There has been a month-over-month increase in healthcare data breaches. In March 2018, 29 security incidents were reported by HIPAA covered entities compared to 25 incidents in February.

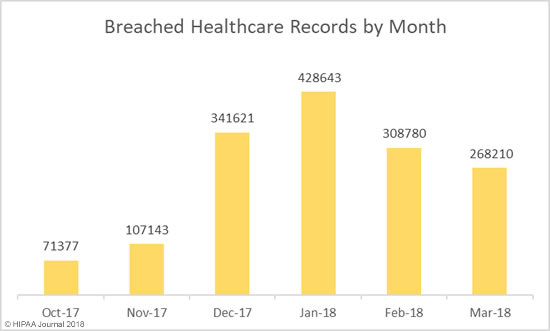
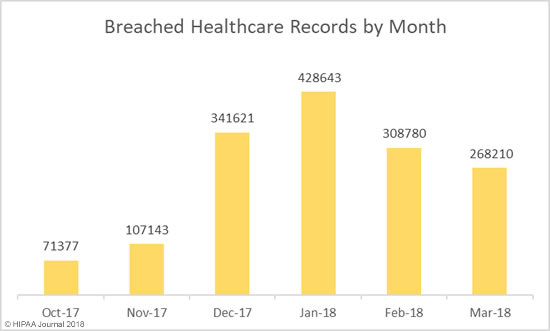
Even though more data breaches were reported in March, there was a fall in the number of individuals impacted by breaches. March 2018 healthcare data breaches saw 268,210 healthcare records exposed – a 13.13% decrease from the 308,780 records exposed in incidents in February.
Causes of March 2018 Healthcare Data Breaches
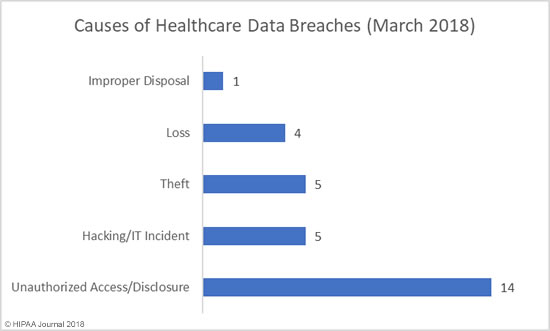
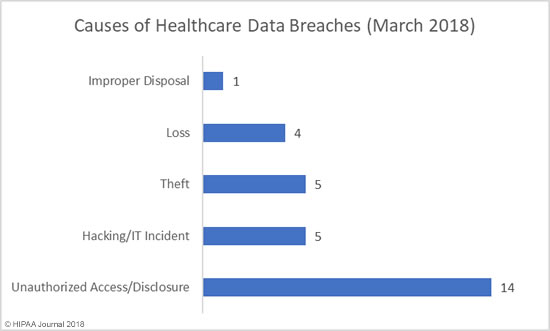
March saw the publication of the Verizon Data Breach Investigations Report which confirmed the healthcare industry is the only vertical where more data breaches are caused by insiders than hackers. That trend continued in March. Unauthorized access/disclosures, loss of devices/records, and improper disposal incidents were behind 19 of the 29 incidents reported – 65.5% of all incidents reported in March.
The main cause of healthcare data breaches in March 2018 was unauthorized access/disclosure incidents. 14 incidents were reported, with theft/loss incidents the second main cause with 9 incidents, followed by hacking/IT incidents with 5 breaches reported.
Severity of Breaches by Breach Cause
| Breach Cause |
Total Records Exposed in March |
Median Records Exposed |
Mean Records Exposed |
| Unauthorized Access/Disclosure |
166,859 |
3,551 |
11,919 |
| Hacking/IT Incident |
54,814 |
5,207 |
10,963 |
| Theft |
40,018 |
1,424 |
8,004 |
| Loss |
5,107 |
1,096 |
1,277 |
| Improper Disposal |
1,412 |
1,412 |
1,412 |
Largest Healthcare Data Breaches Reported in March 2018
There were ten healthcare data breaches reported in March that impacted more than 10,000 individuals. The largest data breach resulted in the exposure of 63,551 individuals’ PHI. That incident occurred and was discovered in December 2016, although the incident has only just been reported to the HHS’ Office for Civil Rights.
While hacking incidents usually result in the highest number of exposed/compromised records, in March it was unauthorized access/disclosure incidents that dominated the breach reports.
| Name of Covered Entity |
Covered Entity Type |
Individuals Affected |
Type of Breach |
| Middletown Medical P.C. |
Healthcare Provider |
63,551 |
Unauthorized Access/Disclosure |
| ATI Holdings, LLC and its subsidiaries |
Healthcare Provider |
35,136 |
Hacking/IT Incident |
| City of Houston Medical Plan |
Health Plan |
34,637 |
Theft |
| Mississippi State Department of Health |
Healthcare Provider |
30,799 |
Unauthorized Access/Disclosure |
| Barnes-Jewish Hospital |
Healthcare Provider |
18,436 |
Unauthorized Access/Disclosure |
| Barnes-Jewish St. Peters Hospital |
Healthcare Provider |
15,046 |
Unauthorized Access/Disclosure |
| Special Agents Mutual Benefit Association |
Health Plan |
13,942 |
Unauthorized Access/Disclosure |
| Guardian Pharmacy of Jacksonville |
Healthcare Provider |
11,521 |
Hacking/IT Incident |
| Primary Health Care, Inc. |
Healthcare Provider |
10,313 |
Unauthorized Access/Disclosure |
March 2018 Healthcare Data Breaches by Covered Entity Type
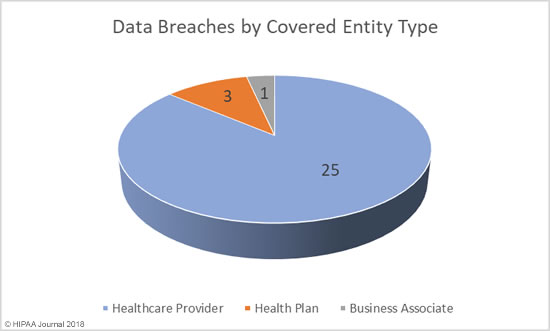
No data breaches were reported by business associates of HIPAA-covered entities in March. The breach summaries published by the HHS’ Office for Civil Rights suggest there was no business associate involvement in any of the 29 incidents reported.
However, the largest reported incident – the breach at Middletown Medical – is marked as having no business associate involvement, when the breach notice uploaded to the provider’s website indicates the incident was caused by a subcontractor of a business associate. It is possible there were more security breaches in March that had some business associate involvement.
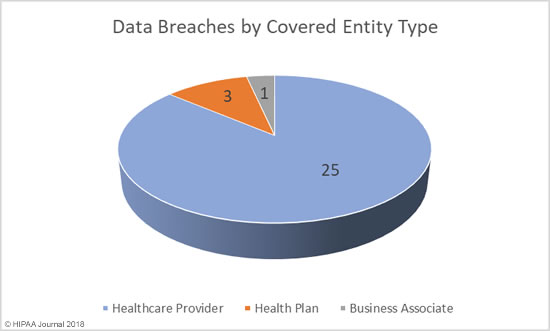
Records Exposed by Covered Entity Type
Unsurprisingly, given the number of incidents reported by healthcare providers, these incidents resulted in the highest number of exposed records – 154,325 records – followed by breaches at business associates/subcontractors – 63,551 records – and health plans – 50,334 records.
Breaches at business associates/subcontractors saw the highest number of records exposed per incident (Median & Mean = 63,551 records), followed by health plans (Median=13,943 records / Mean = 16,778 records), and healthcare providers (Median = 1,843 records / Mean = 6,173 records).
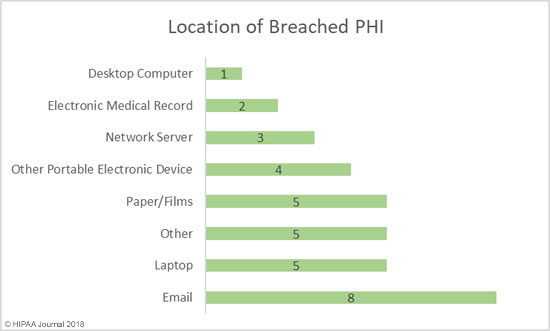
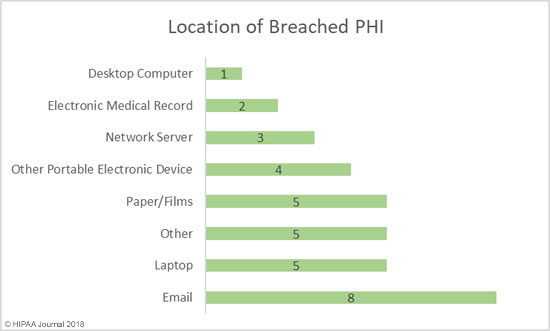
Location of Breached Protected Health Information
The main location of breached protected health information in March was portable electronic devices (laptops /other portable devices) with 9 incidents reported. Had encryption been used to protect ePHI on these devices, a breach of PHI could have easily been avoided.
The second biggest problem area was email with 8 reported incidents. These breaches include misdirected emails and phishing incidents.
Securing physical records continues to be a problem. There were five incidents reported in March that involved physical records such as paper and films.
March 2018 Healthcare Data Breaches by State
In March 2018, six states experienced multiple healthcare data breaches. While California usually tops the list for the most number of breaches, this month it was Massachusetts-based healthcare organizations that were the hardest hit, with 5 incidents reported.
California was in second place with four security incidents, followed by Missouri and New York with three, and Maryland and Texas with two. The 10 other states where breaches occurred were Arkansas, Colorado, District of Columbia, Florida, Georgia, Iowa, Illinois, Minnesota, Mississippi, and West Virginia.
Financial Penalties for Breaches and HIPAA Violations
There were no civil monetary penalties issued by the Department of Health and Human Services’ Office for Civil Rights in March, and no settlements with HIPAA-covered entities or business associates to resolve HIPAA violations.
The New York attorney general’s office has continued to take a hard line on companies discovered to have violated HIPAA Rules and suffered data breaches as a result with one further settlement reached in March.
Virtua Medical Group agreed to settle violations of HIPAA and state laws for $417,816. That penalty relates to the failure to secure an FTP server, although it was not the healthcare provider that was directly responsible. The error was made by a business associate of Virtua Medical Group.
The post Analysis of March 2018 Healthcare Data Breaches appeared first on HIPAA Journal.