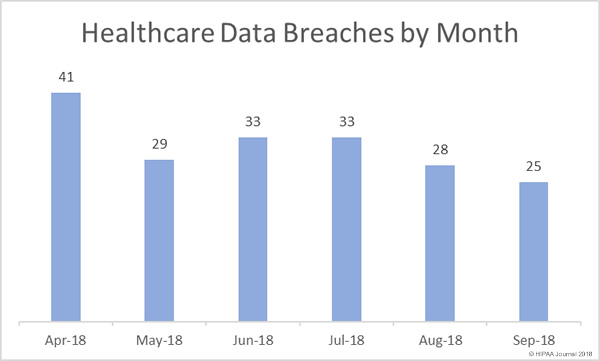
For the second consecutive month there has been a reduction in both the number of reported healthcare data breaches and the number of exposed healthcare records. In September, there were 25 breaches of 500 or more records reported to the Department of Health and Human Services’ Office for Civil Rights – the lowest breach tally since February.
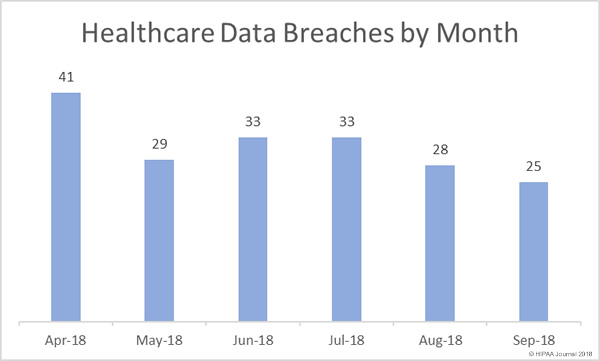
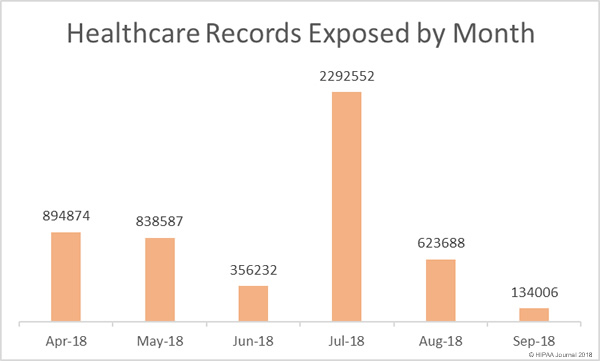
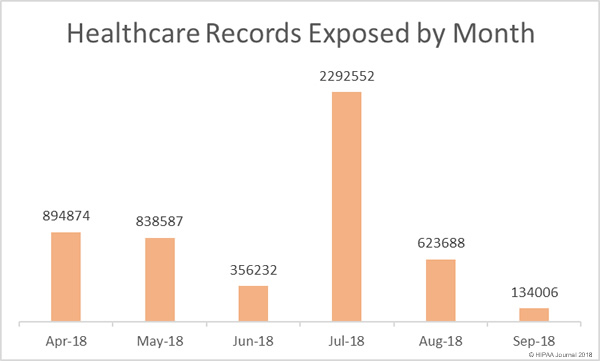
There was also a substantial reduction in the number of exposed/stolen healthcare records in September. Only 134,000 healthcare records were exposed/stolen in September – A 78.5% reduction in compared to August. Fewer records were exposed in September than in any other month in 2018.
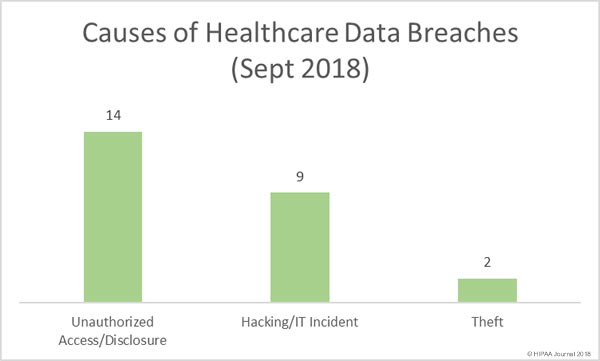
Causes of September 2018 Healthcare Data Breaches
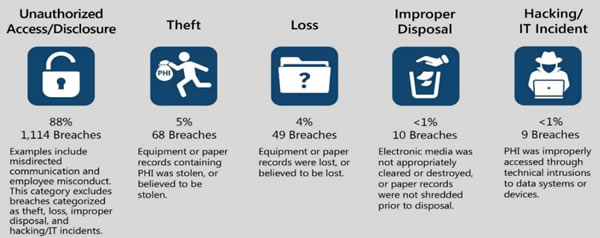
In August, hacking/IT incidents dominated the healthcare breach reports, but there was a major increase (55.55%) in unauthorized access/disclosure breaches in September, most of which involved paper records. There were no reported cases of lost paperwork or electronic devices containing ePHI, nor any improper disposal incidents.
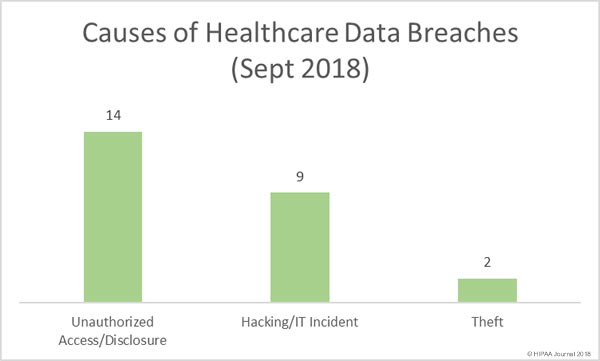
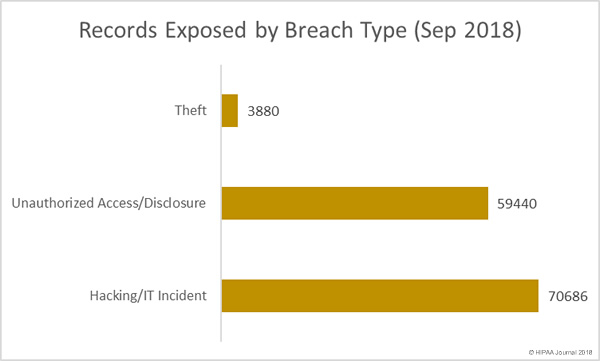
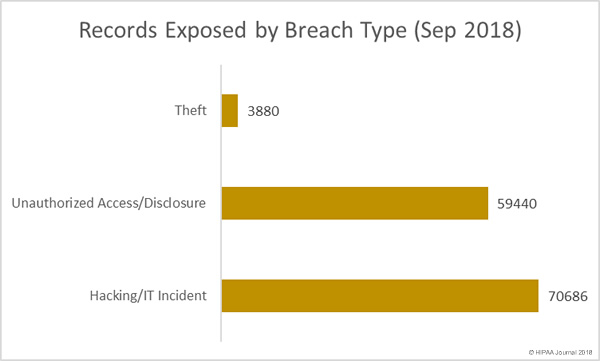
While there were fewer hacking/IT incidents than unauthorized access/disclosure incidents in September, they resulted in the exposure of more healthcare records. Six of the top ten healthcare data breaches in September were hacking/IT incidents.
Ten Largest Healthcare Data Breaches in September 2018
| Covered Entity |
Entity Type |
Records Exposed |
Breach Type |
Location of PHI |
| WellCare Health Plans, Inc. |
Health Plan |
26942 |
Unauthorized Access/Disclosure |
Paper/Films |
| Reliable Respiratory |
Healthcare Provider |
21311 |
Hacking/IT Incident |
Email |
| Toyota Industries North America, Inc. |
Health Plan |
19320 |
Hacking/IT Incident |
Email |
| Independence Blue Cross, LLC |
Business Associate |
16762 |
Unauthorized Access/Disclosure |
Other |
| Ransom Memorial Hospital |
Healthcare Provider |
14329 |
Hacking/IT Incident |
Email |
| Ohio Living |
Healthcare Provider |
6510 |
Hacking/IT Incident |
Email |
| University of Michigan/Michigan Medicine |
Healthcare Provider |
3624 |
Unauthorized Access/Disclosure |
Paper/Films |
| Reichert Prosthetics & Orthotics, LLC |
Healthcare Provider |
3380 |
Theft |
Other Portable Electronic Device |
| J.A. Stokes Ltd. |
Healthcare Provider |
3200 |
Hacking/IT Incident |
Desktop Computer, Electronic Medical Record, Network Server |
| J&J Medical Service Network Inc. |
Business Associate |
2500 |
Hacking/IT Incident |
Network Server |
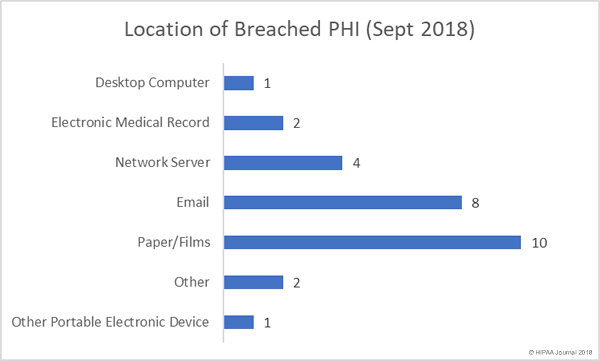
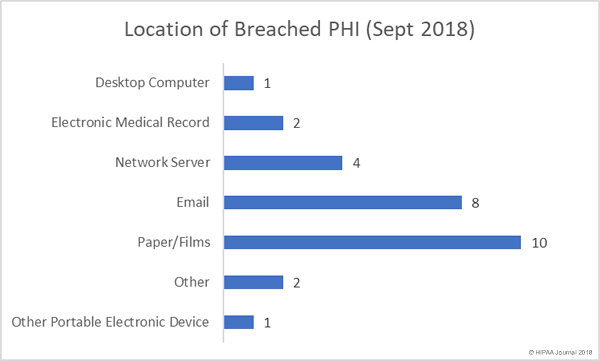
Location of Breached Protected Health Information
Over the past few months, email has been the most common location of breached PHI. September also saw a high number of email-related breaches reported – mostly due to phishing attacks – but the highest percentage of breaches involved paper records. There were 9 incidents involving unauthorized access/disclosure of paper records and one theft incident.
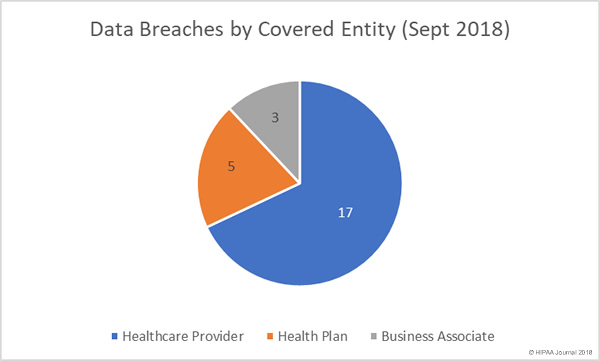
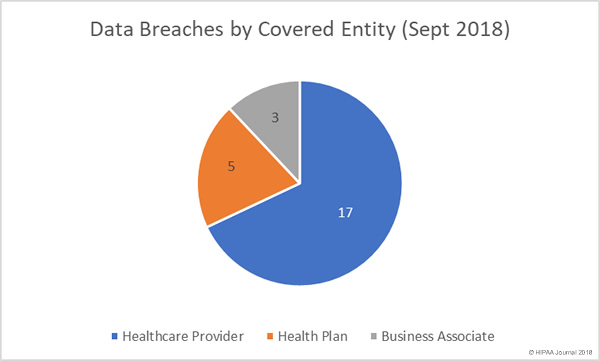
Data Breaches by Covered Entity Type
There was a 150% month-over-month rise in health plan data breaches in September, although healthcare providers were the worst affected with 17 healthcare data breaches reported in September 2018. While there were only 3 data breaches reported by business associates of HIPAA-covered entities, a further four breaches had some business associate involvement.
Healthcare Data Breaches by State
Healthcare organizations based in 18 states reported data breaches in September. Texas was the worst affected with four separate healthcare data breaches in September. There were three breaches reported by healthcare providers in Massachusetts and two reported breaches in California and Kansas. One breach was reported in Arizona, Colorado, Florida, Indiana, Michigan, Nebraska, New Jersey, Nevada, New York, Ohio, Oregon, Pennsylvania, Rhode Island, and Wisconsin.
HIPAA Enforcement Actions in September
After two months without any OCR financial penalties, OCR agreed settlements with three hospitals in September to resolve potential HIPAA violations. All three hospitals were alleged to have violated the HIPAA Privacy Rule by allowing an ABC film crew to record footage for the TV show “Boston Med.”
In all cases, OCR determined that patient privacy had been violated by allowing filming to take place without first obtaining patients’ consent. OCR also determined there had been failures to safeguard patients’ protected health information.
Massachusetts General Hospital agreed to a settlement of $515,000, Brigham and Women’s Hospital settled its case with OCR for $384,000, and Boston Medical Center paid OCR $100,000. New York Presbyterian Hospital had already settled its Boston Med-related case with OCR for $2.2 million in 2016.
State attorneys general also enforce HIPAA Rules and can issue fines for HIPAA violations. In September there was one settlement agreed with a state attorney general. UMass Memorial Health Care paid $230,000 to Massachusetts to resolve alleged HIPAA failures related to two data breaches that exposed the protected health information (PHI) of more than 15,000 state residents. In both cases, employees had accessed and copied PHI without authorization.
The post September 2018 Healthcare Data Breach Report appeared first on HIPAA Journal.