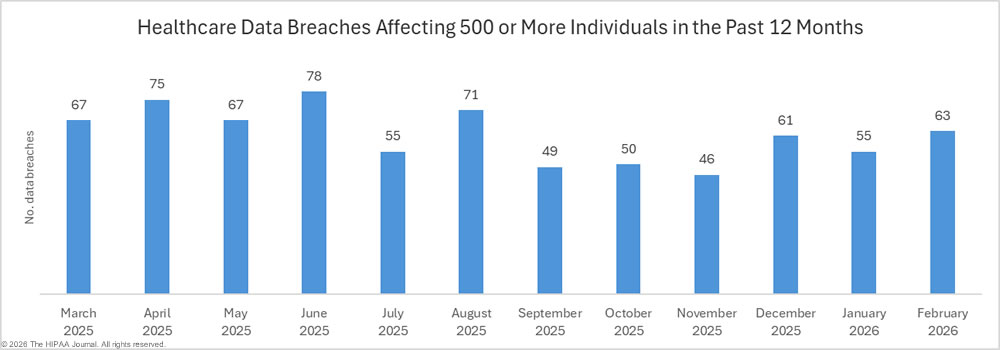
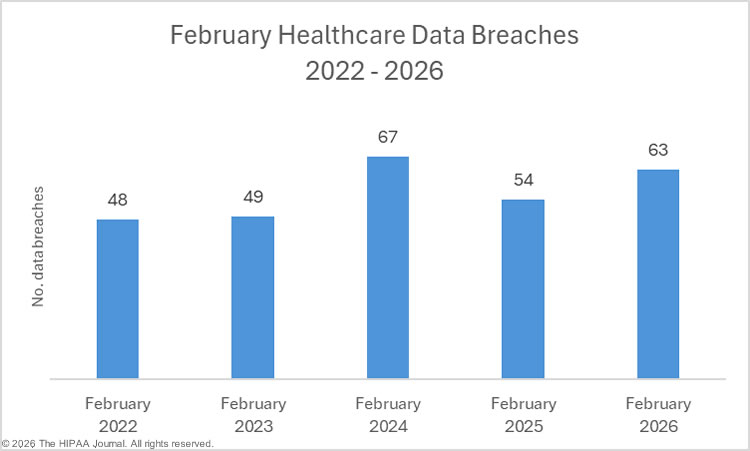
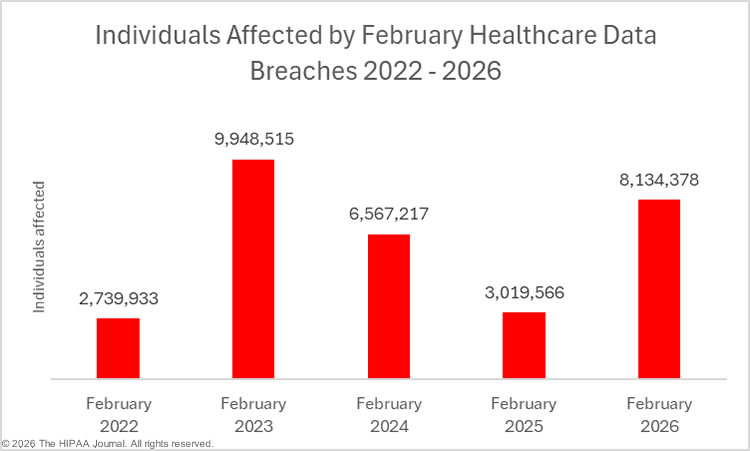
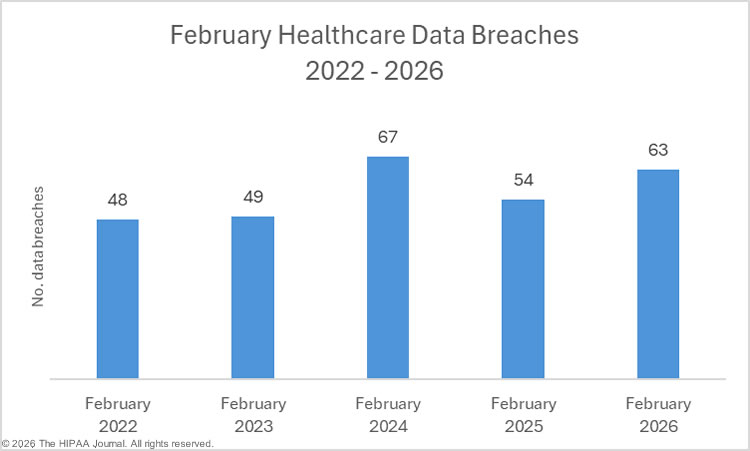
In February 2026, 63 data breaches were reported to the Department of Health and Human Services (HHS) Office for Civil Rights (OCR) that affected 500 or more individuals, a 14.5% increase from January 2026, and 12.5% more than the average number of February data breaches over the past 5 years.
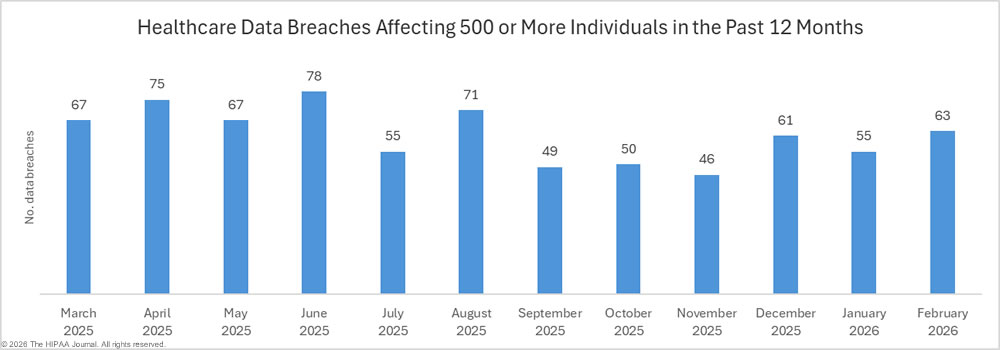
Between January 1 and February 28, 2026, 118 data breaches affecting 500 or more individuals have been reported to OCR, involving the protected health information of 9,651,076 individuals. While healthcare data breaches have declined 10.6% year-over-year, the number of individuals affected has increased 44.7%.
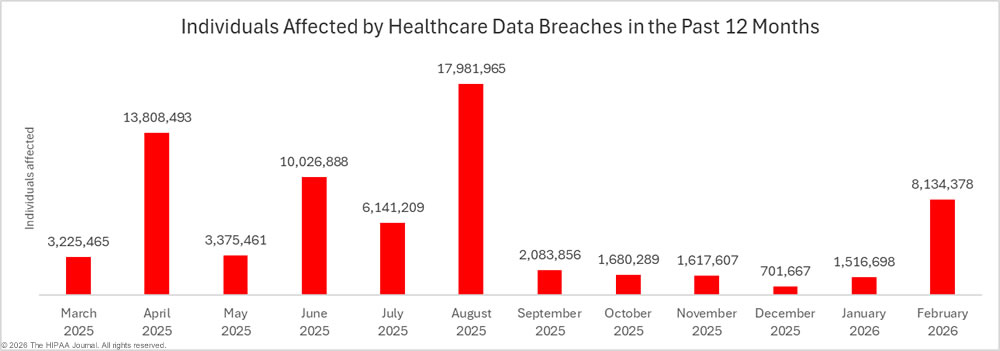
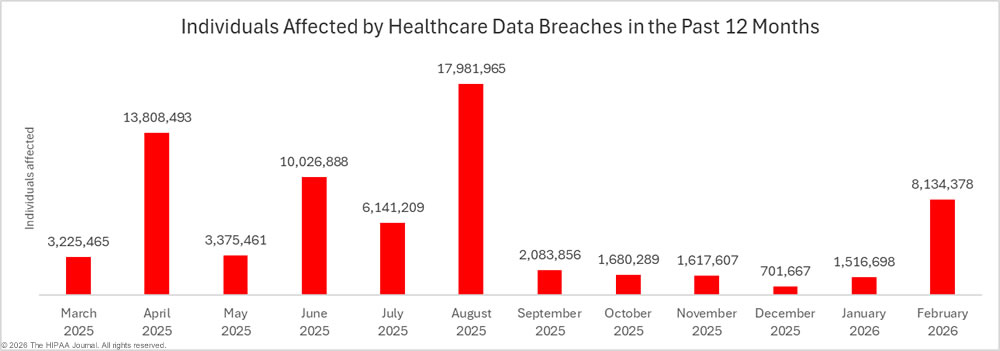
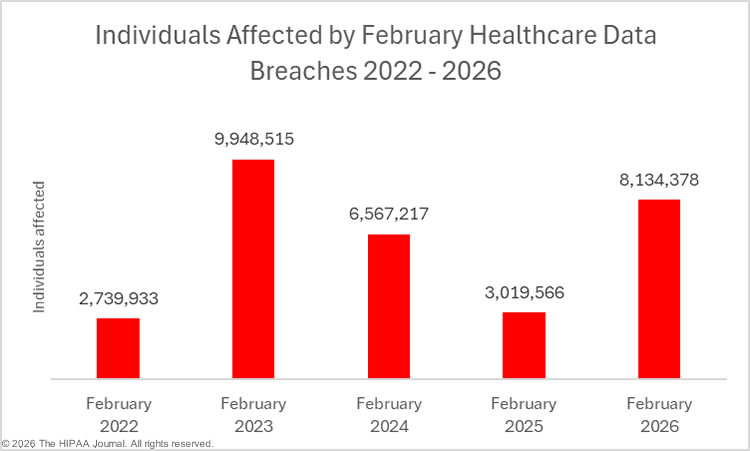
Across the 63 data breaches reported in February, the protected health information of at least 8,134,378 individuals was exposed or impermissibly disclosed, a 436% month-over-month increase and 38.9% more than the average number of affected individuals over the past 12 months.
Biggest Healthcare Data Breaches in February 2026
The high total in February is due to massive data breaches at two HIPAA-regulated entities in February – TriZetto Provider Solutions, a provider of administrative services to healthcare providers and health plans, and QualDerm Partners, a healthcare management services provider to 158 healthcare practices in 17 states. Both incidents potentially involved unauthorized access to the protected health information of more than 3 million individuals.
TriZetto is a business associate of many HIPAA-covered entities and was a subcontractor used by the healthcare technology and data analytics company OCHIN, a provider of specialized electronic health record software to healthcare providers. OCHIN said the breach impacted around 9% of the patient population of its member network – around 700,000 patients. It is unclear how many healthcare organizations were affected in total by the TRiZetto data breach. The HIPAA Journal has tracked 44 HIPAA-covered entities that have announced that they were affected, although the total is undoubtedly higher. Hackers gained access to the web portal that TriZetto’s clients used to access TriZetto’s systems. The intrusion was detected in October 2025; however, the threat actor had access to its systems for almost a year. It is unclear which threat group was behind the breach, as it was not disclosed by TriZetto, and no group appears to have claimed responsibility for the breach.
The data breach at QualDerm Partners was of a similar scale, affecting more than 3.1 million individuals. The intrusion was detected in December 2025, and the investigation confirmed that hackers had access to its systems between December 23 and December 24, 2025, and exfiltrated protected health information. As with the data breach at TriZetto, the threat actor behind the incident is unknown. While on a much smaller scale, the data breach at ApolloMD Business Services affected many healthcare provider clients. The ransomware group Qilin claimed responsibility for the attack and claimed to have exfiltrated patient data. While the data breach was reported in February, it was detected in May 2025. More individuals were affected by those three data breaches alone than in all data breaches reported to OCR since mid September 2025.
| HIPAA-Regulated Entity |
State |
Entity Type |
Individuals Affected |
Cause of Breach |
| TriZetto Provider Solutions |
MO |
Business Associate |
3,433,965 |
Hacking incident |
| QualDerm Partners, LLC |
TN |
Healthcare Provider |
3,117,874 |
Hacking incident – data theft confirmed |
| ApolloMD Business Services, LLC |
GA |
Business Associate |
626,540 |
Ransomware attack (Qilin) |
| Vikor Scientific, LLC. |
SC |
Healthcare Provider |
139,964 |
Network server hacking incident – OCR provided technical assistance on HIPAA compliance |
| IPPC Inc., IPPC of New York LLC, and Innovative Pharmacy LLC |
NJ |
Healthcare Provider |
133,862 |
Hacking incident – data theft confirmed |
| Oscar Health |
NY |
Health Plan |
91,350 |
Employee emailed ePHI to incorrect recipients – OCR provided technical assistance on HIPAA compliance |
| National Association on Drug Abuse Problems |
NY |
Healthcare Provider |
90,000 |
Hacking incident |
| Counseling Center of Wayne & Holmes Counties |
OH |
Healthcare Provider |
83,354 |
Hacking incident – data theft confirmed |
| Academic Urology & Urogynecology of Arizona |
AZ |
Healthcare Provider |
73,281 |
Hacking incident |
| Lakeside Pediatrics & Adolescent Medicine, PLLC |
ID |
Healthcare Provider |
34,154 |
Hacking incident |
| Emanuel Medical Center |
GA |
Healthcare Provider |
28,963 |
Hacking incident |
| Advanced Homecare Management, LLC DBA Enhabit Home Health & Hospice |
TX |
Healthcare Provider |
23,154 |
Hacking incident at a business associate |
| Cedar Point Health, LLC |
CO |
Healthcare Provider |
23,114 |
Hacking incident |
| WIRX Pharmacy |
PA |
Healthcare Provider |
20,047 |
Hacking incident |
| Wendy Foster OD |
KS |
Healthcare Provider |
20,000 |
Hacking incident |
| AccentCare |
TX |
Healthcare Provider |
19,772 |
Hacking incident at a business associate (Doctor Alliance) involving a web application |
| Communications Workers of America Local 1180 Security Benefits Fund |
NY |
Health Plan |
18,550 |
Unauthorized access to electronic medical records at a business associate |
| EyeCare Partners, LLC, including The Ophthalmology Group, Ophthalmology Consultants, and Ophthalmology Associates. |
MO |
Healthcare Provider |
17,110 |
Unauthorized access to employee email accounts |
| Manhattan Retirement Foundation d/b/a Meadowlark Hills |
KS |
Healthcare Provider |
14,442 |
Ransomware attack (Beast) – data theft confirmed |
| Jackson Hospital and Clinic |
AL |
Healthcare Provider |
13,910 |
Hacking incident at a business associate |
| Couve Healthcare Consulting, LLC DBA Evergreen Healthcare Group |
WA |
Business Associate |
11,795 |
Hacking incident involving its cloud-based electronic medical records |
| Triad Radiology Associates |
NC |
Healthcare Provider |
11,011 |
Unauthorized access to an employee’s email account |
Under the HIPAA Breach Notification Rule, data breaches must be reported to OCR within 60 days of the discovery of a data breach. When the number of affected individuals is not known, an estimate should be provided to OCR. Many regulated entities choose to report a breach using a placeholder figure of 500 or 501 individuals in such cases. The breach data for February 2026 includes 7 such data breaches. These figures are usually, but not always, updated when data breach investigations/data reviews are completed.
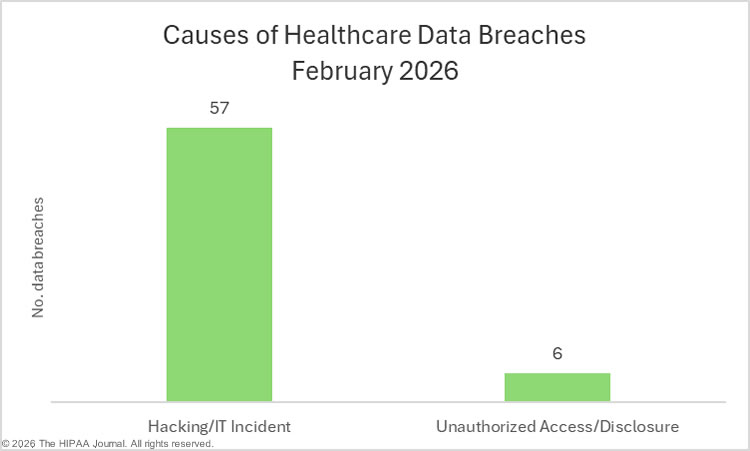
Causes of February 2026 Healthcare Data Breaches
Hacking and other IT incidents continue to be the leading cause of healthcare data breaches, as has been the case for many years. All but 6 of the data breaches in February were hacking/IT incidents, which accounted for 98.6% of all individuals affected in the February 2026 data set. Across the 57 hacking-related data breaches, 8,020,208 individuals were affected. The average breach size was 140,705 individuals, and the median breach size was 2,908 individuals.
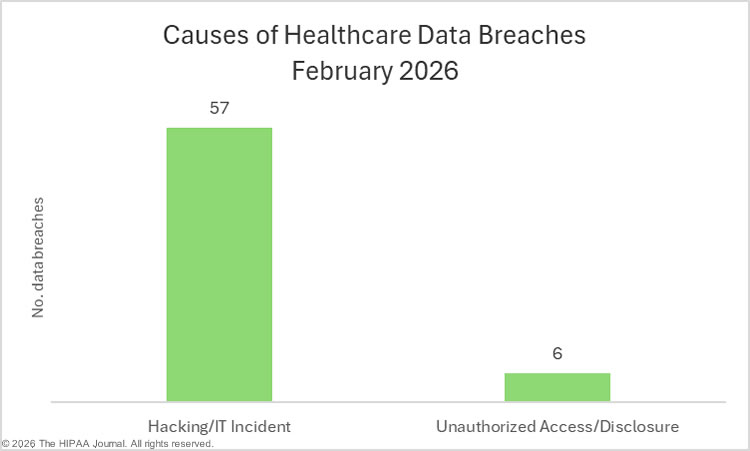
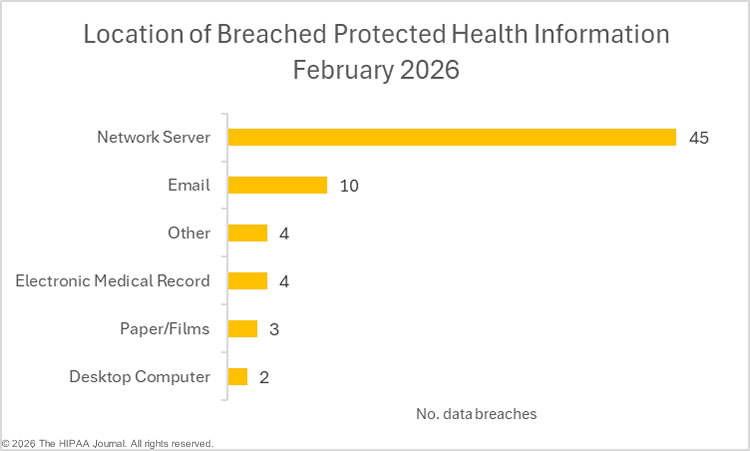
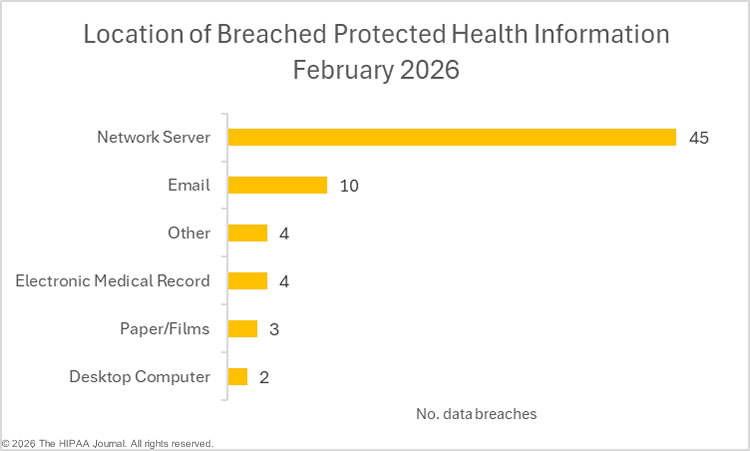
The remaining 6 data breaches were unauthorized access/disclosure incidents, which affected 114,170 individuals. The average breach size was 19,028 individuals, and the median breach size was 1,560 individuals. The largest of these incidents affected more than 91,000 individuals and was the result of an employee emailing ePHI to an incorrect recipient. Loss and theft incidents were once one of the biggest causes of healthcare data breaches, but they are now rarely reported. There were no loss or theft incidents in February, nor any improper disposal incidents. The most common location of breached protected health information in February was network servers, followed by email accounts/disclosures.
February 2026 Data Breaches at HIPAA Regulated Entities
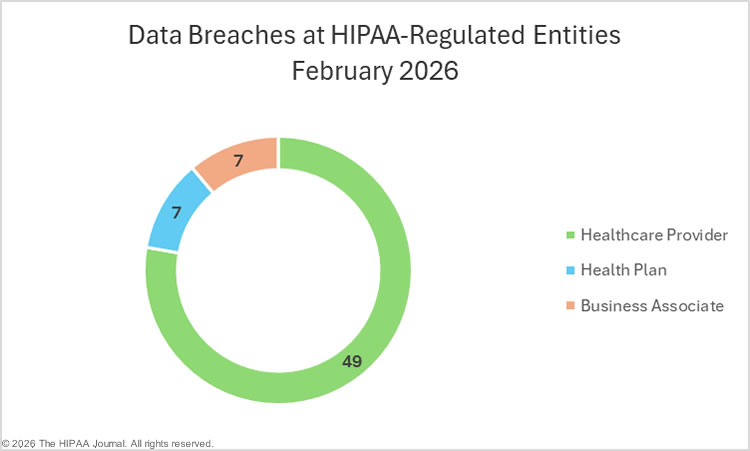
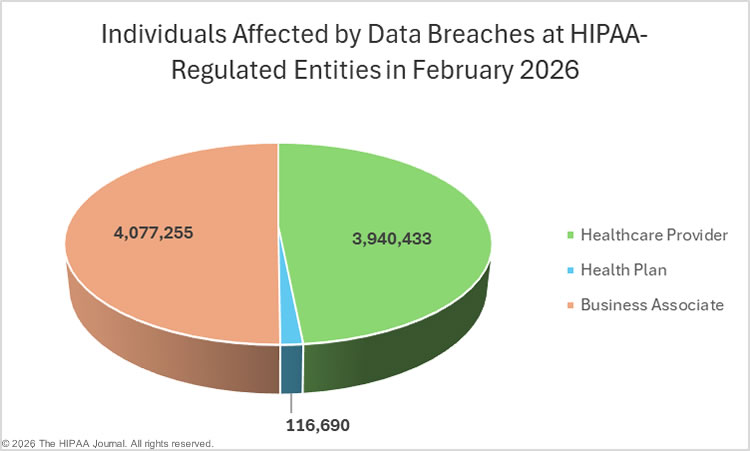
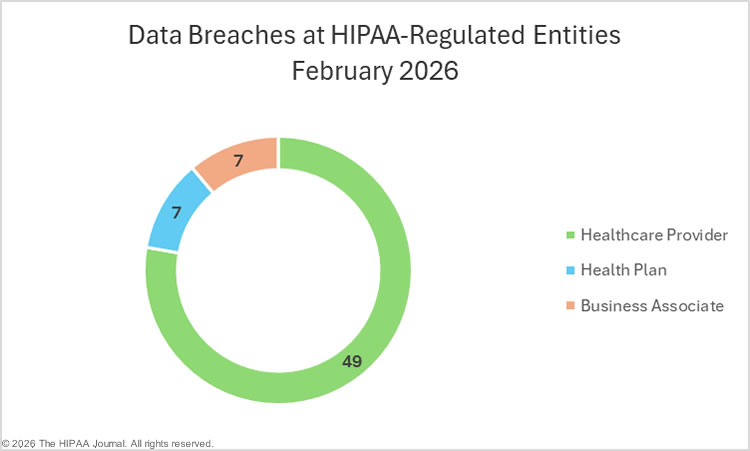
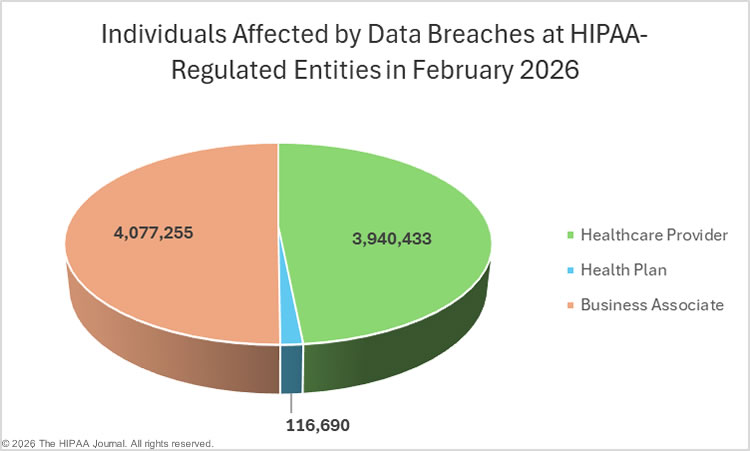
In February, data breaches involving the protected health information of 500 or more individuals were reported by 49 healthcare providers (3,940,433 individuals), 7 health plans (116,690 individuals), and 7 business associates (4,077,255 individuals). The raw data from the OCR breach portal shows the reporting entity rather than the entity that experienced the breach, as when a data breach occurs at a business associate, it is often the covered entity that reports the breach.
February serves as a good example of how business associate data breaches are often underrepresented in data breach reports. Recalculating the data based on the entity that experienced the data breach, 25 data breaches occurred at business associates. The data breach at Trizetto Provider Solutions was reported to OCR by Trizetto as affecting more than 3.4 million individuals; however, many of the affected entities reported the breach to OCR themselves. The charts below are based on the entity that experienced the data breach, rather than the entity that reported the data breach, to better reflect data breaches at business associates.
Geographical Distribution of February 2026 Healthcare Data Breaches
The data breaches reported to OCR in February were quite widely distributed, affecting entities in 32 U.S. states. New York and Texas topped the list with 6 data breaches in each state, with four data breaches reported by entities based in California.
| State |
Breaches |
| New York & Texas |
6 |
| California |
4 |
| Georgia, Kansas & Oregon |
3 |
| Arkansas, Illinois, Kentucky, Michigan, Missouri, North Carolina, New Jersey, Oklahoma, Pennsylvania, South Carolina, Tennessee & Utah |
2 |
| Alabama, Arizona, Colorado, Florida, Idaho, Indiana, Massachusetts, Maryland, Maine, Minnesota, New Hampshire, Ohio, Virginia & Washington |
1 |
In terms of breach severity, Missouri and Tennessee topped the list for affected individuals.
| State |
Individuals Affected |
State |
Individuals Affected |
| Missouri |
3,451,075 |
North Carolina |
11,512 |
| Tennessee |
3,119,544 |
Maine |
9,300 |
| Georgia |
658,003 |
Kentucky |
8,972 |
| New York |
210,655 |
California |
6,283 |
| South Carolina |
140,465 |
Arkansas |
5,800 |
| New Jersey |
134,444 |
Oregon |
4,641 |
| Ohio |
83,354 |
Michigan |
4,473 |
| Arizona |
73,281 |
Indiana |
3,158 |
| Texas |
52,361 |
Illinois |
2,891 |
| Kansas |
35,769 |
Oklahoma |
2,275 |
| Idaho |
34,154 |
Virginia |
1,544 |
| Pennsylvania |
24,647 |
Florida |
1,107 |
| Colorado |
23,114 |
New Hampshire |
1,005 |
| Alabama |
13,910 |
Massachusetts |
634 |
| Utah |
12,085 |
Maryland |
626 |
| Washington |
11,795 |
Minnesota |
501 |
HIPAA Enforcement Activity in February 2026
There were no announcements about HIPAA enforcement actions by the HHS Office for Civil Rights or state attorneys general in February. OCR has confirmed, however, that its risk analysis enforcement initiative has been expanded to cover risk management. When investigating a data breach, OCR will request documentation demonstrating that a comprehensive, organization-wide risk analysis has been conducted and that risks identified by the risk analysis have been managed and reduced to a reasonable and acceptable level in a timely manner.
To help HIPAA-regulated entities manage risks and comply with the requirements of the HIPAA Security Rule, OCR released a video presentation this month. In the video, Nicholas Heesters, OCR’s Senior Advisor for Cybersecurity, explains the HIPAA requirements for risk management, provides examples of violations of the risk management implementation specification of the security management process standard that OCR discovered during its data breach investigations.
About this Report
The HIPAA Journal healthcare data breach reports are based on data breaches reported to the HHS’ Office for Civil Rights, as HIPAA-regulated entities rarely publicly disclose the number of individuals affected by a data breach, and in the case of hacking incidents, attackers’ claims are unreliable. Typically, the data breach reports are published around the 20th of each month for the preceding month; however, OCR has been slow to add data breaches to its data breach portal, hence the delay in publication.
OCR is delaying adding breach reports to the “under investigation” section of its data breach portal. For instance, no data breach reports submitted to OCR in March 2026 were added to the under investigation section of the breach portal in March 2026. As of April 10, 2026, there are only two data breaches listed for March. While the delay could indicate resource pressure at OCR, data breaches have been added to the “Archive” section of the OCR breach portal at a much-accelerated pace, indicating a change of priorities at OCR. OCR appears to be concentrating on investigating data breaches and closing investigations more quickly.
The post February 2026 Healthcare Data Breach Report appeared first on The HIPAA Journal.