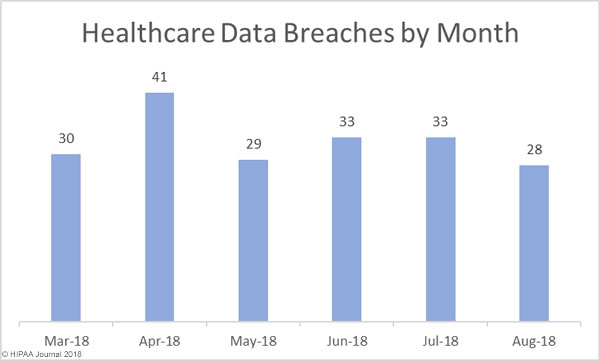
August was a much better month for the healthcare industry with fewer data breaches reported than in July. In August, 28 healthcare data breaches were reported to the HHS’ Office for Civil Rights, a 17.86% month-over-month reduction in data breaches.
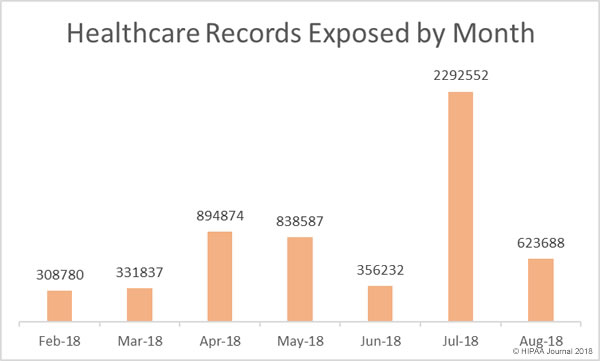
There was also a major reduction in the number of healthcare records that were exposed or stolen. In August, 623,688 healthcare records were exposed or stolen – A 267.56% reduction from August, when 2,292,522 healthcare records were breached.
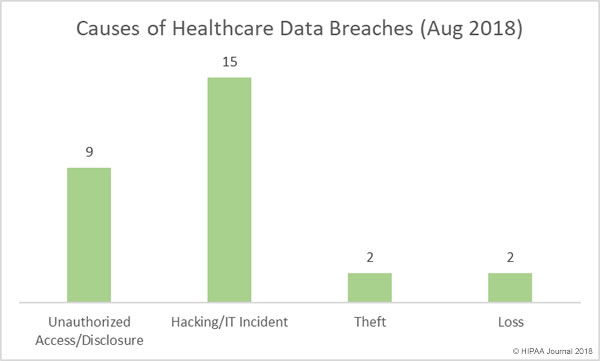
Causes of Healthcare Data Breaches in August 2018
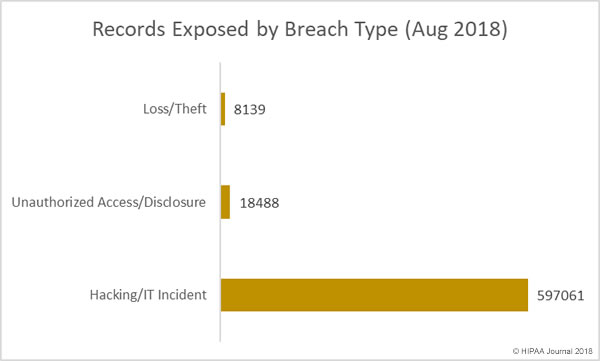
Hacking incidents dominated the breach reports in August, accounting for 53.57% of all reported data breaches and 95.73% of all records exposed or disclosed in August. Eight of the top ten breaches were the result of hacks, malware, or ransomware attacks.
Insider breaches are a major problem in the healthcare industry, more so than other verticals. In August there were nine insider breaches – 32.14% of the healthcare data breaches in August. Those breaches involved the unauthorized access or impermissible disclosure of 18,488 healthcare records – 2.96% of the monthly total.
There were two breaches involving the loss of PHI, one case of lost physical records and one lost portable electronic device containing electronic protected health information. The two theft incidents in August involved paper records.
Largest Healthcare Data Breaches in August 2018
| Name of Covered Entity | Covered Entity Type | Individuals Affected | Type of Breach |
| AU Medical Center, INC | Healthcare Provider | 417000 | Hacking/IT Incident |
| Fetal Diagnostic Institute of the Pacific | Healthcare Provider | 40800 | Hacking/IT Incident |
| Legacy Health | Healthcare Provider | 38000 | Hacking/IT Incident |
| Acadiana Computer Systems, Inc. | Business Associate | 31151 | Hacking/IT Incident |
| Carpenters Benefit Funds of Philadelphia | Health Plan | 20015 | Hacking/IT Incident |
| University Medical Center Physicians | Healthcare Provider | 18500 | Hacking/IT Incident |
| Simon Orthodontics | Healthcare Provider | 15129 | Hacking/IT Incident |
| Wells Pharmacy Network | Healthcare Provider | 10000 | Unauthorized Access/Disclosure |
| St. Joseph’s Medical Center | Healthcare Provider | 4984 | Loss |
| Central Colorado Dermatology, PC | Healthcare Provider | 4065 | Hacking/IT Incident |
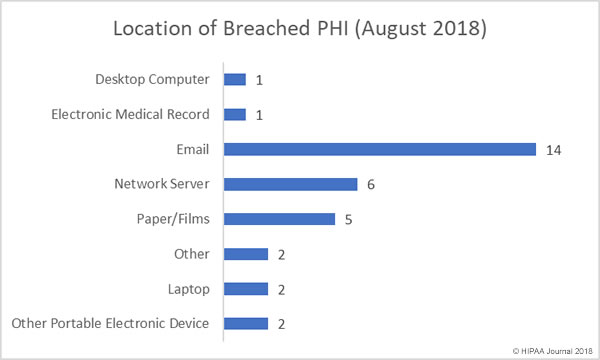
Location of Breached PHI
Email-related data breaches continue to dominate the healthcare data breach reports. A further 14 email-related data breaches were reported in August, the majority of which saw email accounts accessed by unauthorized individuals as a result of healthcare employees falling for phishing emails. Phishing attacks on healthcare providers are being reported regularly, highlighting just how important it is for healthcare organizations to provide ongoing security awareness training for employees to teach them the skills they need to identify phishing attempts.
There were six incidents involving PHI stored on network servers in August, including two confirmed ransomware attacks. There were five breaches involving paper records.
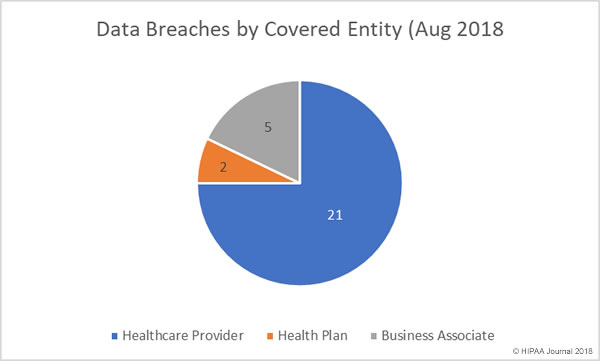
August Data Breaches by Covered Entity Type
Healthcare providers experienced the lion’s share of data breaches in August with 21 reported breaches. There were two health plan breaches and business associates of HIPAA-covered entities reported 5 breaches, with one further breach having some business associate involvement.
August Healthcare Data Breaches by State
Healthcare organizations based in 19 states experienced data breaches in August. While California and Texas usually top the list for data breaches due to the number of healthcare organizations based in those states, atypically, in August Oregon was the worst affected state with four breaches reported.
California and Florida each had three breaches reported, Colorado and Texas had two, and there was one breach reported in Arizona, Georgia, Hawaii, Illinois, Indiana. Louisiana, Maryland, Michigan, Nevada, New York, Ohio, Pennsylvania, Tennessee, and Virginia.
HIPAA Enforcement Actions in August
In 2016 and 2017, the HHS’ Office for Civil Rights took a hard line on enforcement of HIPAA Rules and agreed 21 settlements with HIPAA-covered entities and issued two civil monetary penalties. There have only been three financial settlements reached between OCR and HIPAA-covered entities in 2018 and no further fines or settlements were announced in August. While OCR enforcement activity appears to have slowed, that is not the case with state attorneys general, in particular New York. The New York attorney general’s office has agreed two settlements with HIPAA-covered entities in 2018 with a third agreed in August.
The Arc of Erie County resolved violations of HIPAA Rules and state laws by paying a penalty of $200,000 to the New York attorney general’s office following the exposure of 3,751 individual’s PHI. The PHI had been uploaded to a website and could be accessed without authentication.
The post August 2018 Healthcare Data Breach Report appeared first on HIPAA Journal.