A new report released by the Department of Health and Human Services’ Office of Inspector General (OIG) has revealed the vast majority of Medicaid data breaches are relatively minor and only affect an extremely limited number of individuals.
For the study, OIG assessed all breaches reported by Medicaid agencies and their contractors in 2016. According to the report, the records of 515,000 Medicaid beneficiaries were exposed in 2016, spread across 1,260 data breaches.
Almost two thirds of Medicaid data breaches reported in 2016 affected a single person with a further 29% of breaches affecting between 1 and 9 individuals. Large-scale breaches, which resulted in the data of 500 or more beneficiaries being exposed, accounted for 1% of the annual total.
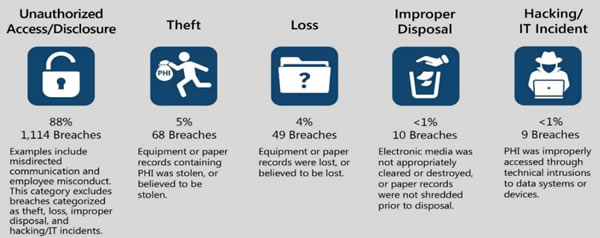
While the breach causes were highly varied, the majority of incidents were the result of simple errors such as misaddressing a letter, fax, or email. Those breaches only resulted in a very limited amount of PHI being exposed, such as a beneficiary name and Medicaid or other ID number. Out of the 1,260 breaches only 303 resulted in the exposure of a Social Security number and just 23 involved financial information. Hackers may be responsible for a large percentage of healthcare data breaches, but there were only 9 hacking incidents reported in 2016 that resulted in the exposure of Medicaid data.
Image source: HHS Office of Inspector General
OIG explained that previous reviews have concentrated on identifying vulnerabilities in states’ information systems and controls, which could potentially be exploited to gain access to Medicaid systems and data. This review was concerned with the breach response when security incidents occur. An efficient breach response can limit the potential for harm such as identify theft.
In addition to an analysis of Medicaid data breaches, OIG also assessed the breach response policies and procedures in 50 states and the District of Columbia. OIG discovered a common breach reporting framework has been adopted by the majority of U.S. states, which covers investigations of breaches and their scope, the best way to respond to data breaches, how to protect breach victims, and identifying the actions to take to correct vulnerabilities to prevent future security incidents. OIG also assessed the responses to individual breaches in nine states to gain a better understanding of the breach response processes.
OIG noted that the breach response processes varied slightly from state to state, with all meeting the requirements of HIPAA as well as state-specific laws. While all breaches were reported to the HHS’ Office for Civil Rights to meet the requirements of the HIPAA Breach Notification Rule, many states failed to routinely notify the Centers for Medicare & Medicaid Services (CMS) separately, even though the CMS has required states to do so since 2006.
OIG suggests that this was likely due to the introduction of the HIPAA Breach Notification Rule in 2009.
The failure to report Medicaid breaches directly to the CMS hampers the agency’s ability to monitor data security issues nationally. This can make it harder to identify multi-state data breaches and determine when best practices and guidance need to be issued to correct common data security issues.
To correct the problem, OIG has recommended CMS should issue updated guidance for Medicaid agencies and their contractors and detail the circumstances that warrant a separate breach notification to be issued to the CMS.
CMS concurred with the recommendation, although did point out that the reporting requirements had been made clear in a 2006 State Medicaid Director Letter to Medicaid agencies and contractors.
The OIG report can be downloaded on this link (PDF, 2.1MB)
The post OIG Publishes 2016 Medicaid Data Breach Report appeared first on HIPAA Journal.