The Department of Health and Human Services’ Office for Civil Rights has announced its fourth largest HIPAA violation penalty has been issued to The University of Texas MD Anderson Cancer Center (MD Anderson). MD Anderson has been ordered to pay $4,348,000 in civil monetary penalties to resolve the HIPAA violations related to three data breaches experienced in 2012 and 2013.
MD Anderson is an academic institution and a cancer treatment and research center based at the Texas Medical Center in Houston, TX. Following the submission of three breach reports in 2012 and 2013, OCR launched an investigation to determine whether the breaches were caused as a result of MD Anderson having failed to comply with HIPAA Rules.
The breaches in question were the theft of an unencrypted laptop computer from the home of an MD Anderson employee and the loss of two unencrypted USB thumb drives, each of which contained the electronic protected health information (ePHI) of its patients. In total, the PHI of 34,883 patients was exposed and could potentially have been viewed by unauthorized individuals.
The investigation revealed that MD Anderson had conducted a risk analysis, as is required by HIPAA. That risk analysis revealed the use of unencrypted devices posed a serious threat to the confidentiality, integrity, and availability of ePHI. To address the risk, in 2006 MD Anderson developed policies that required all portable storage devices to be encrypted.
However, even though policies called for the use of encryption, encryption was not implemented until March 24, 2011. When encryption was implemented, it was not implemented on all portable devices in its inventory. MD Anderson reported to OCR that by January 25, 2013, it had only encrypted 98% of its computers. If MD Anderson had implemented encryption on all portable electronic devices containing ePHI, the three breaches would have been prevented.
Preventable Data Breaches Experienced by MD Anderson
The laptop was stolen from the home of Dr. Randall Millikan on April 30, 2012. Dr. Millikan confirmed that the ePHI on the device were not encrypted, the laptop was not password protected, and the ePHI could potentially have been viewed by family members at his home as a result, as well as by the individual who stole the laptop.
The USB devices were lost on or around July 12, 2012 and December 2, 2013. The first contained an Excel file containing the ePHI of 2,264 individuals. The device was lost by a summer intern on her way home from work. The second USB drive was lost by a visiting researcher from Brazil at some point over the Thanksgiving weekend. The device was usually left in the tray on her desk. Neither device was encrypted or password protected.
Between 2010 and 2011, MD Anderson’s Information Security Program and Annual Reports stated clearly that the storage of ePHI on mobile media was a key risk area that had not yet been mitigated, which was also detailed in its risk analysis for fiscal year 2011. That risk analysis determined that employees were downloading ePHI onto portable storage devices for use outside the institution. The failure to address the risk was a violation of 45 C.F.R. § 164.312(a)(2)(iv) and its own policies.
Penalties for HIPAA Violations
When financial penalties are deemed appropriate, OCR usually negotiates with the covered entity and a settlement is agreed; however, MD Anderson disagreed with OCR’s decision and maintained the financial penalty was unreasonable. Specifically, MD Anderson claimed that it was not obligated to use encryption as the data on the devices were used for research purposes, and that the research was not subject to HIPAA’s nondisclosure requirements. A covered entity has the right to contest penalties for HIPAA violations. Consequently, the matter was referred to an Administrative Law Judge.
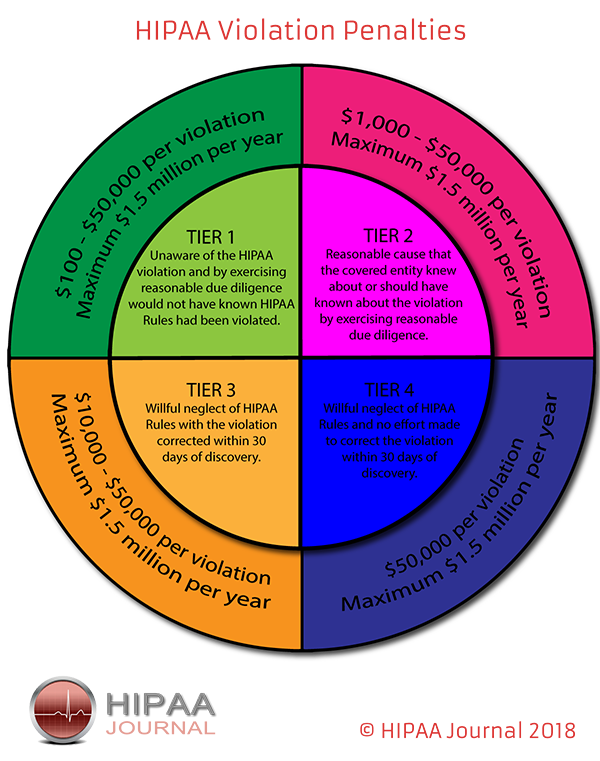
OCR proposed penalties for HIPAA violations under the tier of ‘reasonable cause’. OCR wrote in its Notice of Proposed Determination, “Reasonable cause is “an act or omission in which a covered entity or business associate knew, or by exercising reasonable diligence would have known, that the act or omission violated an administrative simplification provision, but in which the covered entity or business associate did not act with willful neglect.”
The penalty amounts in such cases are a minimum of $1,000 for each violation up to a maximum of $1.5 million per calendar year.
OCR determined penalties were appropriate for calendar year 2011 (283 days from March 24 to December 31), calendar year 2012 (366 days from January 1 to December 31) and calendar year 2013 (25 days from January 1 to January 25), and applied the maximum penalty of $1.5 million for each of those calendar years.
Administrative Law Judge Steven T. Kessell granted summary judgement in favor of OCR to remedy MD Anderson’s noncompliance with 45 C.F.R. § 164.312(a) – Technical Safeguards; encryption – and 45 C.F.R. § 164.502(a) – Uses and Disclosure of PHI; impermissible disclosure of ePHI.
“OCR is serious about protecting health information privacy and will pursue litigation, if necessary, to hold entities responsible for HIPAA violations,” said OCR Director Roger Severino. “We are pleased that the judge upheld our imposition of penalties because it underscores the risks entities take if they fail to implement effective safeguards, such as data encryption, when required to protect sensitive patient information.”
The post OCR Announces $4.3 Million Civil Monetary Penalty for University of Texas MD Anderson Cancer Center appeared first on HIPAA Journal.