How to Become OSHA Compliant
The summarized way to become OSHA compliant is to establish which OSHA standards apply to your business, conduct a risk assessment to identify threats to safety and health, and abate identified threats as necessary.
What is OSHA Compliance?
OSHA compliance is complying with all applicable workplace standards promulgated by the federal Occupational Safety and Health Administration or an OSHA-approved state plan to promote safe and healthy workplaces. Most businesses are required to comply with “General Industry” standards, but there are separate standards for the agriculture, maritime, and construction industries.
The OSHA standards for General Industry cover everything from safe working surfaces and workplace ventilation to exposure limits for hazardous substances and chemicals. There are also standards governing hazard communication, injury and illness recordkeeping, and workforce training. The failure to comply with any applicable safety, health, or administrative standard is a violation of OSHA.
What Happens if You Violate OSHA?
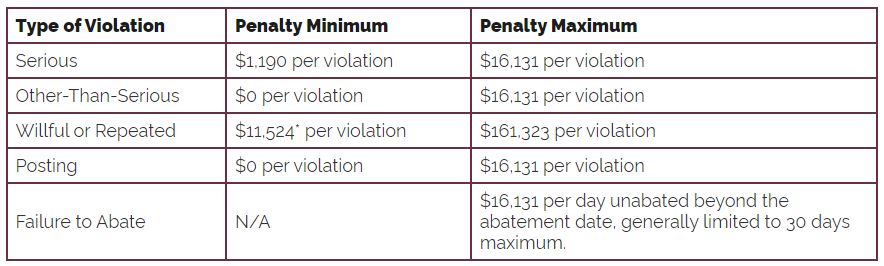
What happens if you violate OSHA depends on the nature of the violation and its outcome. OSHA has a four-tier penalty structure which, at the lowest level, allows inspectors to cite a business for an OSHA violation and give the business time to abate it. If the reason for the violation is not abated in the stated time – or the violation is more serious in nature – OSHA can impose financial penalties.
If a business willfully neglects to mitigate threats to safety and health to an acceptable level – and a member of the workforce suffers a fatal injury as a result – OSHA can refer the case to the Department of Justice to pursue a criminal conviction. If found guilty, negligent employers and safety managers can be fined up to $1 million and sentenced to up to twenty years in jail.
How to Become OSHA Compliant in More Detail
In the introduction, the way to become OSHA compliant was summarized in three stages. While this is an accurate explanation of how to become OSHA compliant, some businesses may require more details. OSHA recommends a seven step process for businesses in the “General Industry” category to become OSHA compliant which consists of:
Identify Standards that Apply to Most Businesses
These include standards relating to safe working surfaces, workplace ventilation, fire safety, exit routes, and hazard communication. Businesses should read these standards, conduct a risk assessment to ensure the standards are being complied with, and implement measures to correct violations and mitigate threats to workforce safety and health.
Identify Standards that Apply to Your Business
For business in the healthcare industry, standards to consider could include the bloodborne pathogens standard, the ionizing radiation standard, and the exposure to formaldehyde standard. It will also be necessary for businesses in the healthcare industry to familiarize themselves with OSHA’s permissible exposure limits for hazardous substances.
Survey the Workplace for Additional Hazards
All organizations have to comply with OSHA’s General Duty clause which requires employers to provide a work environment free from recognized hazards not otherwise covered by an OSHA standard. In the healthcare industry, this clause would cover activities such as safe patient handling, protection from infectious diseases, and preventing workplace violence.
Develop a Workplace Safety and Health Plan
Becoming OSHA compliant is one thing. Remaining OSHA compliant is another. Therefore businesses need to develop a workplace safety and health plan which schedules frequent inspections, includes a process for members of the workforce to report hazards to safety managers , and delegates the responsibilities for documenting and abating reported hazards.
Train Members of the Workforce
Some OSHA standards require members of the workforce to undergo OSHA training before being exposed to a hazard for the first time, while others require initial training AND annual refresher training – for example, the bloodborne pathogens standard. All workforce training should be documented and retained in the event of a subsequent OSHA inspection.
Recordkeeping, Reporting, and Posting
In addition to the documentation of hazard reports and workforce training, businesses are required to keep records of all workplace injuries and illnesses, submit injury and illness data to OSHA annually, report fatalities and severe injuries, and post copies of citations when issued. Note: some State-approved OSHA Plans have more stringent reporting requirements.
Ask for Compliance Assistance when Necessary
The final step in the process to become OSHA compliant is to ask for help if you need it. There are multiple resources on the Help pages of OSHA’s website and third party resources that can help businesses become OSHA compliant. Alternatively, you can call your local OSHA Office to see if your business qualifies for a free onsite consultation.
Related Content
How Can You File a Report with OSHA
The post How to Become OSHA Compliant appeared first on HIPAA Journal.
What is Healthcare Compliance Tracking Software? – HIPAA Journal
What is Healthcare Compliance Tracking Software?
Healthcare compliance tracking software is a tool that helps healthcare organizations keep compliance programs on schedule by automating the management of activities such as risk assessments, policy and procedure reviews, workforce training, and incident management. When used effectively, healthcare compliance tracking software can help organizations avoid legal risks, better protect the privacy and security of health information, and improve the quality of patient care.
Healthcare organizations have a lot of regulations and standards to comply with. Not only are most healthcare organizations required to comply with HIPAA, OSHA, and FDA regulations, but they might also have to meet CMS’ conditions for participation in Medicare, the voluntary standards for Joint Commission accreditation, and industry-specific or role-specific state licensing requirements.
In addition, if a healthcare organization operates in a state that has passed a data privacy law that does not exempt HIPAA covered entities and business associates, there may be occasions in which a provision of a state data privacy law preempts a provision of HIPAA – notwithstanding that some states exempt Protected Health Information, but not other types of identifiable information.
As a consequence of multiple regulations and standards, it is often difficult to keep on top of compliance activities. Even the best planned health compliance programs can be thrown off-schedule by an unforeseen event – for example, the recent guidance that using tracking technologies on user-authenticated healthcare web pages could be a HIPAA violation.
How Healthcare Compliance Tracking Software can Keep Programs on Schedule
Healthcare compliance tracking software works by tracking program initiatives and activities to alert compliance teams when risk assessments are due for review, when policies and procedures need revising, and when workforce training needs to be provided or repeated – or, in the case of a security awareness training program, when the program needs to be updated to reflect emerging threats.
The same capabilities can be configured to manage Business Associate Agreements and the retention of compliance documentation, and to produce reports for upper management to show the value of investing in healthcare compliance tracking software. In some cases, the value of the investment can be that it is possible to demonstrate a good faith effort to comply with regulations and standards.
Thereafter – depending on the compatibility of the software with an existing IT infrastructure – healthcare compliance tracking software can be used to manage incident responses (i.e., compliance with the HIPAA Breach Notification Rule) or ensure corrective action plans remain on schedule to avoid an extension of the plan or a civil financial penalty for failing to comply with the plan.
The Benefits of Tracking Compliance Activities with Automation
The primary benefit of tracking compliance activities with automation is that healthcare compliance tracking software reduces the likelihood of human error due to an oversight or misinterpretation of a compliance activity. This reduces the likelihood of non-compliance and the consequences of non-compliance such as remedial action, legal risks, and financial costs (both direct and indirect costs).
In addition, by mitigating the risk that compliance activities will fall behind schedule, healthcare compliance tracking software helps better protect the privacy and security of health information. The benefit of this is that, when patients believe their health information will remain confidential, they are more likely to share details of their health conditions with healthcare providers.
With more information available to them, healthcare providers can make better informed decisions about diagnoses and treatment plans, which improves the quality of patient care and leads to better patient outcomes. Better patient outcomes not only reduce healthcare costs, but can improve staff morale and retention – saving healthcare organizations staff recruitment and training costs.
The above is just a snapshot of the capabilities and benefits of healthcare compliance tracking software. If you would like to know more about tracking compliance activities with automation, or developing a compliance program that accounts for the variety of regulations and standards, it is advisable to speak with a healthcare compliance expert.
The post What is Healthcare Compliance Tracking Software? appeared first on HIPAA Journal.
71% of Ransomware Attack Victims Refuse to Pay the Ransom – HIPAA Journal
71% of Ransomware Attack Victims Refuse to Pay the Ransom
The latest data from the ransomware remediation firm, Coveware, shows the number of victims of ransomware attacks choosing to pay the ransom has fallen to a record low. At the start of 2019, 85% of victims of ransomware attacks paid a ransom following an attack, by the middle of 2021 the percentage had fallen to 46%, and in Q4, 2023, only 29% of victims paid the ransom. In 2019, ransomware groups started engaging in double extortion tactics, where access is gained to victims’ networks and data is exfiltrated before file encryption. Ransom payments are required to obtain the keys to decrypt files and to prevent stolen data from being leaked or sold. For many victims, the main reason for paying the ransom was to prevent a data leak rather than to obtain the keys to decrypt files. Coveware reports that in ransomware attacks involving data theft, in Q3, 2023, only 26% of victims paid the ransom.
There are many reasons behind the steady decline in ransom payments. One of the main factors is better preparedness, such as ensuring that a backup is made of all sensitive data and the backup is stored securely in an air-gapped system where it cannot be encrypted in an attack. In attacks where there is data theft, paying the ransom could prevent a data leak or the sale of the data; however, ransomware groups are not trusted to delete the stolen data. There have been attacks where payment of the ransom has not prevented a data leak, and paying up has led to further extortion attempts and attacks. There has also been a law enforcement crackdown and in some regions, paying a ransom is now illegal.
Prohibiting ransomware payments is one of the measures being considered by governments to curb attacks. If paying a ransom to a ransomware group is prohibited, ransomware groups would, in theory, stop conducting attacks in that country. Coveware suggests the reality would be different. The attacks would likely continue and companies would stop reporting attacks and seeking assistance from law enforcement. It would become much harder to track ransomware attacks and law enforcement investigations of ransomware groups would be severely hampered. All the good work by law enforcement to encourage victims to report attacks would be undone and as soon as a ban is implemented, a large illegal market would be created.
In the United States, several states have imposed partial bans on ransom payments, such as prohibiting state agencies and organizations from paying ransoms yet these bans do not appear to be having the desired effect, as ransomware attacks in those states have not reduced. Coveware believes that banning ransom payments amounts to capitulation. “A ban would signal that as a country, we are admitting that we are incapable of defending ourselves. That we are helpless against the threat of cyber extortion.”
Coveware’s data shows the efforts made by companies to prepare for ransomware attacks have paid off. Enterprises are no longer being crippled by file encryption and can recover their data without paying the ransom, and the efforts of law enforcement to disrupt and dismantle ransomware groups have produced meaningful results. “This fight will not be won overnight. It will take years, but the fight IS winnable,” said Coveware.
With revenues from ransomware attacks falling, ransomware groups need to conduct more attacks or increase their ransom demands, but Coveware’s data shows that ransom payments have reduced. In Q4, 2023, the average ransom payment was $568,705, down 33% from Q3, 2023. The median payment in Q4, 2023 was unchanged from the previous quarter and remained at $200,000.
In Q3, 2023 there was little change in the most active ransomware groups, with Akira retaining the top spot with 17% of attacks, followed by Blackcat with 10%, LockBit with 8%, and Play Ransomware with 6%; however, there has been an increase in activity by smaller ransomware groups and non-affiliated lone wolf actors. In around one-third of attacks, the method used to gain initial access to victims’ networks was unknown. Out of the other attacks, RDP compromise was the most common and has been increasing since Q3, 2022. Email phishing was the second most common initial access vector, although the popularity of this method declined over the same period. The exploitation of software vulnerabilities was the third most common initial access vector, with the Cisco ASA vulnerability (CVE-2023-20269) one of the most commonly exploited vulnerabilities.
Between Q2, 2022, and Q2, 2023, ransomware gangs favored attacks on large companies but the average size of victim companies has been falling with medium-sized companies seen as the sweet spot. Attacks are easier to conduct as investment in cybersecurity is lower than at large firms and mid-sized companies have sufficiently large revenues to allow large ransom demands to be issued. In Q4, 2023, the average size of a victim company was 231 employees, down 32% from Q3, 2023. In Q4, 2023, 22.2% of attacks were on companies in the professional services sector, with healthcare the second most attacked industry with 16% of attacks, followed by the public sector with 11.1% of attacks.
The post 71% of Ransomware Attack Victims Refuse to Pay the Ransom appeared first on HIPAA Journal.
Keenan & Associates Data Breach Affects More Than 1.5 Million Individuals – HIPAA Journal
Keenan & Associates Data Breach Affects More Than 1.5 Million Individuals
The Torrance, CA-based insurance broker Keenan & Associates has recently reported a cybersecurity incident to the Maine Attorney General that has affected 1,509,616 individuals. Keenan & Associates is part of AssuredPartners NL, one of the largest brokerage firms in the United States. The company has clients across a variety of industries, including healthcare, education, and the public sector.
The cybersecurity incident was detected on Sunday, August 27, 2023, when some of its network servers were disrupted. Action was immediately taken to contain the attack and isolate the affected network servers and third-party cybersecurity experts were engaged to investigate to determine the nature and scope of the unauthorized activity. The forensic investigation confirmed that there had been unauthorized access to its internal systems at various points between August 21, 2023, and August 27, 2023, and during that time, certain files were exfiltrated from its systems. Some of those files contained personal data provided by its clients along with some employee data. The review of those files confirmed they contained names in combination with one or more of the following: date of birth, Social Security number, passport number, driver’s license number, health insurance information, and general health information.
Keenan & Associates said additional security protocols have been implemented to enhance network, data, and system security, and its security measures will continue to be evaluated to determine if further steps need to be taken to harden cybersecurity defenses. The incident has also been reported to the Federal Bureau of Investigation (FBI) and Keenan & Associates has been assisting the FBI with its investigation.
While data theft was confirmed, Keenan & Associates is unaware of any actual or attempted misuse of the stolen data. As a precaution, affected individuals have been offered complimentary credit monitoring, identity theft protection, and identity theft resolution services. Keenan & Associates did not publicly disclose the names of the affected clients, so it is unclear at this stage whether the breach is reportable under the Health Insurance Portability and Accountability Act.
The post Keenan & Associates Data Breach Affects More Than 1.5 Million Individuals appeared first on HIPAA Journal.