A HIPAA violation refers to the failure to comply with HIPAA rules, which can include unauthorized access, use, or disclosure of Protected Health Information (PHI), failure to provide patients with access to their PHI, lack of safeguards to protect PHI, failure to conduct regular risk assessments, or insufficient employee training on HIPAA rules. To best answer the question what is a HIPAA violation, it is necessary to explain what HIPAA is, who it applies to, and what the definition of a HIPAA violation is; for although most people believe they know what a HIPAA compliance violation is, evidence suggests otherwise.
In this article we provide a detailed explanation of HIPAA violations.
 You can also use the article in conjunction with our HIPAA Violations Checklist to understand what is required to ensure full compliance. Please use the form on this page to arrange your free copy of the checklist.
You can also use the article in conjunction with our HIPAA Violations Checklist to understand what is required to ensure full compliance. Please use the form on this page to arrange your free copy of the checklist.
Summary Of Article Contents
HIPAA Violation Misunderstandings
The evidence that there may be a misunderstanding about what a HIPAA violation is comes from the Department of Health and Human Services (HHS) Enforcement Highlights web page. The web page is regularly updated with statistics relating to complaints about HIPAA violations, compliance reviews, and enforcement action.
According to the most recent update, the HHS has received almost 300,000 complaints since the compliance date of the Privacy Rule (April 2003). On its behalf, the Office for Civil Rights (OCR) has conducted tens of thousands of compliance reviews or intervened with technical assistance before a review was necessary.
However, in more than 200,000 cases, complaints received by HHS have not been reviewed by OCR for reasons such as the entity alleged to have violated HIPAA was not a HIPAA Covered Entity, or the alleged activity did not violate HIPAA rules. Additionally, in nearly 14,000 cases in which reviews were carried out, no violation of HIPAA was found.
While these statistics imply more than two-thirds of people do not understand what is a HIPAA violation, it is important to put the statistics into context as they only relate to complaints received by the HHS and do reflect complaints made directly to Covered Entities and State Attorney Generals by patients, plan members, and members of the workforce.. Nonetheless, it may be important for some to review their interpretation of what constitutes a violation.
What is HIPAA and Who Does It Apply To?
 The Health Insurance Portability and Accountability Act of 1996 (HIPAA) was introduced primarily to ensure employees could maintain healthcare coverage between jobs and not be discriminated against for pre-existing conditions. To prevent insurance carriers passing on the cost of compliance to plan members and employers, Congress added a second Title to the Act to simplify the administration of healthcare, eliminate wastage, and prevent healthcare fraud.
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) was introduced primarily to ensure employees could maintain healthcare coverage between jobs and not be discriminated against for pre-existing conditions. To prevent insurance carriers passing on the cost of compliance to plan members and employers, Congress added a second Title to the Act to simplify the administration of healthcare, eliminate wastage, and prevent healthcare fraud.
Since the passage of HIPAA, most of the regulatory activity has revolved around the Administrative Simplification provisions in 45 CFR Parts 160,162, and 164. These “Parts” include the General HIPAA Provisions, the Transaction and Code Sets Rules, and – most importantly in the context of what is a HIPAA violation – the publication of the Privacy Rule, the Security Rule, and Breach Notification Rule.
The failure to comply with any Standards in these Rules is considered a violation of HIPAA – even if no harm has resulted. For example, one of the most common types of complaint relates to the failure to provide patients with copies of their PHI on request. Examples of other types of HIPAA violations are provided below along with the penalties that may be applied when a violation of HIPAA occurs.
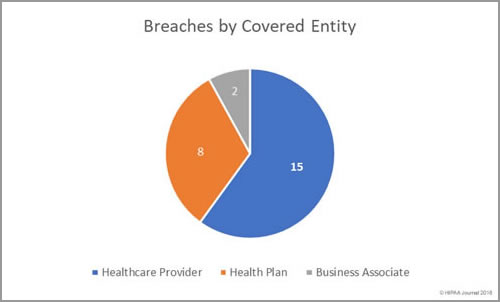
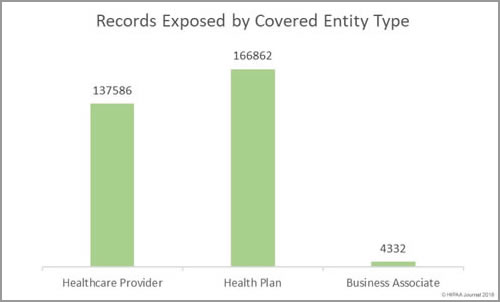
The Standards apply to Covered Entities and Business Associates. Covered Entities are defined as health plans, healthcare clearinghouses, and healthcare providers who electronically transmit PHI in connection with transactions for which HHS has adopted standards. Most healthcare providers qualify as a Covered Entity, but it is important to be aware that some are exempted.
Business Associates are businesses with whom a Covered Entity shares PHI to help carry out its healthcare activities and functions. Since the publication of the Final Omnibus Rule in 2013, Business Associates have had the same requirements as Covered Entities to comply with the Privacy, Security, and Breach Notification Rules as found in 45 CFR Parts 160, 162, and 164.
What is a PHI Violation?
Violations of HIPAA involving the unauthorized disclosure of PHI beyond the permitted uses and disclosures are the most common type of HIPAA violation. PHI violations can range from providing more information than the minimum necessary to achieve the purpose of an allowable disclosure to the hacking of an unencrypted database that exposes the PHI of thousands of patients.
To avoid a PHI violation, Covered Entities and Business Associates not only need to implement the safeguards stipulated by the Privacy and Security Rules, but also ensure appropriate policies and procedures are in place to minimize the risk of a PHI violation. Members of each entity´s workforce also need to be trained on the policies and procedures and the sanctions for non-compliance.
Other Types of HIPAA Law Violation
One frequent misunderstanding about HIPAA is that a violation is only a violation when it involves authorized uses and disclosures of PHI. However, there are many other ways in which a Covered Entity or Business Associate can violate HIPAA. For example, failing to train members of the workforce on policies and procedures or failing to document the training.
It is also a HIPAA law violation to withhold the details of a breach from the individuals affected by the breach, the HHS´ Office for Civil Rights, and – in certain circumstances – from the media. In recent years, several fines have been issued for HIPAA law violations attributable to non-compliance with the Breach Notification Rule or for failing to comply with the Rule in the time allowed.
Further HIPAA Violation Examples
In addition to the examples previously mentioned, there are many more ways in which Covered Entities and Business Associates can violate HIPAA. Below we list a selection of further HIPAA violation examples:
- Impermissible disclosures of PHI
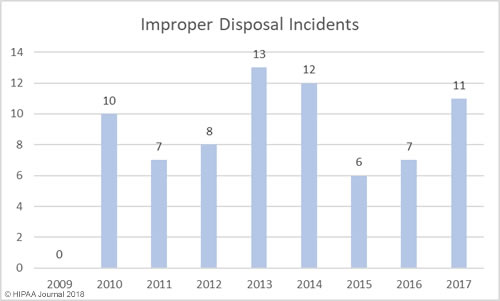
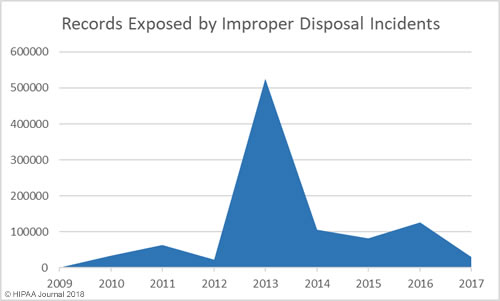
- Improper disposal of PHI
- Failure to conduct a risk analysis
- Failure to manage risks to the confidentiality, integrity, and availability of PHI
- Failure to implement safeguards to ensure the confidentiality, integrity, and availability of PHI
- Failure to maintain and monitor PHI access logs
- Failure to enter into a HIPAA-compliant Business Associate Agreement prior to sharing PHI
- Failure to provide patients with an accounting of disclosures on request
- Failure to implement access controls to limit who can view PHI
- Failure to terminate access rights to PHI when no longer required
- Failure to provide security awareness training
- Unauthorized release of PHI to individuals not authorized to receive the information
- Sharing of PHI online or via social media without permission
- Mishandling and mis-mailing PHI
- Texting unencrypted PHI
- Failure to encrypt PHI or use an alternative, equivalent measure to prevent unauthorized access/disclosure
It is important that anybody with access to PHI in an organization is provided with HIPAA training that explains what is a HIPAA violation and that all members of a Covered Entity´s or Business Associate´s workforce are provided with security awareness training regardless of their role.
How are HIPAA Violations Uncovered?
 Many HIPAA violations are discovered by HIPAA-covered entities through internal audits. Supervisors may identify employees who have violated HIPAA Rules and employees often self-report HIPAA violations and potential violations by co-workers.
Many HIPAA violations are discovered by HIPAA-covered entities through internal audits. Supervisors may identify employees who have violated HIPAA Rules and employees often self-report HIPAA violations and potential violations by co-workers.
The HHS’ Office for Civil Rights is the main enforcer of HIPAA Rules and investigates complaints of HIPAA violations reported by healthcare employees, patients, and health plan members. OCR also investigates all Covered Entities that report breaches of more than 500 records, conducts investigations into certain smaller breaches, and periodically audits HIPAA-covered entities and business associates.
State attorneys general also have the power to investigate breaches, and investigations are often conducted due to complaints about potential HIPAA violations and when reports of breaches of patient records are received.
What are the Penalties for Violations of HIPAA Rules?
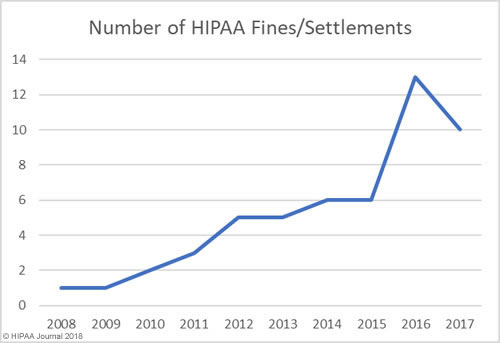
The penalties for violations of HIPAA rules are dependent on the nature of the violation, the level of culpability, how much harm was caused by the violation, and the efforts made by the Covered Entity or Business Associate to mitigate the breach or its impact. In most cases, the penalties consist of a Corrective Action Plan, but the OCR has the power to impose substantial financial penalties.
State attorneys general also have the power to investigate breaches, and investigations are often conducted due to complaints about potential HIPAA violations and when reports of breaches of patient records are received. These are in addition to any penalties for violations of HIPAA rules that are issued by individual states when data breaches violate state privacy and security rules.
HIPAA Violation Categories
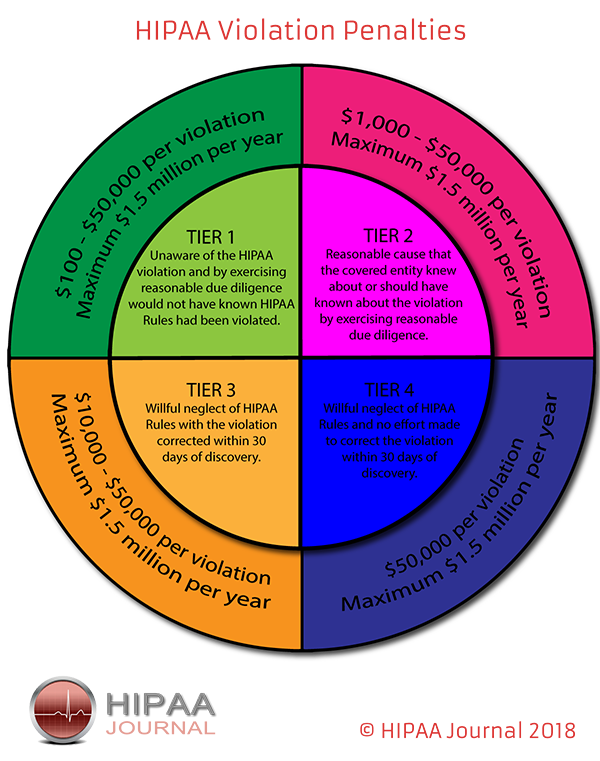
There are four HIPAA violation categories. Each has a minimum and maximum “limit” within which OCR can impose financial penalties depending on the level of culpability. Two of the HIPAA violation categories are designated for Covered Entities and Business Associates that can demonstrate reasonable due diligence, whereas the other two are for entities guilty of willful neglect.
Category 1 – Unaware of the HIPAA violation and by exercising reasonable due diligence would not have known HIPAA rules had been violated.
Category 2 – Reasonable cause that the Covered Entity/Business Associate knew about – or should have known about – the violation by exercising reasonable due diligence.
Category 3 – Willful neglect of the HIPAA Rules with the violation corrected and the consequences mitigated within thirty days of discovery.
Category 4 – Willful neglect of the HIPAA Rules and no effort made to correct the violation or mitigate the consequences within thirty days of discovery.
HIPAA Violation Penalties
Originally, the financial HIPAA violation penalties were modest and did not act as an appropriate deterrent to prevent HIPAA-covered entities from violating the HIPAA Rules. They were significantly increased in the HITECH Act of 2009; and, since 2015, they have been adjusted for inflation annually. The table below shows the HIPAA violation penalties for 2023 and includes the maximum an entity can be fined for multiple instances of the same violation. The cost-of-living adjustment multiplier is expected to be set by the Office of Management and Budget (OMB) by January 15, 2023.
| Penalty Tier |
Level of Culpability |
Minimum Penalty per Violation |
Maximum Penalty per Violation |
Annual Penalty Limit |
| Tier 1 |
Reasonable Efforts |
$137 |
$68,928 |
$2,067,813 |
| Tier 2 |
Lack of Oversight |
$1,379 |
$68,928 |
$2,067,813 |
| Tier 3 |
Neglect – Rectified within 30 days |
$13,785 |
$68,928 |
$2,067,813 |
| Tier 4 |
Neglect – Not Rectified within 30 days |
$68,928 |
$2,067,813 |
$2,067,813 |
OCR Reinterprets HITECH Act Penalty Increases
As the above table shows, the maximum penalty per year is the same in all four penalty tiers, which may seem odd. In 2019, the HHS reexamined the text of the HITECH Act and determined that the language had been misinterpreted with respect to the penalty amounts, and OCR determined that the maximum penalty per year should be reduced in three of the four penalty tiers, and set the annual cap at $25,000 for tier 1, $100,000 for tier 2, $250,000 for tier 3, and $1,500,000 for tier 4.
These new maximum penalties have not been made official, as that requires further rulemaking. While that does appear to be the intention of the HHS, this has currently been addressed through a notice of enforcement discretion, which applies indefinitely until the change to the penalty structure is made official. There is still a discrepancy between the maximum penalty per violation in tier 1, which is double that of the annual cap, which will no doubt be clarified in further rulemaking. Adjusted for inflation, the new penalty amounts for 2023, for cases assessed on or after October 6, 2023, are detailed in the table below.
| Annual Penalty Limit |
Annual Penalty Limit |
Minimum Penalty per Violation |
Maximum Penalty per Violation |
Annual Penalty Limit |
| Tier 1 |
Lack of Knowledge |
$137 |
$34,464 |
$34,464 |
| Tier 2 |
Reasonable Cause |
$1,379 |
$68,928 |
$137,886 |
| Tier 3 |
Willful Neglect |
$13,785 |
$68,928 |
$344,638 |
| Tier 4 |
Willful neglect (not corrected within 30 days |
$68,928 |
$68,928 |
$2,067,813 |
Recognized Security Practices
In 2021, the HITECH Act was amended to encourage HIPAA-regulated entities to adopt ´recognized security practices` to better protect healthcare data from unauthorized access. If those security practices have been adopted and have been in place continuously for 12 months, they will be considered by OCR when deciding on financial penalties and other actions in response to data incidents. HIPAA-regulated entities that adopt recognized security practices will not avoid financial penalties for HIPAA Security Rule violations, but they will be considered as a mitigating factor and will see any financial penalties reduced. By adopting recognized security practices, HIPAA-regulated entities will also be subjected to less extensive audits and investigations.
FAQs
How can you tell if an organization is in violation of HIPAA?
It is not always easy to tell if an organization is in violation of HIPAA if, as a health plan member or patient, you are unfamiliar with your rights or the permissible uses and disclosures of PHI. In most cases, individuals are not aware that an organization has been in violation of HIPAA until they receive a breach notification letter. However, if you are unsure about whether an organization is in violation of HIPAA, there are several steps you can take.
Health plan members and patients who believe their privacy may have been violated should, in the first instance, file a complaint with the organization concerned. The organization should acknowledge the complaint and respond with either an explanation of why your privacy was not violated or – if it was – an explanation of what the organization is doing to rectify the cause of the violation.
Complaints can also be filed with the HHS’ Office for Civil Rights or your state´s Attorney General. These agencies have the authority to review complaints against HIPAA covered entities and business associates; and, although it may take longer to get a reply, HHS´ Office for Civil Rights and state Attorneys General can thoroughly investigate if an organization is in violation of HIPAA and take action accordingly.
What is the difference between a risk assessment and a risk analysis?
The difference between a risk assessment and a risk analysis is that a risk assessment is generally regarded to be a review of potential threats, and a risk analysis a calculation of how likely the threats are to occur. There is a lack of clarity in HIPAA about the difference between a risk assessment and a risk analysis inasmuch as the risk analysis section of the Security Rule (45 CFR § 164.308(a)) states:
Covered entities and business associates must conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information held by the covered entity or business associate – i.e., the Rule requires an analysis of risks, but doesn´t elaborate on the analysis process.
Who can violate HIPAA?
Anyone covered by the HIPAA regulations can violate HIPAA. However, there has been some confusion – especially during the COVID-19 pandemic – about who exactly is covered by HIPAA. Entities required to comply with HIPAA are health plans, healthcare clearinghouses, and healthcare organizations that engage in qualifying electronic transactions (most now do). Business Associates and contractors with who PHI is shared can also violate HIPAA.
The requirement to comply with HIPAA regulations also applies to all workforces of a Covered Entity, Business Associate, or contractor. HIPAA defines a workforce as “employees, volunteers, trainees, and other persons whose conduct, in the performance of work for a Covered Entity or Business Associate, is under the direct control of such Covered Entity or Business Associate, whether or not they are paid by the Covered Entity or Business Associate”.
When potential risks and vulnerabilities are identified, what happens next?
When potential risks and vulnerabilities are identified, covered entities and business associates are required to implement security measures sufficient to reduce risks and vulnerabilities to a reasonable and appropriate level. In order to determine what constitutes a “reasonable and appropriate level”, organizations should take into account (per 45 CFR § 164.306(b)):
- The size, complexity, and capabilities of the organization
- The organization´s technical infrastructure, hardware, and software security capabilities
- The cost of reasonable and appropriate security measures
- The probability and criticality of potential risks to the integrity of ePHI
What does the “criticality of potential risks” mean?
The term criticality of potential risks refers to the scale of injury that might be caused by a HIPAA violation. For example, a cloud storage volume – containing the payment details and Social Security numbers of thousands of patients – left open to the public Internet has the potential to cause more injury than two nurses discussing the treatment options for patient A within earshot of patient B.
What is the HIPAA Law?
The term HIPAA Law refers to all five Titles of the Healthcare Insurance Portability and Accountability Act. The relevant Title for organizations in the healthcare industry is Title II – “Preventing Health Care Fraud and Abuse; Administrative Simplification; Medical Liability Reform” – as this is the section which led to the HIPAA Privacy, Security, and Breach Notification Rules.
What is considered a HIPAA violation?
A HIPAA violation is considered to be non-compliance with any “required” standard or any “addressable” standard for which an equally effective substitute has not been implemented, or a documented reason exists for the standard not to be implemented. An example of non-compliance with a required standard is failing to provide security awareness training to all members of the workforce regardless of their role.
Can a non-medical person violate HIPAA?
A non-medical person can violate because HIPAA applies to covered entities and business associates, and their workforces. Therefore, if a non-medical member of the workforce (such as a member of the IT team) disclosed PHI without authorization, they would be in violation of HIPAA – although it would be their employer who would have to notify the affected individual and report the disclosure to HHS´ Office for Civil Rights.
What are HIPAA violations?
HIPAA violations (in the plural) are a series of violations often attributable to the failure of a Covered Entity to monitor compliance with policies and procedures. There have been cases in which non-compliant short-cuts have been taken by employees “to get the job done”, and when shortcuts are unchecked, they can develop into a cultural norm of non-compliance.
Who can violate HIPAA laws?
Nobody can violate HIPAA laws, although there are many exceptions to HIPAA which mean covered entities and business associates do not have to comply with HIPAA in every circumstance. For example, under the Military Command Exception, healthcare professionals in the military are allowed to disclose PHI without the patient´s authorization in order to report on the patient´s fitness for duty, fitness to perform an assignment, or fitness to perform another activity necessary for a military mission.
What constitutes a HIPAA violation?
What constitutes a HIPAA violation is usually defined as any violation of the Privacy, Security, or Breach Notification Rules. Some violations – such as “incidental uses and disclosures” – would not generally result in financial penalties. Members of the workforce who violate HIPAA in this way are likely to be required to undergo further training.
What are the 3 types of HIPAA violations?
The 3 types of HIPAA violations are administrative, civil, and criminal violations. Most administrative HIPAA violations are investigated by the Centers for Medicare and Medicaid Services (CMS), while civil HIPAA violations are investigated by the HHS´ Office for Civil Rights (OCR). If the Office for Civil Rights investigates a case with possible criminal motives, the case is referred to the Department of Justice for investigation.
What violates HIPAA according to CMS?
What violates HIPAA according to CMS is the failure to comply with the Administrative Requirements (Part 162 of the Administrative Simplification Regulations). The Administrative Requirements cover the code sets and identifiers Covered Entities or Business Associates acting on their behalf must use when conducting transactions for which HHS has published standards. Although CMS has the authority to issue fines for non-compliance, to date, administrative HIPAA violations have been resolved by corrective actions, not financial penalties.
What counts as a HIPAA violation according to the FTC?
Nothing counts as a HIPAA violation according to the FTC. However, while the Federal Trade Commission (FTC) is not concerned with HIPAA enforcement, the agency does enforce the Federal Trade Commission Act, which has a Health Data Breach Rule that allows the FTC to pursue financial penalties for failures to issue breach notifications by vendors of personal health records and related entities not covered by HIPAA. In 2023, the FTC imposed its first financial penalty for failing to notify individuals about the impermissible disclosure of consumers’ health data to third parties, after a vendor promised such information would be kept private.
What is not a HIPAA violation?
The list of alleged violations that are not a HIPAA violation is very long indeed. More than two-thirds of complaints received by HHS´ Office for Civil Rights (OCR) alleging HIPAA violations are rejected after review because the complaints are made against organizations that are not subject to the HIPAA Rules or do not relate to an impermissible use or disclosure of Protected Health Information.
Can HIPAA violations be criminal?
A HIPAA violation can be criminal when an individual knowingly and wrongfully uses or discloses PHI in violation of §1320d-6 of the Social Security Act. Violations of this nature are most often referred to the Department of Justice, who has the authority to impose fines of up to $250,000 and pursue custodial sentences of up to ten years.
Does HIPAA apply to everyone?
HIPAA applies to everyone who is a member of a group health plan or who is a patient of a healthcare provider that qualifies as a covered entity inasmuch as it protects the privacy of these peoples´ individually identifiable health information and ensures the confidentiality, integrity, and availability of these peoples´ electronic Protected Health Information.
With regards to complying with the HIPAA Rules, HIPAA does not apply to everyone. Only “covered entities” and “business associates” with whom Protected Health Information is shared are required to comply with the HIPAA Rules. Members of the workforce for both types of organization have to comply with the policies and procedures developed by their employers to comply with HIPAA.
Can a patient violate HIPAA?
A patient cannot violate HIPAA because they do not qualify as a HIPAA covered entity, a business associate to a covered entity, or a member of the workforce. Even if a patient is employed by the hospital at which they are a patient, they cannot violate HIPAA because an employee is only a member of a covered entity´s workforce while “in the performance of work […] under the control of such covered entity”.
How do you report a HIPAA violation?
How you report a HIPAA violation can vary depending on whether you are a patient or group plan member, or a member of a covered entity´s or business associate´s workforce. If you are a patient or group plan member, you have the options of reporting a HIPAA violation to the Privacy Office where the violation occurred, to your state Attorney General, or to HHS´ Office for Civil Rights.
If you are a member of a covered entity´s or business associate´s workforce, who you report a HIPAA violation to may be determined by the content of your employment contract (i.e., an immediate supervisor). In the event of there being no reporting policy in the employment contract, your options are the same as a patient or group plan member.
What is the penalty for a HIPAA violation?
The penalty for a HIPAA violation depends on the nature of the violation, it´s consequences, the previous compliance history of the perpetrator, and whether the perpetrator is an organization or a member of an organization´s workforce.
If an organization, a minor HIPAA violation with minimal consequences will likely be resolved by technical assistance or a corrective action plan. If the violation is more serious, impacts thousands of individuals, and is a repeat offense, the likely penalty will be a civil monetary penalty.
If you are a member of an organization´s workforce, the penalty will depend on your employer´s sanctions policy. A minor violation may result in a verbal warning, while a more serious violation may result in a written warning – or, if a repeated serious violation, termination of employment.
What are the HIPAA violation categories?
The HIPAA violation categories are administrative violations, civil violations, and criminal violations. An example of an administrative violation would be to use the wrong codes on a claims transaction, while an example of a civil HIPAA violation would be to deny a patient access to a copy of their Protected Health Information (data breaches also fall into the category of civil HIPAA violations).
A criminal HIPAA violation is when a covered entity, business associate, or a member of either´s workforce has wrongfully and knowingly accessed, obtained, or transmitted Protected Health Information without authorization for a purpose prohibited by §1320d-6 of the Social Security Act. Criminal violations of HIPAA can incur substantial fines and jail sentences.
Is a HIPAA violation a felony?
A HIPAA violation is not a felony unless it involves the knowing and willful disclosure of PHI under false pretenses and/or to sell, transfer, or use the PHI for personal gain, malicious harm, or commercial advantage. These violations were classified as felonies in an opinion published by the Attorney General´s Office of Legal Counsel in 2005.
Can a family member violate HIPAA?
A family cannot violate HIPAA because family members are not required to comply with HIPAA. However, if a family member is employed at (for example) a hospital as a member of a covered entity´s workforce; and, while performing their role as a member of a covered entity´s workforce, accesses the medical history of a patient without authorization, this is a violation of HIPAA.
How long do you have to report a HIPAA violation?
How long you have to report a HIPAA violation can vary depending on who you report it to. Usually there are three options – to a Privacy Officer, to a State Attorney General, or to HHS´ Office for Civil Rights. Privacy Officers and State Attorney General can set their own time limits for how long you have to report a HIPAA violation. HHS´ Office for Civil Rights only accepts reports for 180 days after the date on which the violation was discovered.
What are the consequences of violating HIPAA?
The consequences of violating HIPAA depend on the nature of the violation, the impact the violation has, the violator´s previous compliance history, and whether the violator is an organization or a member of an organization´s workforce.
If an organization violates HIPAA, the consequences can range from voluntary compliance to technical assistance, to a corrective action plan, to a fine. Comparatively few violations of HIPAA result in a fine. Most are resolved by voluntary compliance and technical assistance.
If a member of an organization´s workforce violates HIPAA, the consequences will be determined by the organization´s HIPAA sanctions policy. These can range from a verbal warning to retraining, to a written warning, to termination of employment and possible loss of license.
My HIPAA rights were violated. Who do I complain to?
If your HIPAA rights were violated, you should complain to the Privacy Officer at the organization where your rights were violated. The contact details of the Privacy Office are on the Notice of Privacy Practices given to you when you first enrolled as a patient of a healthcare provider or as a member of a group health plan.
If you fail to obtain a satisfactory explanation of why your HIPAA rights were violated and what the organization is doing to prevent a repeat, you can complain to HHS´ Office for Civil Rights via the complaints portal. However, please note you only have 180 days from the date your HIPAA rights were violated to file your complaint.
Is violating HIPAA illegal?
Violating HIPAA is not illegal unless it involves one of the three offences that qualify as a misdemeanor or felony under §1320d-6 of the Social Security Act. All three offences relate to the knowing and wrongful disclosure of PHI, and it is rare these offenses occur. Therefore, practically all violations of HIPAA are civil violations.
What are 3 common HIPAA violations?
The 3 most common HIPAA violations according to HHS´ Enforcement Highlights report are impermissible uses and disclosures of PHI, a lack of safeguards for PHI, and the lack of patient access to PHI. Strictly speaking, these are the 3 most common alleged HIPAA violations; but it is highly likely the majority of allegations in each category are justified.
What happens if a doctor violates HIPAA?
What happens if a doctor violates HIPAA depends on whether the doctor is a covered entity, a member of a covered entity´s workforce, or a business associate providing a service on behalf of a covered entity.
With regards to the doctor being a covered entity, it is important to be aware not all healthcare provides qualify as covered entities. Those that do not qualify as a covered entity are not required to comply with HIPAA unless they provide a service for a covered entity as a business associate.
If a doctor is a covered entity in their own right (i.e., a solo practitioner), if HHS´ Office for Civil Rights investigates and identifies a compliance issue, it will usually attempt to resolve the issue with voluntary compliance or technical assistance. If the violation is serious – or the doctor has a history of non-compliance – the agency may impose a corrective action plan or civil monetary penalty.
If the doctor is a member of a covered entity´s workforce, the likely consequences of a minor HIPAA violation is a verbal warning and refresher training. However, if the doctor has a history of non-compliance, the warning could be written, and – if the violation is repeated – the covered entity could terminate the doctor´s employment and refer them to a medical licensing board.
A doctor that does not qualify as a covered entity but provides a service on behalf of a covered entity will only be required to comply with some standards of the Privacy Rule (usually determined by the content of the Business Associate Agreement). If the doctor violates a HIPAA standard they are required to comply with, the incident should be reported to the covered entity, who will investigate the violation or refer it to HHS´ Office for Civil Rights.
What is the penalty for violating HIPAA laws?
The penalty for violating HIPAA laws can depend on multiple factors. These include – but are not limited to – who committed the violation, what the consequences of the violation were, and the previous compliance history of the person or organization that violated HIPAA.
If, for example, a member of a covered entity´s workforce accidently revealed more than the minimum necessary PHI with limited consequences and it was their first violation, the penalty will likely be a verbal warning and possible a session of refresher training.
At the other end of the scale, if an organization with a poor compliance history is responsible for the knowing disclosure of PHI for commercial advantage, it could face multimillion dollar fines from HHS´ Office for Civil Rights, State Attorneys General, and the Department of Justice – who could also pursue a criminal conviction against the perpetrators with a potential jail term of up to ten years.
How does a HIPAA Privacy Rule violation differ from a HIPAA Security Rule violation?
A HIPAA Privacy Rule violation differs from a HIPAA Security Rule violation inasmuch as the objectives of the Privacy Rule are to protect the privacy of individually identifiable health information and give individuals rights over their health information, while the objective of the Security Rule is to ensure the confidentiality, integrity, and confidentiality of electronic Protected Health Information – which is a subset of individually identifiable health information.
Consequently, a HIPAA Privacy Rule violation is most likely to be the violation of a standard relating to permissible uses and disclosures of Protected Health Information or the failure to allow individuals to exercise their rights, whereas a HIPAA Security Rule violation is most likely to the violation of a standard relating to an Administrative, Physical, or Technology Safeguard – for example, the failure to prevent members of the workforce sharing login credentials.
Can I get fired for an accidental HIPAA violation?
You can get fired for an accidental HIPAA violation if, as a member of a covered entity´s or business associate´s workforce – you have a previous history of accidental HIPAA violations with significant consequences. However, unless your first accidental HIPAA violation had particularly significant consequences, and your employer´s sanctions policy included being fired for a first offense, you will likely be sanctioned with a verbal or written warning and required to take refresher HIPAA training.
How long does a HIPAA violation investigation take?
How long a HIPAA violation investigation takes can depend on a number of factors. If, for example, a healthcare worker has accidently violated a Privacy Rule standard and the consequences were minimal, a HIPAA violation investigation may take less than thirty minutes. However, if an investigation into a data breach by HHS´ Office for Civil Rights uncovers non-compliance in multiple areas, a HIPAA investigation could take months to conclude.
Can you sue for a HIPAA violation?
You cannot sue for a HIPAA violation under HIPAA laws because the regulations do not provide for a private right of action. However, if you have suffered harm as the consequence of a HIPAA violation, there may be other consumer protection or privacy laws you may be able to use to sue for a HIPAA violation against a negligent covered entity or business associate. Ideally, you should seek advice from a legal expert who is familiar with the laws in your state.
Do I need an attorney to report a HIPAA violation?
You do not need an attorney to report a HIPAA violation because the process for filing a complaint via the OCR complaints portal is straightforward. However, if you wish to pursue a civil claim for a violation of your privacy rights, it may be a good idea to speak with a HIPAA violation attorney before filing your complaint as HIPAA does not provide for a private right of action.
The post What is a HIPAA Violation? appeared first on HIPAA Journal.
 You can also use the article in conjunction with our HIPAA Violations Checklist to understand what is required to ensure full compliance. Please use the form on this page to arrange your free copy of the checklist.
You can also use the article in conjunction with our HIPAA Violations Checklist to understand what is required to ensure full compliance. Please use the form on this page to arrange your free copy of the checklist. The Health Insurance Portability and Accountability Act of 1996 (HIPAA) was introduced primarily to ensure employees could maintain healthcare coverage between jobs and not be discriminated against for pre-existing conditions. To prevent insurance carriers passing on the cost of compliance to plan members and employers, Congress added a second Title to the Act to simplify the administration of healthcare, eliminate wastage, and prevent healthcare fraud.
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) was introduced primarily to ensure employees could maintain healthcare coverage between jobs and not be discriminated against for pre-existing conditions. To prevent insurance carriers passing on the cost of compliance to plan members and employers, Congress added a second Title to the Act to simplify the administration of healthcare, eliminate wastage, and prevent healthcare fraud. Many HIPAA violations are discovered by HIPAA-covered entities through internal audits. Supervisors may identify employees who have violated HIPAA Rules and employees often self-report HIPAA violations and potential violations by co-workers.
Many HIPAA violations are discovered by HIPAA-covered entities through internal audits. Supervisors may identify employees who have violated HIPAA Rules and employees often self-report HIPAA violations and potential violations by co-workers.