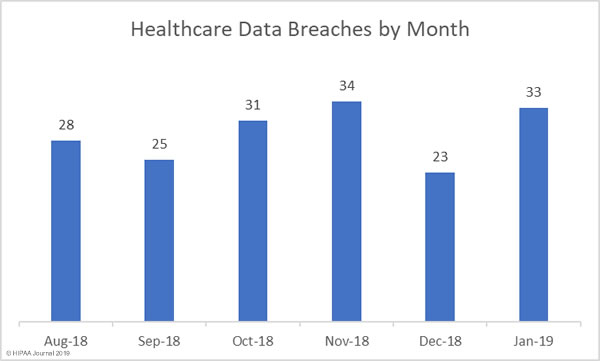
After a relatively quiet month for healthcare data breaches, breach numbers rose to more typical levels and were reported at a rate of more than one per day. There were 33 healthcare data breaches reported in January 2019.
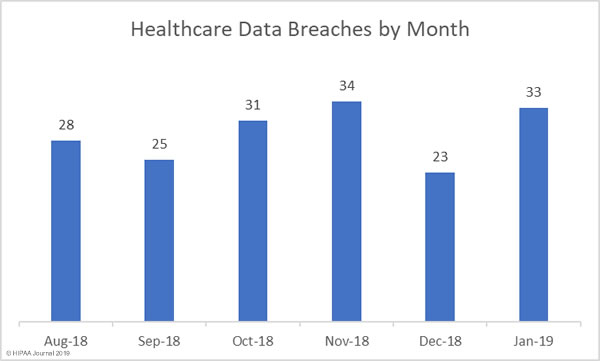
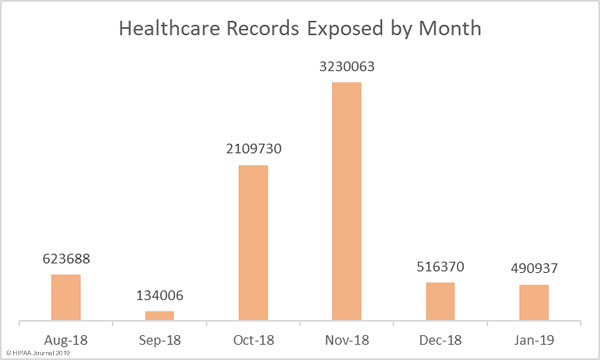
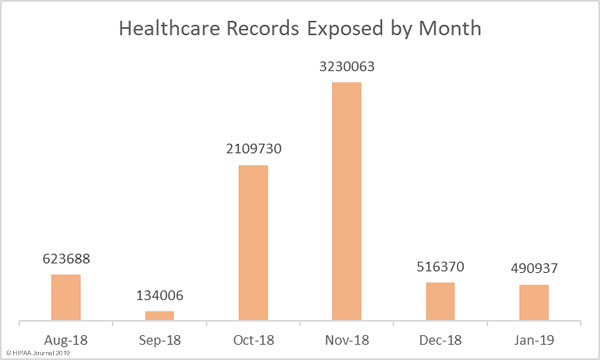
January was the second successive month where there was a fall in the number of individuals impacted by healthcare data breaches. January’s healthcare data breaches saw 490,937 healthcare records exposed, stolen or impermissibly disclosed.
Largest Healthcare Data Breaches in January 2019
| Rank |
Name of Covered Entity |
Covered Entity Type |
Individuals Affected |
Type of Breach |
| 1 |
Centerstone Insurance and Financial Services (BenefitMall) |
Business Associate |
111589 |
Hacking/IT Incident |
| 2 |
Las Colinas Orthopedic Surgery & Sports Medicine, PA |
Healthcare Provider |
76000 |
Theft |
| 3 |
Valley Hope Association |
Healthcare Provider |
70799 |
Hacking/IT Incident |
| 4 |
Roper St. Francis Healthcare |
Healthcare Provider |
35253 |
Hacking/IT Incident |
| 5 |
Managed Health Services |
Health Plan |
31300 |
Hacking/IT Incident |
| 6 |
EyeSouth Partners |
Business Associate |
24113 |
Hacking/IT Incident |
| 7 |
Dr. DeLuca Dr. Marciano & Associates, P.C. |
Healthcare Provider |
23578 |
Hacking/IT Incident |
| 8 |
Critical Care, Pulmonary and Sleep Associates, PLLP |
Healthcare Provider |
23377 |
Hacking/IT Incident |
| 9 |
Valley Professionals Community Health Center |
Healthcare Provider |
12029 |
Hacking/IT Incident |
| 10 |
Cambridge Healthcare Services, LLC |
Business Associate |
10866 |
Theft |
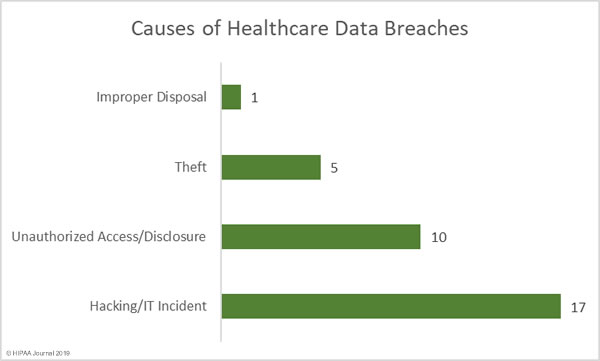
Causes of January 2018 Healthcare Data Breaches
Hacking and other IT security incidents such as ransomware and malware attacks were the biggest cause of healthcare data breaches in January 2019, accounting for 51.52% of the month’s data breaches (917 incidents) and the largest reported breach of the month. Hacking/IT incidents also accounted for the most breached records: 74.07% of all breached records in January (363,631 records).
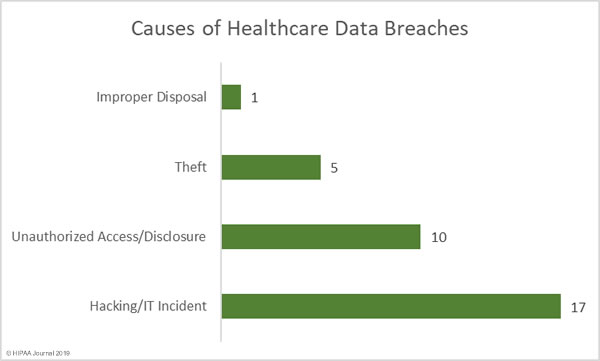
Unauthorized access and impermissible disclosure incidents were in second place with 10 incidents (30.30%), although they involved only a small percentage of the month’s breached records – 19,500 or 3.97% of the month’s total.
There were 5 theft incidents reported in January which involved the protected health information of 106,006 individuals – 21.59% of the records exposed in January – and one improper disposal incident that saw 1,800 paper records accidentally discarded with regular trash.
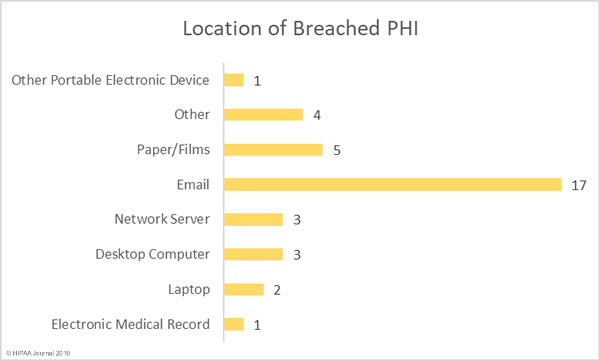
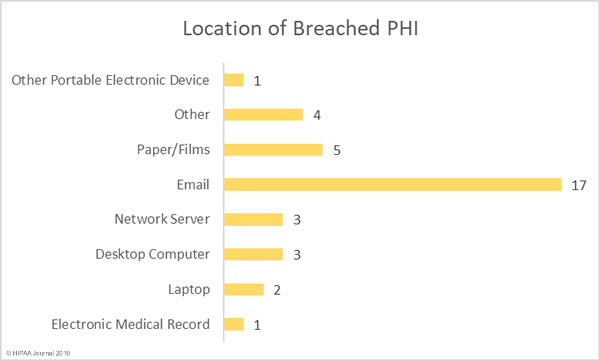
Location of Breached Protected Health Information
Healthcare organizations are still having difficulty preventing phishing attacks and other email-related breaches. As has been the case in the past few months, email-related data breaches have dominated the breach reports. Most of the email breaches in January were due to phishing attacks.
51.52% of healthcare data breaches in January 2019 involved PHI stored in emails and email attachments (17 incidents). Physical PHI, such as paper records, charts, and films was exposed in 15.15% of breaches in January (5 incidents).
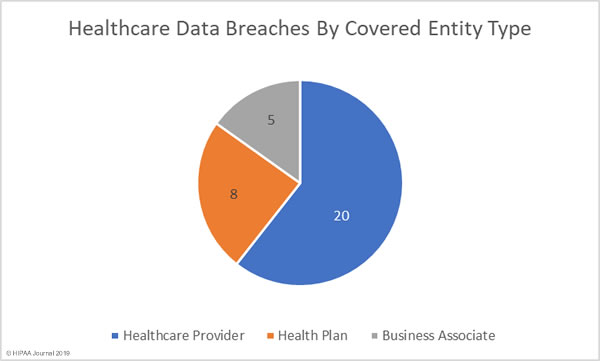
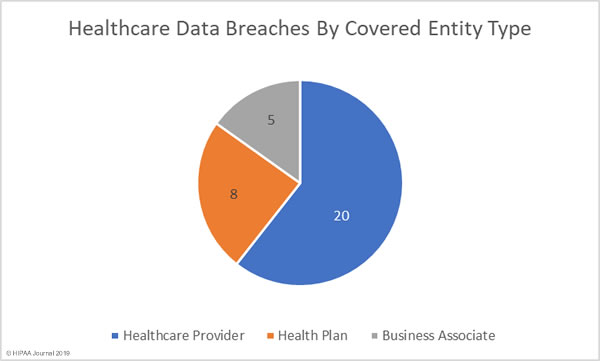
Healthcare Data Breaches by Covered Entity Type
Healthcare providers were the worst affected by healthcare data breaches in January 2019 with 20 reported incidents, six of which ranked in the top ten breaches of the month.
8 health plans reported breaches in January and there were five breaches reported by business associates of HIPAA-covered entities, including the largest data breach of the month. A further 6 data breaches had some business associate involvement but were reported by the HIPAA-covered entity.
Healthcare Data Breaches by State
HIPAA covered entities and business associates based in 20 different states reported healthcare data breaches in January 2019. The worst affected state was Texas with four reported breaches. Georgia, Indiana, and Kentucky each had 3 breaches in January and there were two breaches reported in each of California, Connecticut, Florida, Kansas.
Colorado, Illinois, Michigan, Minnesota, North Carolina, Nebraska, New Jersey, Pennsylvania, Rhode Island, South Carolina, Tennessee, and Washington each experienced one healthcare data breach in January.
Penalties for Noncompliance and HIPAA Violations
The Department of Health and Human Services’ Office for Civil Rights (OCR) did not issue any financial penalties in January 2019 or agree to any settlements to resolve HIPAA violations; however, OCR did announce in late January that a further settlement had been agreed with a HIPAA covered entity in December 2018 – Too late for inclusion in our December 2018 Healthcare Data Breach Report.
In December 2018, Cottage Health agreed to settle its HIPAA violation case with OCR for $3,000,000. OCR investigated Cottage Health over two breaches experienced in 2013 and 2015 which saw the protected health information of 62,500 patients exposed online.
OCR also announced that 2018 had been a record year for HIPAA enforcement. OCR’s HIPAA fines and settlements totaled $28,683,400 in 2018, beating the previous record of $23,505,300 set in 2016 by 22%. 2018 also saw the largest ever HIPAA settlement agreed. Anthem Inc., agreed to pay OCR $16,000,000 to resolve HIPAA violations discovered during the investigation of its 78.8 million-record data breach of 2015.
OCR closed out 2018 with 10 settlements to resolve HIPAA violations and one civil monetary penalty, beating last year’s total by one.
There was one HIPAA violation case closed by a state attorney general in January 2019. The California Attorney General agreed to settle a case with health insurer Aetna for $935,000. The financial penalty resolved violations of HIPAA and state laws that contributed to the impermissible disclosure of plan members’ PHI. In two separate 2017 mailings, PHI was visible through the windows of envelopes. The mailings were sent to individuals who had been diagnosed with Afib in one mailing, and patients who were receiving HIV medications in the other. The impermissible disclosures affected 1,991 California residents.
This was the sixth state attorney general financial penalty Aetna has agreed to pay in relation to the mailing errors. In 2018, Aetna settled cases with New York, New Jersey, Washington, Connecticut, and the District of Columbia. The latest financial penalty brings the total financial penalties over the HIPAA violations to $2,725,172.
The post January 2019 Healthcare Data Breach Report appeared first on HIPAA Journal.