The first three months of 2018 have seen 77 healthcare data breaches reported to the Department of Health and Human Services’ Office for Civil Rights (OCR). Those breaches have impacted more than one million patients and health plan members – Almost twice the number of individuals that were impacted by healthcare data breaches in Q4, 2017.
There was a 10.5% fall in the number of data breaches reported quarter over quarter, but the severity of breaches increased. The mean breach size increased by 130.57% and there was a 15.37% increase in the median breach size.
In Q4, 2017, the mean breach size was 6,048 healthcare records and the median breach size was 1,666 records. In Q1, 2018, the mean breach size was 13,945 records and the median breach size was 1,922 records.
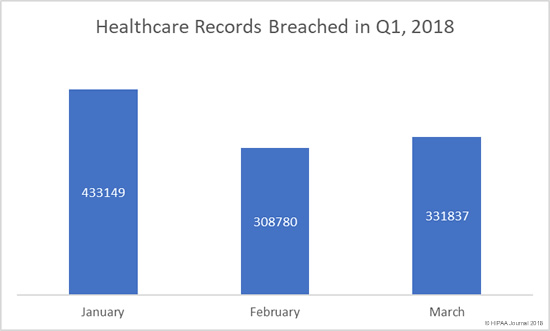
Between January 1 and March 31, 2018, 1,073,766 individuals had their PHI exposed, viewed, or stolen compared to 520,141 individuals in Q4, 2017.
Individuals Impacted by Healthcare Data Breaches in Q1, 2018
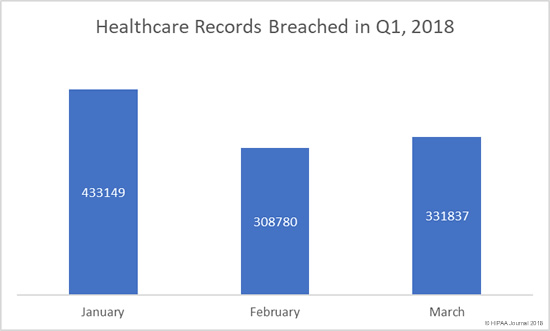
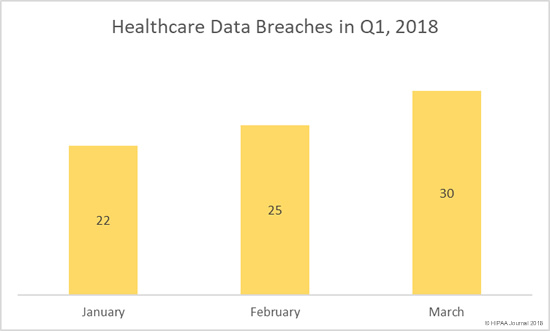
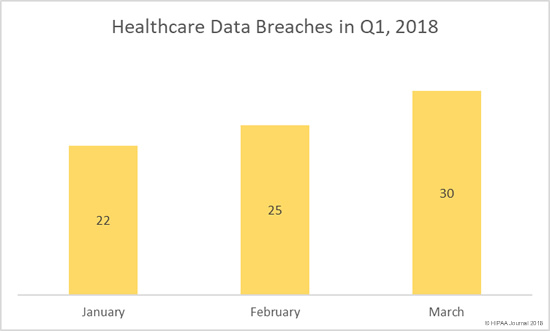
Throughout 2017, healthcare data breaches were occurring at a rate of more than one per day. Compared to 2017, January was a relatively good month for the healthcare industry, with just 22 security incidents reported to the HHS’ Office for Civil Rights.
However, January also saw the largest healthcare data breach of the quarter reported – A hacking incident that potentially resulted in the theft of almost 280,000 records. That incident made January the worst month in terms of the number of healthcare records exposed.
The number of reported data breaches also increased each month, In March, breaches were being reported at the typical rate of one per day.
Q1, 2018 Healthcare Data Breaches
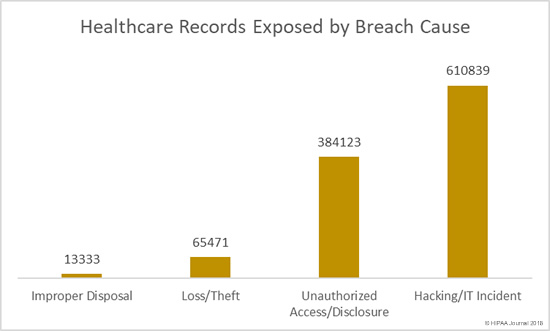
Main Causes of Healthcare Data Breaches in Q1, 2018
The healthcare industry is something of an anomaly when it comes to data breaches. In other industries, hacking/IT incidents dominate the breach reports; however, the healthcare industry is unique as insiders cause the most data breaches.
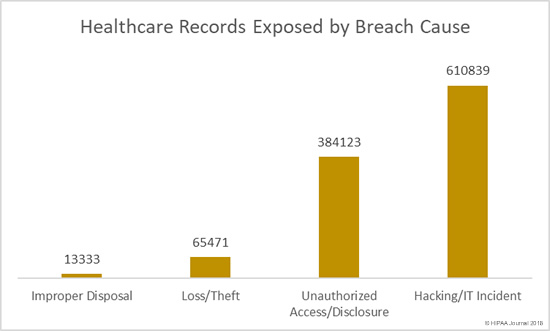
Once again, insiders were behind the majority of breaches. Unauthorized access/disclosure incidents, loss of physical records and devices containing ePHI, and improper disposal incidents accounted for 59.74% of the 77 breaches reported in Q1.
The main cause of breaches in Q1, 2018 was unauthorized access/disclosures – 35 incidents and 45.45% of the total breaches reported in Q1. There were 15 breaches involving the loss or theft of electronic devices containing ePHI, all of which could have been prevented had encryption been used.

Healthcare Records Exposed in Q1, 2018 by Breach Cause
Unauthorized access/disclosure incidents were more numerous than hacking incidents in Q1, although more healthcare records were exposed/stolen in hacking/IT incidents than all other causes of breaches combined.
Location of Breached PHI in Q1, 2018
Healthcare security teams may be focused on securing the perimeter and preventing hackers from accessing and stealing electronic health information, but it is important not to neglect physical records. As was the case in Q4, 2017, physical records were the top location of breached PHI in Q1, 2018.
Email, which includes social engineering, phishing attacks and misdirected emails, was the second most common location of breached PHI followed by network servers.

Largest Healthcare Data Breaches of Q1, 2018
In Q1, 2018, there were 18 healthcare security breaches that impacted more than 10,000 individuals. Hacking/IT incidents tend to involve more records than any other breach cause, although in Q1, 2018, there were several large-scale unauthorized access/disclosure incidents, including five of the top ten breaches of the quarter.
The two largest breaches of the year to date affected Oklahoma State University Center for Health Sciences and St. Peter’s Surgery & Endoscopy Center. In both cases a hacker gained access to the network and potentially viewed/obtained patients’ PHI.
The five largest breaches of the quarter accounted for 57% of all records exposed in the quarter. The top 18 data breaches accounted for 87% of all records exposed in the quarter.
| Name of Covered Entity |
Covered Entity Type |
Individuals Affected |
Type of Breach |
| Oklahoma State University Center for Health Sciences |
Healthcare Provider |
279865 |
Hacking/IT Incident |
| St. Peter’s Surgery & Endoscopy Center |
Healthcare Provider |
134512 |
Hacking/IT Incident |
| Tufts Associated Health Maintenance Organization, Inc. |
Health Plan |
70320 |
Unauthorized Access/Disclosure |
| Florida Agency Persons for Disabilities |
Health Plan |
63627 |
Unauthorized Access/Disclosure |
| Middletown Medical P.C. |
Healthcare Provider |
63551 |
Unauthorized Access/Disclosure |
| Onco360 and CareMed Specialty Pharmacy |
Healthcare Provider |
53173 |
Hacking/IT Incident |
| Triple-S Advantage, Inc. |
Health Plan |
36305 |
Unauthorized Access/Disclosure |
| ATI Holdings, LLC and its subsidiaries |
Healthcare Provider |
35136 |
Hacking/IT Incident |
| City of Houston Medical Plan |
Health Plan |
34637 |
Theft |
| Mississippi State Department of Health |
Healthcare Provider |
30799 |
Unauthorized Access/Disclosure |
| Agency for Health Care Administration |
Health Plan |
30000 |
Hacking/IT Incident |
| Decatur County General Hospital |
Healthcare Provider |
24000 |
Hacking/IT Incident |
| Barnes-Jewish Hospital |
Healthcare Provider |
18436 |
Unauthorized Access/Disclosure |
| Barnes-Jewish St. Peters Hospital |
Healthcare Provider |
15046 |
Unauthorized Access/Disclosure |
| Special Agents Mutual Benefit Association |
Health Plan |
13942 |
Unauthorized Access/Disclosure |
| Guardian Pharmacy of Jacksonville |
Healthcare Provider |
11521 |
Hacking/IT Incident |
| CarePlus Health Plan |
Health Plan |
11248 |
Unauthorized Access/Disclosure |
| Primary Health Care, Inc. |
Healthcare Provider |
10313 |
Unauthorized Access/Disclosure |
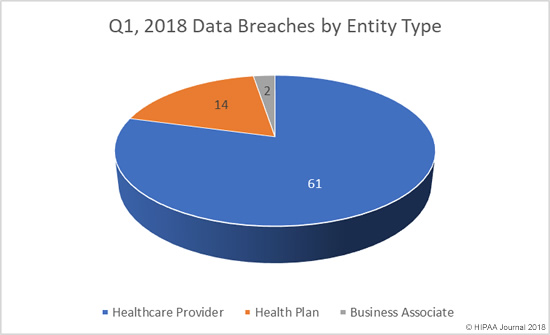
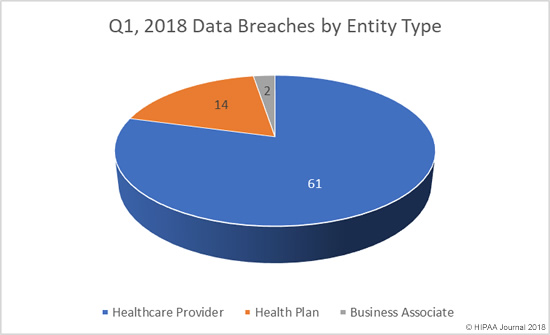
Healthcare Data Breaches in Q1, 2018 by Covered Entity
Healthcare providers were the worst affected by healthcare data breaches in Q1, 2018. As was the case in Q4, 2017, 14 health plans experienced a breach of more than 500 records. There were half the number of business associate breaches in Q1, 2018 as there were in Q4, 2017.
Healthcare Data Breaches in Q1, 2018 by State
In Q1, healthcare organizations based in 35 states reported breaches of more than 500 records. The worst affected state was California with 11 reported breaches, followed by Massachusetts with 8 security incidents.
There were four security incidents in both Missouri and New York, and three breaches reported by healthcare organizations based in Florida, Illinois, Maryland, Mississippi, Tennessee, and Wisconsin.
Healthcare organizations based in Alabama, Arkansas, Kentucky, Rhode Island, Texas, and Wyoming reported two breaches.
There was one breach experienced in Colorado, Connecticut, District of Columbia, Georgia, Iowa, Maine, Michigan, Minnesota, North Carolina, New Jersey, New Mexico, Nevada, Ohio, Oklahoma, Pennsylvania, Utah, Virginia, Washington and West Virginia.
The post Report: Healthcare Data Breaches in Q1, 2018 appeared first on HIPAA Journal.