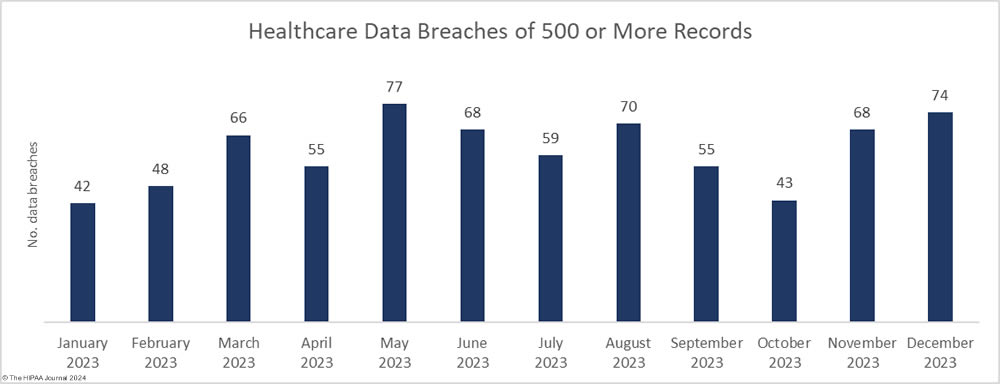
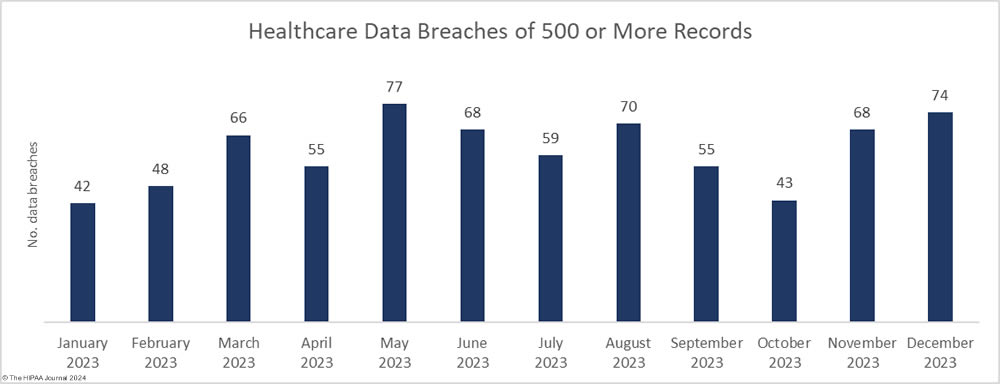
There was no letup in healthcare data breaches as the year drew to a close, with December seeing the second-highest number of data breaches of the year. The Department of Health and Human Services (HHS) Office for Civil Rights received 74 reports of healthcare data breaches of 500 or more records in December, which helped make 2023 a record-breaking year for healthcare data breaches. While there may still be some late additions to the list, as of January 18, 2023, 725 data breaches of 500 or more healthcare records have been reported to OCR in 2023 – The highest number since OCR started publishing records of data breaches on its “Wall of Shame.” To add some perspective, that is more than twice the number of data breaches that were reported in 2017.
It is not just the number of data breaches that is concerning. Healthcare data breaches have been increasing in severity and there have been ransomware attacks that have seen patients contacted and threatened directly with the exposure of their sensitive health data. Many of the data breaches reported in 2023 have been on a colossal scale, with December no exception with two multi-million-record data breaches reported.
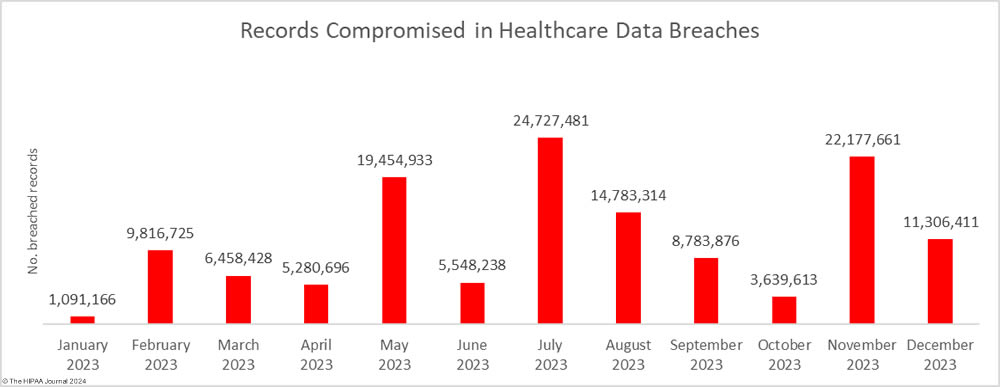
Since 2009, when OCR created its Wall of Shame, the number of breached records has been trending upwards, but even the most pessimistic of security professionals would not have predicted at the start of 2023 that there would be such a massive rise in breached records. 2021 was a bad year with 45.9 million records breached, and 2022 was worse with 51.9 million breached records, but in 2023, an astonishing 133 million records were exposed or stolen. On January 18, 2023, the OCR breach portal showed 133,068,542 individuals had their protected health information exposed or stolen in 2023.
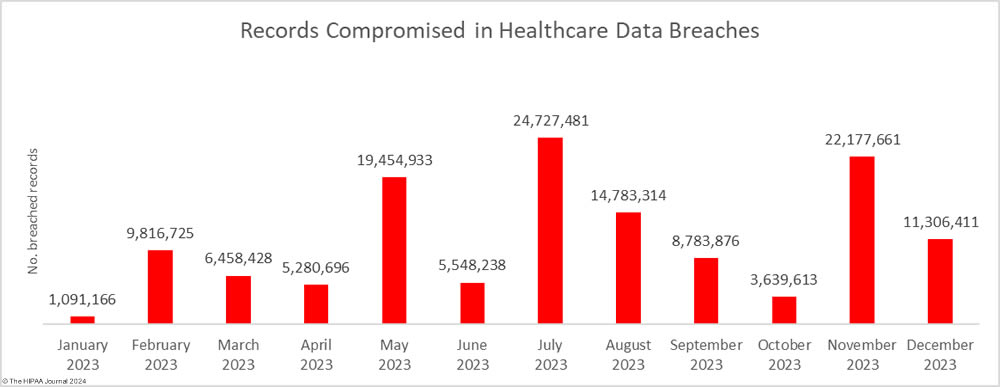
We will explore the year’s data breaches in greater detail and make predictions for the coming year in posts over the next few days but first, let’s take a dive into December’s data breaches to see where and how 11,306,411 healthcare records were breached.
The Biggest Healthcare Data Breaches in December 2023
Two of the largest data breaches of 2023 were reported in December, the largest of which occurred at the New Jersey-based analytics software vendor, HealthEC. Hackers gained access to a system used by more than 1 million healthcare professionals to improve patient outcomes. The platform contained the protected health information of 4,452,782 individuals. The data breach was the second in as many months to result in the exposure of the health data of more than 1 million Michigan residents, prompting the Michigan Attorney General to call for new legislation to hold companies accountable for breaches of healthcare data.
A 2.7 million-record data breach was reported by another business associate, ESO Solutions. ESO Solutions is a provider of software solutions for hospitals, health systems, EMS agencies, and fire departments, and had its network breached and files encrypted with ransomware. At least 12 health systems and hospitals are known to have been affected.
More than 900,000 records were obtained by hackers who gained access to an archive of data from the now defunct Fallon Ambulance Services, which was being stored to meet data retention requirements by Transformative Healthcare, and a cyberattack on Electrostim Medical Services exposed the data of almost 543,000 patients.
It has now been 7 months since the Clop hacking group exploited a zero-day vulnerability in Progress Software’s MOVEit Transfer solution and data breach reports continue to be issued. More than 2,600 organizations worldwide had data stolen in the attacks, with the healthcare industry among the worst affected.
| Name of Covered Entity |
State |
Covered Entity Type |
Individuals Affected |
Cause of Data Breach |
| HealthEC LLC |
NJ |
Business Associate |
4,452,782 |
Hacking incident (Data theft confirmed) |
| ESO Solutions, Inc. |
TX |
Business Associate |
2,700,000 |
Ransomware attack |
| Transformative Healthcare (Fallon Ambulance Services) |
MA |
Healthcare Provider |
911,757 |
Hacking incident (Data theft confirmed) |
| Electrostim Medical Services, Inc. dba EMSI |
FL |
Healthcare Provider |
542,990 |
Hacking incident |
| Cardiovascular Consultants Ltd. |
AZ |
Healthcare Provider |
484,000 |
Ransomware attack (Data theft confirmed) |
| Retina Group of Washington, PLLC |
MD |
Healthcare Provider |
455,935 |
Ransomware attack |
| CompleteCare Health Network |
NJ |
Healthcare Provider |
313,973 |
Ransomware attack (Data theft confirmed) |
| Health Alliance Hospital Mary’s Avenue Campus |
NY |
Healthcare Provider |
264,197 |
Hacking incident (Data theft confirmed) |
| Independent Living Systems, LLC |
FL |
Business Associate |
123,651 |
Hacking incident (MOVEit) |
| Pan-American Life Insurance Group, Inc. |
LA |
Health Plan |
105,387 |
Hacking incident (MOVEit) |
| Meridian Behavioral Healthcare, Inc. |
FL |
Healthcare Provider |
98,808 |
Hacking incident |
| Mercy Medical Center |
IA |
Healthcare Provider |
97,132 |
Hacking incident at business associate (PJ&A) |
| Pan-American Life Insurance Group, Inc. |
LA |
Business Associate |
94,807 |
Hacking incident (MOVEit) |
| Regional Family Medicine |
AR |
Healthcare Provider |
80,166 |
Hacking incident |
| HMG Healthcare, LLC |
TX |
Healthcare Provider |
80,000 |
Hacking Incident (Data theft confirmed) |
| Heart of Texas Behavioral Health Network |
TX |
Healthcare Provider |
63,776 |
Hacking incident |
| Kent County Community Mental Health Authority d/b/a Network180 |
MI |
Healthcare Provider |
59,334 |
Unauthorized email account access |
| Highlands Oncology Group PA |
AR |
Healthcare Provider |
55,297 |
Ransomware attack |
| Southeastern Orthopaedic Specialists, PA |
NC |
Healthcare Provider |
35,533 |
Ransomware attack (Data theft confirmed) |
| Eye Physicians of Central Florida, PLLC, a division of Florida Pediatric Associates, LLC |
FL |
Healthcare Provider |
31,189 |
Hacking incident (Data theft confirmed) |
| Clay County Social Services |
MN |
Business Associate |
22,005 |
Ransomware attack (Data theft confirmed) |
| Bellin Health |
WI |
Healthcare Provider |
20,790 |
Hacking incident |
| Neuromusculoskeletal Center of the Cascades, PC |
OR |
Healthcare Provider |
19,373 |
Unauthorized email account access |
| Independent Living Systems, LLC |
FL |
Healthcare Provider |
19,303 |
Hacking incident (MOVEit) |
| Community Memorial Healthcare, Inc. |
KS |
Healthcare Provider |
14,798 |
Hacking incident |
| VNS Choice dba VNS Health Health Plans |
NY |
Health Plan |
13,584 |
Unauthorized email account access |
| Hi-School Pharmacy |
WA |
Healthcare Provider |
12,779 |
Ransomware attack |
Many HIPAA-regulated entities keep information to the bare minimum in their breach reports, which allows them to meet legal requirements for breach reporting while minimizing the risk of disclosing information that could be used against them in class action lawsuits. The problem with this minimalistic breach reporting is the victims of the breach are not given enough information to accurately assess the risk they face, and the lack of transparency in data breach reporting makes it difficult to accurately assess how hackers are gaining access to healthcare networks and the nature of the attacks.
This is especially true for ransomware attacks and data theft/extortion attacks. Several breaches have been reported as hacking incidents where a possibility of unauthorized access to or theft of patient data, when the threat actors behind the attacks have claimed responsibility and have added the breached entity to their data leak sites. This trend has grown throughout the year.
December 2023 Data Breach Causes and Data Locations
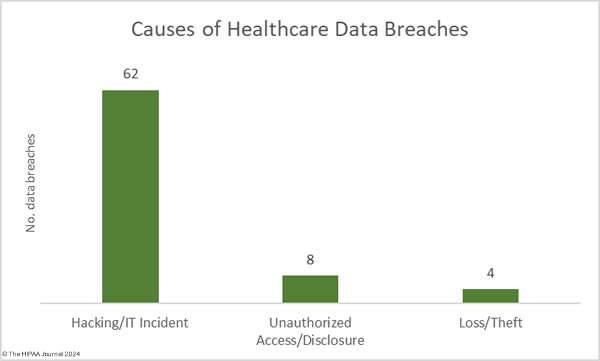
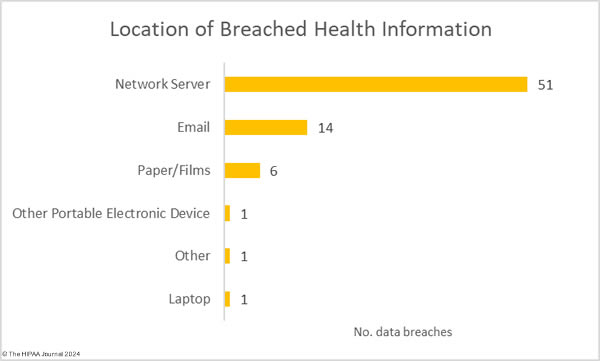
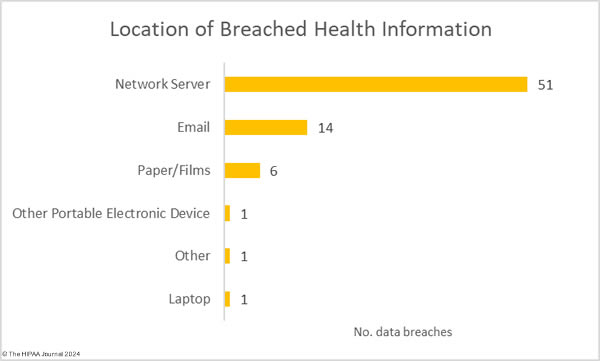
All of December’s data breaches of 10,000 or more records were hacking incidents, which accounted for 83.78% of the month’s 74 data breaches (62 incidents) and 99.79% of the month’s breached healthcare records (11,283,128 records). The average breach size was 181,986 records and the median breach size was 6,728 records. In 2009, hacking incidents accounted for 49% of all data breaches of 500 or more records. In 2023, hacking incidents accounted for 79.72% of all large data breaches. Something clearly needs to be done to improve resiliency to hacking and there are signs of action being taken at the state and federal level.
In December 2023, OCR published its Healthcare Sector Cybersecurity Strategy which details several steps that OCR plans to take to improve cyber resiliency in the healthcare sector and patient safety. The extent to which these plans will be made a reality will depend on Congress making the necessary funding available. OCR is planning a much-needed update to the HIPAA Security Rule in 2024 and has stated that it will establish voluntary cybersecurity goals for the healthcare sector. OCR will be working with Congress to provide financial assistance for domestic investments in cybersecurity to help cover the initial cost. The New York Attorney General has also announced that there will be new cybersecurity requirements for hospitals in the state after a significant increase in cyberattacks, and that funds have been made available to help low-resource hospitals make the necessary improvements.
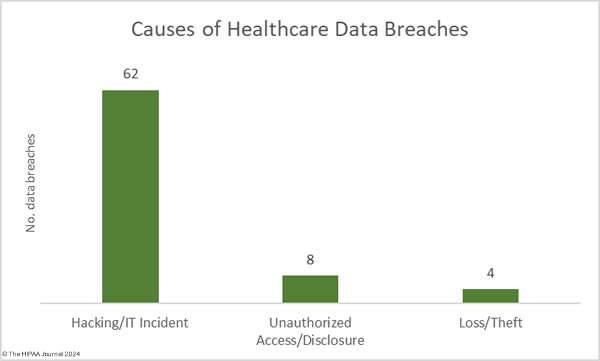
There were 8 data breaches classified as unauthorized access/disclosure incidents, involving 14,998 healthcare records. The average breach size was 1,875 records and the median breach size was 1,427 records. There were four loss/theft incidents reported in December, two of which involved stolen paperwork and two involved the loss of electronic devices, with the latter preventable if encryption had been used. 8,285 records were lost across these incidents.
The most common location of breached healthcare data was network services, which is unsurprising given the large number of hacking incidents. 14 data breaches involved protected health information stored in email accounts, three of which resulted in the exposure of more than 10,000 records.
Where did the Data Breaches Occur?
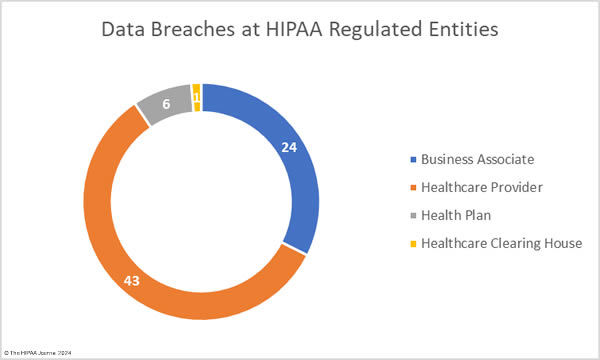
The raw data from the OCR data breach portal shows healthcare providers were the worst affected entity in December with 49 reported breaches of 500 or more records, followed by business associates with 13 breaches, health pans with 11, and a single breach at a healthcare clearinghouse. While healthcare providers suffered the most breaches, it was data breaches at business associates that exposed the most records. Across the 13 business associate-reported breaches, 7,416,567 records were breached, compared to 3,730,791 records in the 49 breaches at healthcare providers. The health plan breaches exposed 156,479 records and 2,574 records were exposed in the healthcare clearinghouse data breach.
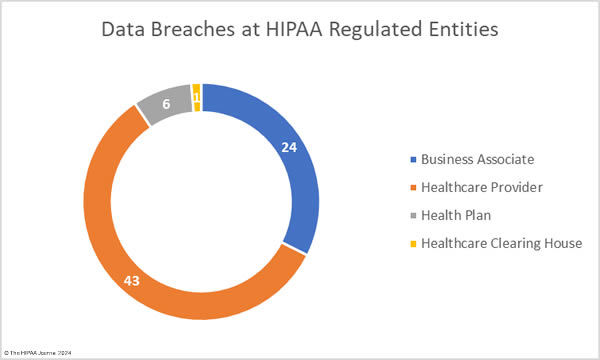
These figures do not tell the full story, as the reporting entity may not be the entity that suffered the data breach. Many data breaches occur at business associates of HIPAA-covered entities but are reported to OCR by the covered entity rather than the business associate. A deeper dive into the data to determine where the breach actually occurred reveals there were 24 data breaches at business associates (7,544,504 records), 43 data breaches at healthcare providers (3,616,078 records), 6 data breaches at health plans (143,255 records), and one breach at a healthcare clearinghouse (2,574 records).
The average size of a business associate data breach was 314,354 records (median: 2,749 records), the average size of a healthcare provider data breach was 84,095 records (median: 5,809 records), and the average health plan data breach was 23,876 records (median: 7,695 records). The chart below shows where the data breaches occurred rather than the reporting entity.
Geographical Distribution of Healthcare Data Breaches
HIPAA-regulated entities in 32 states reported data breaches of 500 or more records in December. California was the worst affected state with 85 large data breaches followed by New York and Texas with 7 reported breaches.
| State |
Number of Breaches |
| California |
8 |
| New York & Texas |
7 |
| Florida |
6 |
| Massachusetts |
4 |
| New Jersey, Tennessee & Wisconsin |
3 |
| Arkansas, Connecticut, Illinois, Kansas, Kentucky, Louisiana, Maryland, North Carolina & Washington |
2 |
| Alaska, Arizona, Colorado, Iowa, Michigan, Minnesota, Mississippi, Missouri, Montana, New Mexico, North Dakota, Oregon, South Carolina, Virginia & West Virginia |
1 |
HIPAA Enforcement in December 2023
OCR announced two enforcement actions against healthcare providers in December to resolve alleged violations of the HIPAA Rules. OCR continued its enforcement initiative targeting noncompliance with the HIPAA Right of Access with its 46th enforcement action over the failure to provide individuals with timely access to their medical records. Optum Medical Care of New Jersey settled its investigation and agreed to pay a financial penalty of $160,000 to resolve allegations that patients had to wait between 84 days and 231 days to receive their requested records when they should have been provided within 30 days.
OCR also announced its first-ever settlement resulting from an investigation of a phishing attack. Lafourche Medical Group in Louisiana suffered a phishing attack that resulted in the exposure of the protected health information of almost 35,000 individuals. While phishing attacks are not HIPAA violations, OCR’s investigation uncovered multiple violations of the HIPAA Security Rule, including no risk analyses prior to the 2021 phishing attack, and no procedures to regularly review logs of system activity before the attack. Lafourche Medical Group chose to settle the investigation and paid a $480,000 penalty.
These two enforcement actions bring the total number of OCR enforcement actions involving financial penalties up to 13, the lowest annual total since 2019, although there was a slight increase in funds raised from these enforcement actions with $4,176,500 collected in fines. OCR is pushing Congress to increase the penalties for HIPAA violations to make penalties more of a deterrent and also to provide much-needed funding to allow OCR to clear the backlog of HIPAA compliance investigations, in particular investigations of hacking incidents. Currently, OCR’s hands are tied, as the department’s budget has remained the same for years, aside from annual increases for inflation, yet its caseload of breach investigations has soared.
HIPAA Enforcement by State Attorneys General
State attorneys general have the authority to enforce HIPAA compliance and 2023 saw an increase in enforcement actions. The HIPAA Journal has tracked 16 enforcement actions by state attorneys general in 2023 that resolved violations of HIPAA or equivalent state consumer protection and data breach notification laws. In December, three enforcement actions were announced, two by New York Attorney General Letitia James and one by Indiana Attorney General Todd Rokita. New York has been particularly active this year having announced 4 settlements to resolve HIPAA violations in 2023 and the state also participated in two multi-state actions.
In December, AG James announced a settlement had been reached with Healthplex to resolve alleged violations of New York’s data security and consumer protection laws with respect to data retention, logging, MFA, and data security assessments which contributed to a cyberattack and data breach that affected 89,955 individuals. The case was settled for $400,000. AG James also investigated New York Presbyterian Hospital over a reported breach of the health information of 54,396 individuals related to its use of tracking technologies on its website, which sent patient data to third parties such as Meta and Google in violation of the HIPAA Privacy Rule and New York Executive Law. The case was settled for $300,000.
The Indiana Attorney General investigated CarePointe ENT over a breach of the health information of 48,742 individuals. AG Rokita alleged that CarePointe ENT was aware of security issues several months before they were exploited by cybercriminals but did not address them in a timely manner. There was also no business associate agreement with its IT services provider. The investigation was settled for $125,000.
The data for this report was obtained from the U.S. Department of Health and Human Services’ Office for Civil Rights on January 18, 2023.
The post December 2023 Healthcare Data Breach Report appeared first on HIPAA Journal.