The Department of Health and Human Services (HHS) Office for Civil Rights (OCR) has submitted its annual reports to Congress on compliance with the Health Insurance Portability and Accountability Act (HIPAA) and breaches of unsecured protected health information for calendar year 2024.
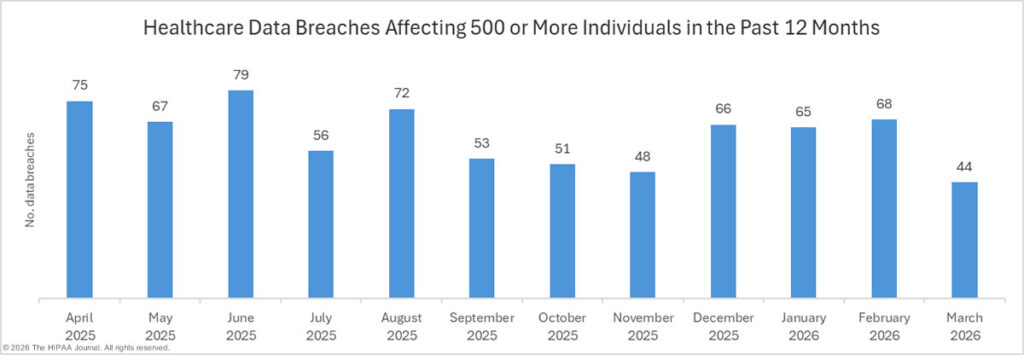
The reports are a requirement of the Health Information Technology for Economic and Clinical Health (HITECH) Act and provide a snapshot of the state of compliance in healthcare, the actions taken by OCR in response to potential noncompliance, and the extent to which sensitive health information is being exposed or stolen. The reports to Congress are based on the number of data breaches that occurred in each calendar year, not the year in which the data breach was reported. In calendar year 2024, OCR received 742 reports of data breaches affecting 500 or more individuals; however, only 663 reports related to breaches that occurred in 2024.
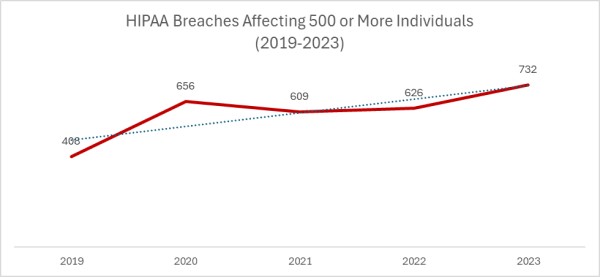
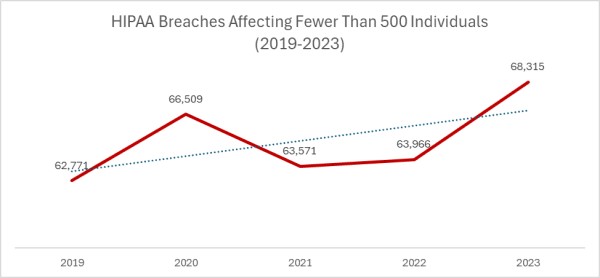
2023 was a particularly bad year for large healthcare data breaches. In its previous reports to Congress, OCR reported that 732 large data breaches occurred in 2023, a 17% increase from the previous year, with more than 113 million individuals affected. While there was an improvement in 2024 with 9% fewer large data breaches reported, an unprecedented number of individuals were affected by large data breaches, smashing the previous record. Across the 663 reported data breaches, the protected health information of 242,908,056 individuals was exposed or impermissibly disclosed. The massive total was largely due to a single data breach at Change Healthcare, which affected an estimated 192 million individuals. In 2024, OCR received 74,299 reports of data breaches affecting fewer than 500 individuals, although across those incidents, only 340,618 individuals were affected.
OCR investigates all large data breaches and opened investigations into all 663 breaches, plus two smaller data breaches. The vast majority of data breach investigations are resolved through voluntary corrective actions taken by the affected regulated entity or the provision of technical assistance. OCR resolved 785 data breach investigations in 2024, including 12 with resolution agreements, corrective action plans, and monetary settlements or civil monetary penalties. In 2024, OCR collected $7,813,831 in penalties to resolve alleged HIPAA violations uncovered through its investigations of data breaches, plus a further $950,000 penalty stemming from an investigation in response to media reports of a data breach.
| Year | Data Breaches (Under 500 individuals) | Percentage Change
(Under 500 individuals) |
Data Breaches (500+ individuals) | Percentage Change (500+ individuals) |
| 2024 | 74,299 | +9% | 663 | -9% |
| 2023 | 68,315 | +7% | 732 | +17% |
| 2022 | 63,966 | +15% | 626 | +3% |
| 2021 | 63,571 | -4% | 609 | -7% |
| 2020 | 66,509 | +6% | 656 | +61% |
| 2020 to 2024 | 12% increase | – | 1% increase | – |
Source: OCR reports to Congress (breaches each calendar year, irrespective of reporting date)
In the 2024 breaches of unsecured protected health information report, OCR explained that there is a continued need for HIPAA-regulated entities to improve compliance. Noncompliance with the HIPAA Rules is often identified. Many data breaches could have been prevented through proactive compliance, rather than addressing security issues after exploitation. Some of the most common areas of noncompliance were the risk analysis, risk management, information system activity review, audit controls, and person or entity authentication standards and implementation specifications of the HIPAA Security Rule.
If a risk analysis is incomplete or not conducted, risks are likely to persist unaddressed and can be exploited by threat actors. Risks also need to be reduced to a reasonable level to make it harder for threat actors to succeed. Access controls can prevent breaches as well as limit the harm caused if a network is breached. OCR’s investigations of data breaches found many instances of scant internal controls limiting lateral movement and excessive privileges for many user accounts, which allowed threat actors to gain access to multiple systems containing ePHI. OCR also commonly found weak authentication practices, such as default passwords and single-factor remote access, rather than multifactor authentication. Improving compliance across these areas would drastically reduce the number of large healthcare data breaches reported each year.
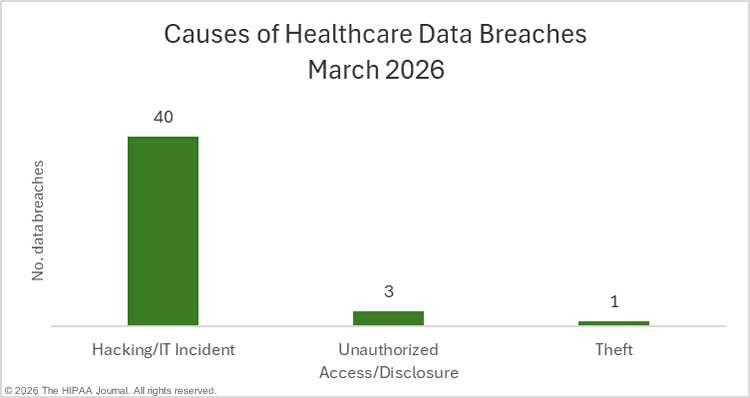
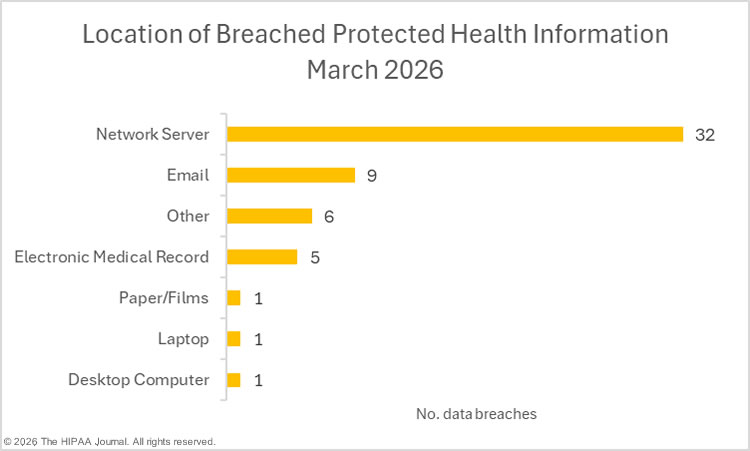
The most common cause of breaches, as has been the case for several years, was hacking/IT incidents, which accounted for 81% of all data breaches and 241,582,022 of the affected individuals (99.45%). The most common location of breached protected health information was network servers. For smaller breaches, the main cause was unauthorized access/disclosure incidents, most commonly involving paper/films.
Penalties to Resolve Alleged HIPAA Violations in Calendar Year 2024
| HIPAA-Regulated Entity | Penalty Type | Penalty Amount | Individuals Affected | Areas of Alleged HIPAA Noncompliance |
| Plastic Surgery Associates of South Dakota | Settlement | $500,000 | 10,226 | Risk analysis; security measures to reduce risks and vulnerabilities; reviews of records of information systems activity; policies and procedures to address security incidents |
| Providence Medical Institute | Civil Monetary Penalty | $240,000 | 85,000 across three ransomware attacks | Business associate agreement; policies and procedures to only allow authorized persons or software to access ePHI |
| Bryan County Ambulance Authority | Settlement | $90,000 | 14,273 | Risk analysis |
| Children’s Hospital Colorado | Civil Monetary Penalty | $548,265 | 14,210 across two email-related incidents | Risk analysis; workforce HIPAA Privacy Rule training. |
| Gulf Coast Pain Management Consultants | Civil Monetary Penalty | $1,190,000 | 34,310 | Risk analysis; review of records of activity in information systems; termination of access rights of terminated employees; procedures for establishing/modifying access rights to information systems. |
| Elgon Information Systems | Settlement | $80,000 | 31,248 | Risk analysis |
| Virtual Private Network Solutions | Settlement | $90,000 | At least 6,400 | Risk analysis |
| Northeast Surgical Group | Settlement | $10,000 | 15,298 | Risk analysis |
| Solara Medical Supplies | Settlement | $3,000,000 | 115,538 across two incidents | Risk analysis; breach notification letters to individuals, HHS, and media. |
| USR Holding | Settlement | $337,750 | 2,903 | Risk analysis; review of activity in information systems; procedures for creating and maintaining exact retrievable copies of ePHI; prevention of unauthorized access and deletion of ePHI. |
| Warby Parker | Civil Monetary Penalty | $1,500,000 | More than 197,986 individuals | Risk analysis; security measures to reduce risks and vulnerabilities; review of records of activity in information systems. |
| Health Fitness | Settlement | $227,816 | 4,304 | Risk analysis |
| Heritage Valley Health System | Settlement | $950,000 | Undisclosed | Risk analysis; contingency plan for emergencies; policies and procedures restricting access to ePHI |
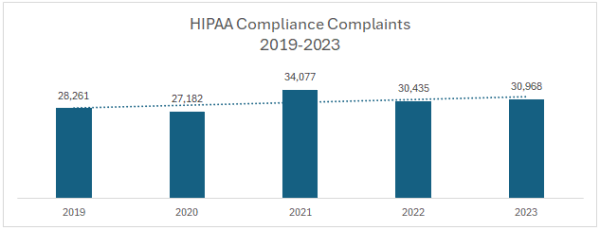
In calendar year 2024, OCR received 30,256 new complaints about potential violations of the HIPAA Rules and carried over 2,955 complaints from previous years. Out of those, OCR resolved 28,228 complaints, 17,466 without opening an investigation, and 9,392 were resolved through the provision of technical assistance.
Out of the 1,370 complaint investigations completed by OCR in 2024, around half (48%) required the regulated entity to take corrective action, and in 51% of the investigations, insufficient evidence was found to indicate violations of the HIPAA Rules. Nine complaint investigations were resolved with financial penalties totaling $1,180,781. The most common issues prompting complaints were impermissible uses and disclosures (660 complaints), Right of Access violations (541 complaints), missing general safeguards (481 complaints), lacking HIPAA Security Rule administrative safeguards (147 complaints), and missing or late individual breach notifications (122 complaints).
OCR initiated 730 compliance reviews and completed 797 compliance reviews in 2024 that did not arise from complaints. While OCR is required by the HITECH Act to conduct audits of HIPAA-regulated entities, no audits were initiated in 2024. OCR is also responsible for outreach activities to improve the education of the public with respect to their HIPAA Rights, and HIPAA-regulated entities about large data breach trends. OCR conducted 89 such outreach activities in calendar year 2024.
The report on compliance with the HIPAA Privacy, Security, and Breach Notification Rules shows there was a slight year-over-year decrease in complaints and a small increase in initiated compliance reviews.
| Year | Complaints received | YoY Percentage Change in Complaints | Initiated Compliance Reviews (including complaints and breaches) | YoY Percentage Change in Initiated Compliance Reviews |
| 2024 | 30,256 | – 2% | 797 | -3% |
| 2023 | 30,968 | + 2% | 773 | +14% |
| 2022 | 30,435 | -11% | 676 | + <1% |
| 2021 | 34,077 | +25% | 674 | -10% |
| 2020 | 27,182 | -4% | 746 | +22% |
| 2020 to 2024 | – | +11% | – | +7% |
Penalties Arising from Substantiated HIPAA Compliance Complaints in 2024
In total, OCR imposed 22 financial penalties to resolve HIPAA violations in calendar year 2024, 13 in response to reports of data breaches and 9 in response to complaints. In total, OCR collected $9,944,612 in settlements and penalties. Complaints resolved with financial penalties are detailed in the table below. Further information on each fine can be found on our HIPAA Violation Cases page.
| HIPAA-Regulated Entity | Penalty Type | Penalty Amount | Individuals Affected | Areas of Alleged HIPAA Noncompliance |
| Essex Residential Care dba Hackensack Meridian Health, West Caldwell Care Center | Civil Monetary Penalty | $100,000 | 1 | HIPAA Right of Access |
| American Medical Response | Civil Monetary Penalty | $115,200 | 1 | HIPAA Right of Access |
| Cascade Eye and Skin Centers | Settlement | $250,000
|
291,000 | Risk analysis; monitoring of information systems |
| Rio Hondo Community Mental Health Center | Civil Monetary Penalty | $100,000 | 1 | HIPAA Right of Access |
| Inmediata Health Group | Settlement | $250,000 | 1,565,338 | Risk analysis; monitoring of information systems |
| Holy Redeemer Hospital | Settlement | $35,581 | 1 | HIPAA Right of Access |
| Gums Dental Care | Civil Monetary Penalty | $70,000 | 1 | HIPAA Right of Access |
| South Broward Memorial Hospital District dba Memorial Healthcare System | Settlement | $60,000 | 1 | HIPAA Right of Access |
| Oregon Health and Science University | Civil Monetary Penalty | $200,000 | 1 | HIPAA Right of Access |
The post OCR Reports to Congress on HIPAA Compliance and Data Breaches in 2024 appeared first on The HIPAA Journal.