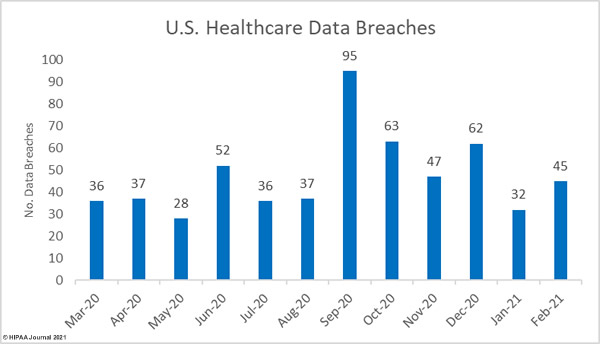
The was a 40.63% increase in reported data breaches of 500 or more healthcare records in February 2021. 45 data breaches were reported to the Department of Health and Human Services’ Office for Civil Rights by healthcare providers, health plans and their business associates in February, the majority of which were hacking incidents.
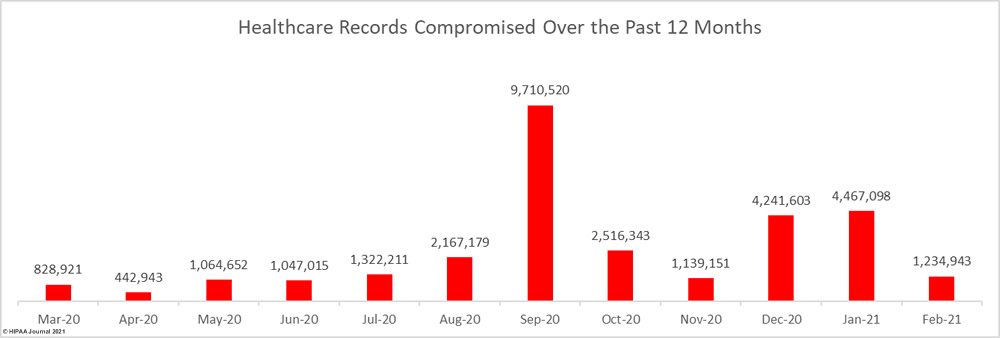
After two consecutive months where more than 4 million records were breached each month there was a 72.35% fall in the number of breached records. 1,234,943 records were exposed, impermissibly disclosed, or stolen across the 45 breaches.
Largest Healthcare Data Breaches Reported in February 2021
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Type of Breach | Cause of Breach |
| The Kroger Co. | OH | Healthcare Provider | 368,100 | Hacking/IT Incident | Ransomware |
| BW Homecare Holdings, LLC (Elara Caring single affiliated covered entity) | TX | Healthcare Provider | 100,487 | Hacking/IT Incident | Phishing |
| RF EYE PC dba Cochise Eye and Laser | AZ | Healthcare Provider | 100,000 | Hacking/IT Incident | Ransomware |
| Gore Medical Management, LLC | GA | Healthcare Provider | 79,100 | Hacking/IT Incident | Hacking incident |
| Summit Behavioral Healthcare | TN | Healthcare Provider | 70,822 | Unauthorized Access/Disclosure | Phishing |
| Humana Inc | KY | Health Plan | 62,950 | Unauthorized Access/Disclosure | Subcontractor shared PHI without consent |
| Nevada Orthopedic & Spine Center | NV | Healthcare Provider | 50,000 | Hacking/IT Incident | Unconfirmed |
| Fisher Titus Health, Inc. | OH | Health Plan | 49,636 | Hacking/IT Incident | Phishing |
| Covenant HealthCare | MI | Healthcare Provider | 47,178 | Hacking/IT Incident | Phishing |
| UPMC | PA | Healthcare Provider | 36,086 | Hacking/IT Incident | Phishing attack on BA |
| Grand River Medical Group | IA | Healthcare Provider | 34,000 | Hacking/IT Incident | Phishing |
| AllyAlign Health, Inc. | VA | Health Plan | 33,932 | Hacking/IT Incident | Ransomware |
| Harvard Eye Associates | CA | Business Associate | 29,982 | Hacking/IT Incident | Ransomware attack on BA |
| Texas Spine Consultants, LLP | TX | Healthcare Provider | 25,728 | Unauthorized Access/Disclosure | Unconfirmed |
| UPMC Health Plan | PA | Health Plan | 19,000 | Hacking/IT Incident | Phishing attack on BA |
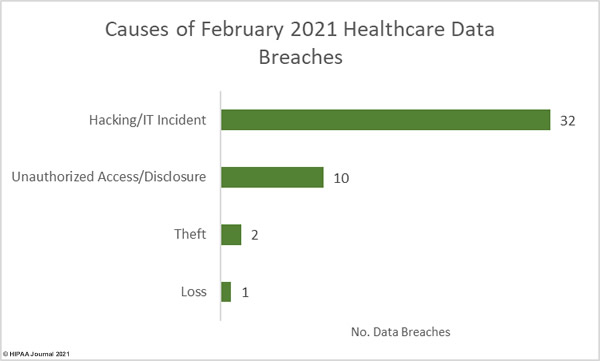
Causes of February 2021 Healthcare Data Breaches
Three breaches of more than 100,000 record were reported in February. The largest healthcare data breach of the month was reported by Kroger, an Ohio-based chain of supermarkets and pharmacies. The breach was due to a CLOP ransomware attack on a vendor – Accellion – that resulted in the theft of the protected health information of 368,100 of its customers. Kroger was one of several HIPAA-covered entities to be affected by the breach.
Elara Caring, one of the nation’s largest providers of home-based care, announced that several employee email accounts containing protected health information had been accessed by unauthorized individuals as a result of responses to phishing emails. Cochise Eye and Laser was also the victim of a ransomware attack in which the protected health information of 100,000 individuals was potentially stolen.
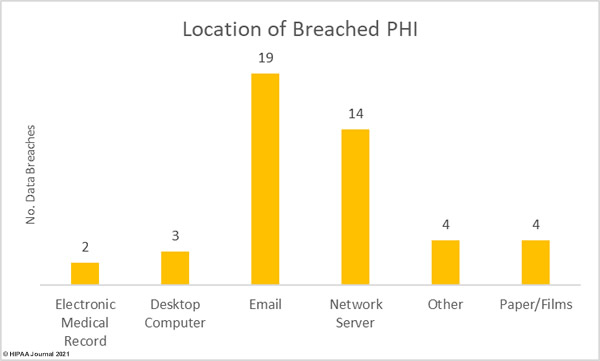
Phishing attacks were the most common cause of data breaches in February, with network server incidents in close second. These mostly involved hacking and the deployment of malware or ransomware. Hacking incidents accounted for 71.1% of the month’s breaches and 85.7% of all records breached in the month. The average size of a hacking breach was 30,239 records and the median breach size was 8,849 records.
There were 10 unauthorized access/disclosure incidents reported in February involving 172,799 records. The average breach size was 17,280 records and the median breach size was 2,497 records. There were 2 theft incidents and 1 reported loss incident reported involving a total of 3,773 records, all three of which involved paper records.
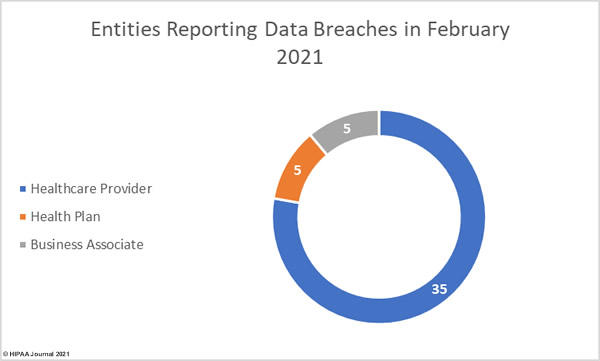
Entities Reporting Healthcare Data Breaches in February 2021
Healthcare providers were the worst affected covered entity type in February, with 35 breaches reported. There were 5 breaches reported by health plans and 5 reported by business associates of HIPAA-covered entities. A further 5 breaches were reported by the covered entity but had some business associate involvement.
Healthcare Data Breaches by State
Healthcare data breaches of 500 or more records were reported in 20 states in February 2021. The worst affected states were California and Texas with six breaches reported in each state. 5 entities in Pennsylvania reported breaches, there were 4 breaches reported in Florida and Michigan, 2 in each of North Carolina, Nevada, Ohio, Tennessee, and Virginia, and 1 in each of Arizona, Colorado, Georgia, Iowa, Kentucky, Louisiana, Minnesota, North Dakota, Utah, and Wyoming.
HIPAA Enforcement Activity in February 2021
In February, the HHS’ Office for Civil Rights announced two settlements had been reached with HIPAA-covered entities to resolve potential violations of the HIPAA Rules. Both enforcement actions were in response to complaints from patients who had not been provided with timely access to their medical records.
OCR launched a new enforcement initiative in late 2019 targeting healthcare providers who were not complying with the HIPAA Right of Access provision of the HIPAA Privacy Rule. Three Right of Access enforcement actions have resulted in settlements so far in 2021, and the latest two bringing the total number of settlements under this enforcement initiative to 16.
Sharpe Healthcare settled its case with OCR and paid a $70,000 penalty and Renown Health settled its case for $75,000.
The post February 2021 Healthcare Data Breach Report appeared first on HIPAA Journal.