2018
The largest healthcare data breach reported in May 2018 – by some distance – was the 538,127-record breach at the Baltimore, MD-based healthcare provider LifeBridge Health Inc. The breach was reported in May, although it occurred more than a year and a half earlier in September 2016, when malware was installed on its server that hosts electronic health records.
In addition to names and contact information, clinical and treatment information, insurance information, and, in some instances, Social Security numbers, were compromised. The scale of the breach and the types of information exposed makes it one of the most serious healthcare data breaches discovered in 2018.
As the table below shows, hacks and IT incidents were behind the most serious breaches in May.
| Breached Entity | Entity Type | Records Breached | Breach Type |
| LifeBridge Health, Inc | Healthcare Provider | 538127 | Hacking/IT Incident |
| The Oregon Clinic, P.C. | Healthcare Provider | 64487 | Hacking/IT Incident |
| Dignity Health | Healthcare Provider | 55947 | Unauthorized Access/Disclosure |
| Aultman Hospital | Healthcare Provider | 42625 | Hacking/IT Incident |
| Holland Eye Surgery and Laser Center | Healthcare Provider | 42200 | Hacking/IT Incident |
| USACS Management Group, Ltd. | Business Associate | 15552 | Hacking/IT Incident |
| Florida Hospital | Healthcare Provider | 12724 | Hacking/IT Incident |
| Aflac | Health Plan | 10396 | Hacking/IT Incident |
| Cerebral Palsy Research Foundation of Kansas, Inc. | Healthcare Provider | 8300 | Unauthorized Access/Disclosure |
| Associates in Psychiatry and Psychology | Healthcare Provider | 6546 | Hacking/IT Incident |
Location of Breached Protected Health Information
In May, the most common location of breached protected health information was email. 11 of the 29 reported breaches involved hacks of email accounts and misdirected emails. It was a similar story in April, when email was also the main location of breached PHI.
In May there were 7 incidents affecting network servers – hacks, malware infections, and ransomware incidents – and 7 incidents involving paper records.
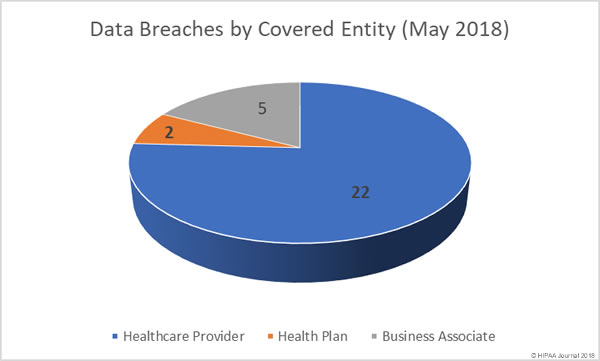
Data Breaches by Covered Entity Type
Healthcare providers experienced the lion’s share of the healthcare data breaches in May 2018, with 22 incidents reported. Only two health plans suffered a data breach in May.
Five business associates of HIPAA-covered entities reported a breach, although a further four breaches had some business associate involvement.
Healthcare Data Breaches by State
California and Ohio were the worst affected by healthcare data breaches in May 2018, with each state having four breaches. Oregon and Texas each experienced two data breaches in May. Nevada saw four breaches reported, but three of those were the same incident, only reported separately by each of the three Dignity Health hospitals affected.
One healthcare data breach was reported by a HIPAA-covered entity or business associate based in Arkansas, Arizona, Colorado, Florida, Georgia, Indiana, Kansas, Massachusetts, Maryland, Michigan, Minnesota, Nebraska, and New York.
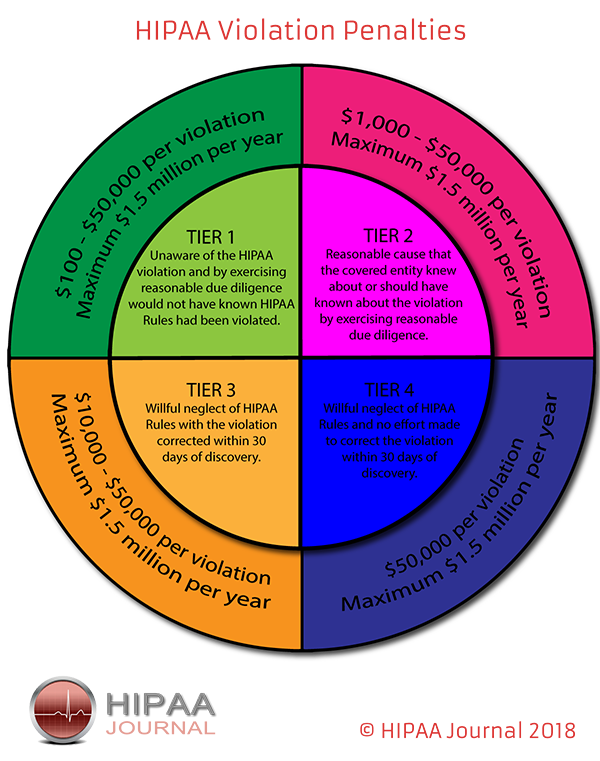
Financial Penalties for HIPAA Violations
While OCR and state attorneys general continue to enforce HIPAA Rules and take action against covered entities and business associates for noncompliance, there were no financial settlements announced by either in May 2018.
Data Source: The Department of Health and Human Services’ Office for Civil Rights.
The post May 2018 Healthcare Data Breach Report appeared first on HIPAA Journal.